Free Microsoft MS-700 Practice Test Questions MCQs
Stop wondering if you're ready. Our Microsoft MS-700 practice test is designed to identify your exact knowledge gaps. Validate your skills with Managing Microsoft Teams questions that mirror the real exam's format and difficulty. Build a personalized study plan based on your free MS-700 exam questions mcqs performance, focusing your effort where it matters most.
Targeted practice like this helps candidates feel significantly more prepared for Managing Microsoft Teams exam day.
23340+ already prepared
Updated On : 25-May-2026334 Questions
Managing Microsoft Teams
4.9/5.0
Topic 5: Misc, Questions
You have a Microsoft 365 subscription that uses Microsoft Teams. The subscription contains 1,000 users in the groups shown in the following table.
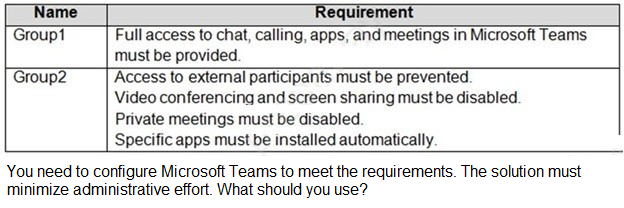
A. policy packages
B. app setup policies
C. Microsoft Teams policies
D. Meetings policies
Explanation:
The question requires applying two distinct sets of configurations to two different groups. Group1 needs full access to all features, while Group2 needs a restricted environment with specific apps installed. To minimize administrative effort, a solution that bundles multiple policy types into a single entity for easy assignment is ideal. Policy packages are designed for this exact scenario, allowing admins to apply a curated collection of settings to specific users or groups efficiently.
Correct Option:
A. Policy packages
Policy packages are a collection of pre-defined or custom policies and settings that can be assigned to users who have similar roles. In this scenario, creating one package for Group1 with policies that grant full access and another package for Group2 with restricted meeting policies, external access settings, and an app setup policy would meet all requirements. This approach bundles multiple policy types together, significantly reducing the administrative overhead of managing each policy type individually for each group.
Incorrect Option:
B. App setup policies
App setup policies are used to control which apps are pinned and automatically installed for users. While this would address the requirement for Group2 to have specific apps installed automatically, it would not fulfill the other requirements for Group2, such as disabling video conferencing, screen sharing, and private meetings. It would also not address any of the requirements for Group1. Therefore, using only app setup policies is an incomplete solution.
Incorrect Option:
C. Microsoft Teams policies
"Microsoft Teams policies" is a broad category encompassing various policy types like messaging, meeting, and calling policies. Using this as an answer is too vague and implies managing each policy type separately. While you could technically configure each required policy individually and assign them to the groups, this would involve creating and assigning multiple discrete policies. This process would require significantly more administrative effort compared to bundling them into a policy package.
Incorrect Option:
D. Meetings policies
Meeting policies control features available when users schedule or join meetings, such as screen sharing and private meetings. This would successfully address the parts of the requirement for Group2 related to disabling video conferencing, screen sharing, and private meetings. However, it would not address the need to automatically install specific apps for Group2, nor would it manage the full-access requirements for Group1. It is a single policy type and cannot cover all the needs outlined for both groups.
Reference:
Manage Teams with policy packages - Microsoft Teams | Microsoft Learn
Manage app setup policies in Microsoft Teams - Microsoft Teams | Microsoft Learn
Manage meeting policies in Microsoft Teams - Microsoft Teams | Microsoft Learn
Task 8
You need to enable shared channel collaboration with mkrosoft.com. The solution must meet the following requirements:
•Users must be able to participate in shared channels created by microsoft.com.
•Users must be able to invite Microsoft contacts to snared channels created by users at your company.
Explanation:
This question focuses on enabling cross-tenant shared channel collaboration between your organization and microsoft.com. Shared channels in Microsoft Teams allow collaboration with people outside the organization, but require specific configuration at both the organization level and the tenant level. The requirements specify bidirectional collaboration capabilities where your users need to participate in external shared channels and also invite external users to your shared channels.
Correct Option:
Configure Cross-tenant access settings for B2B direct connect
B2B direct connect is the feature that enables shared channel collaboration with other Azure AD organizations. You need to configure both inbound and outbound settings for microsoft.com. For inbound, you need to allow microsoft.com to invite your users to their shared channels. For outbound, you need to allow your users to invite microsoft.com contacts to your shared channels. This configuration is done in Azure AD > External Identities > Cross-tenant access settings.
Incorrect Option:
Configure B2B collaboration settings
B2B collaboration is used for inviting external users as guests to your tenant, which provides them access to teams, channels, and resources. While this does enable external collaboration, it is not the optimal solution for shared channels. B2B direct connect is specifically designed for shared channels with less overhead and better integration. B2B collaboration would require users to be added as guests rather than using the seamless shared channel experience.
Incorrect Option:
Configure organization-wide settings in Microsoft Teams
Organization-wide settings in Teams include external access and guest access configurations. External access (federation) allows users to find, call, and chat with users in other domains but does not provide shared channel collaboration capabilities. This setting controls different collaboration scenarios and would not enable the specific shared channel requirements mentioned in the question.
Incorrect Option:
Configure domain allowlisting for external access
Domain allowlisting for external access controls federation settings, which enable chat and calling with external users. While this might allow some communication with microsoft.com users, it does not enable shared channel functionality. Shared channels require B2B direct connect configuration, not federation settings. This option addresses a different type of external collaboration than what the question requires.
Reference:
Configure cross-tenant access for B2B direct connect - Azure AD
Manage external access in Microsoft Teams
Shared channels in Microsoft Teams
You have a Microsoft 365 tenant that uses Microsoft Skype for Business on-premises. You plan to upgrade to Microsoft Teams in stages based on groups. The features required by each group are shown in the following table.
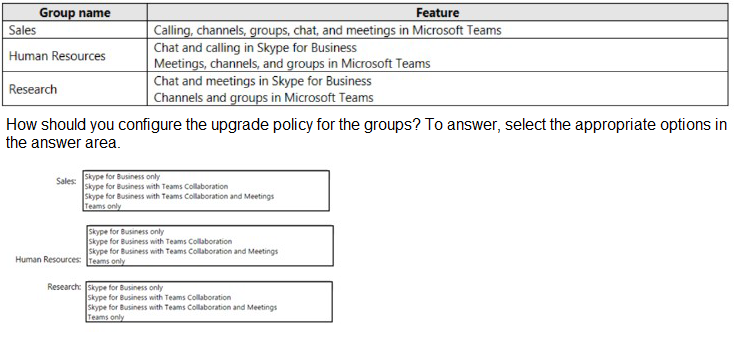
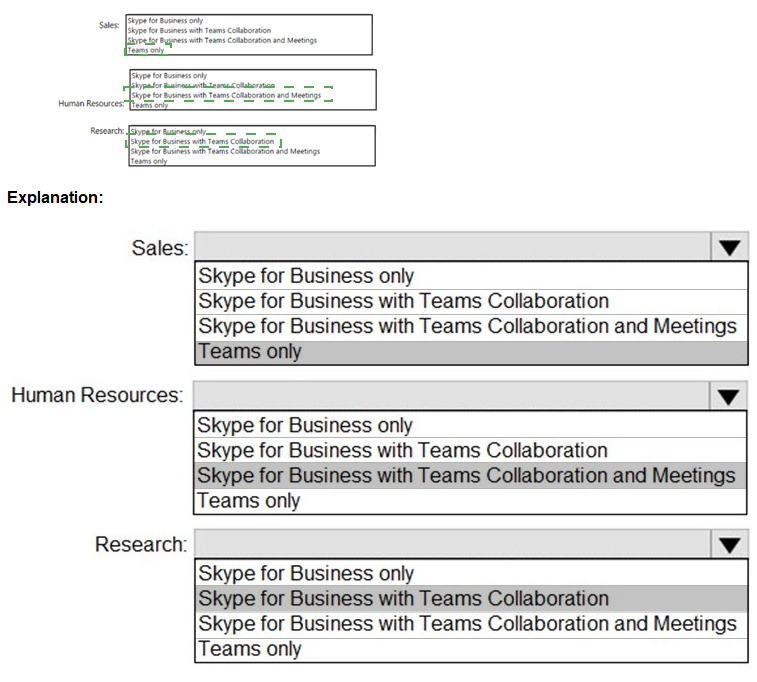
Explanation:
This question addresses configuring upgrade policies during a migration from Skype for Business on-premises to Microsoft Teams. Teams upgrade modes control which client users launch for different workloads. The "Islands" mode (Skype for Business with Teams Collaboration) allows both clients to run simultaneously, while "Teams only" mode forces all functionality into Teams. The selection must be based on which features each group needs from each platform.
Correct Option for Sales:
Teams only
Sales requires calling, channels, groups, chat, and meetings in Microsoft Teams. Since all required features are available in Teams and none are specified for Skype for Business, the appropriate mode is Teams only. This mode provides users with the full Teams experience and ensures all functionality is accessed through the Teams client. Users will not launch Skype for Business as all workloads are handled exclusively in Teams.
Correct Option for Human Resources:
Skype for Business with Teams Collaboration and Meetings
Human Resources requires chat and calling in Skype for Business, but meetings, channels, and groups in Teams. This mixed workload requirement means users need Skype for Business for chat and calling, while Teams handles meetings and collaboration features. This configuration is achieved through the "Skype for Business with Teams Collaboration and Meetings" mode, which routes chat and calling capabilities to Skype for Business while enabling Teams for meetings and collaboration.
Correct Option for Research:
Skype for Business with Teams Collaboration
Research requires chat and meetings in Skype for Business, but channels and groups in Teams. This mode allows both clients to operate side by side, with users able to choose which application to use for each workload. The "Skype for Business with Teams Collaboration" mode (Islands mode) keeps chat and meetings in Skype for Business while enabling Teams for collaboration features like channels and groups.
Incorrect Options:
Skype for Business only would not work for any group because all groups require some Teams functionality. Sales needs all features in Teams, Human Resources needs meetings and collaboration in Teams, and Research needs channels and groups in Teams. This mode would disable Teams entirely and not meet the requirements.
Reference:
Microsoft Teams upgrade modes and coexistence
Choose your upgrade journey from Skype for Business to Microsoft Teams
Migration and interoperability guidance for organizations moving from Skype for Business to Microsoft Teams
Task 6
You need to ensure that only users that are assigned the Global Administrator, User Administrator, or Guest Inviter roles can invite guest users to your company's tenant.
Explanation:
This question addresses controlling guest user invitation permissions in Azure Active Directory. By default, all users and guests can invite guest users to the organization. The requirement is to restrict this capability to only specific administrator roles: Global Administrator, User Administrator, and Guest Inviter. This requires modifying the external collaboration settings in Azure AD to limit who can send invitations.
Correct Option:
Configure Guest invite settings in Azure AD External Identities
The Guest invite settings under External Identities in Azure AD control who can invite guest users. You need to navigate to Azure AD > External Identities > External collaboration settings. Under "Guest invite settings," select "Only users assigned to specific admin roles" and then verify that Global Administrator, User Administrator, and Guest Inviter are the roles with permission. This configuration ensures only these designated roles can invite guest users to the tenant.
Incorrect Option:
Configure Microsoft Teams guest access settings
Teams guest access settings control what guest users can do within Teams, such as calling, meetings, and channel participation. While these settings are important for managing guest experiences, they do not control who can invite guest users to the tenant. Guest invitation permissions are managed at the Azure AD level, not within Teams. Configuring these settings would not meet the requirement to restrict invitation capabilities.
Incorrect Option:
Modify Conditional Access policies
Conditional Access policies control access conditions based on signals like user location, device compliance, or risk level. While these can be applied to guest users, they do not control invitation permissions. Conditional Access is used to enforce access controls after users are in the directory, not to determine who can invite new users. This option would not address the invitation restriction requirement.
Incorrect Option:
Configure user role assignments in Azure AD Roles
While role assignments determine which users hold the Global Administrator, User Administrator, and Guest Inviter roles, this configuration alone does not restrict invitation permissions. Even after assigning these roles correctly, you must still modify the guest invite settings to enforce that only these roles can invite guests. Without changing the external collaboration settings, other users might still retain invitation privileges by default.
Reference:
Configure external collaboration settings in Azure Active Directory
Limit who can invite guests in Azure AD
Manage guest access in Azure Active Directory
Task 11
You need to restrict external Teams communication for both calling and personal chat to only organizational users that use the microsoft.com domain.
Explanation:
This question focuses on controlling external access in Microsoft Teams to limit communication to specific domains. External access (formerly federation) allows users to communicate with users outside the organization. The requirement specifies restricting both calling and personal chat to only users from the microsoft.com domain. This requires configuring domain allowlisting in the external access settings to block all domains except microsoft.com.
Correct Option:
Configure External access settings to allow only specific domains
External access settings in the Teams admin center control communication with users outside the organization. You need to navigate to Teams admin center > Users > External access. Choose "Allow only specific external domains" and add microsoft.com to the allowed domains list. This configuration ensures your users can only communicate via calling and personal chat with users from microsoft.com, blocking all other domains. This meets the requirement precisely.
Incorrect Option:
Configure Guest access settings
Guest access allows external users to be added as guests to your teams and channels, providing access to resources within Teams. This is different from external access which enables calling and personal chat. Guest access would allow microsoft.com users to access team resources but does not specifically control calling and personal chat restrictions. This configuration does not address the requirement for limiting communication channels.
Incorrect Option:
Configure Domain isolation in Azure AD
Domain isolation is typically configured through Conditional Access or B2B policies and controls authentication and access to applications. While this can restrict which domains can access resources, it does not specifically manage Teams calling and personal chat capabilities. External communication restrictions for Teams are managed within Teams admin center, not through Azure AD domain isolation policies.
Incorrect Option:
Configure Information Barriers
Information barriers are policies used to restrict communication between specific groups or users within the same organization, often for compliance reasons. This feature prevents internal users from communicating with each other based on defined segments. Information barriers do not control external communication with other domains and would not address the requirement to restrict communication to only microsoft.com users.
Reference:
Manage external access in Microsoft Teams
Allow or block domains for Teams external access
Configure external chat and collaboration in Microsoft Teams
You have a Microsoft Office 365 subscription named contoso.com. You need to create the Microsoft Teams teams shown in the following table.
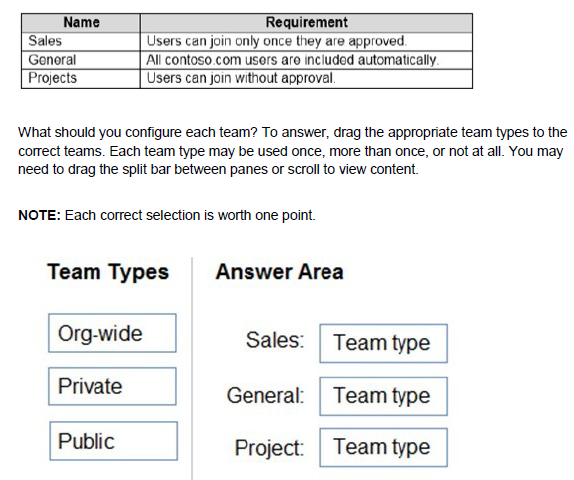
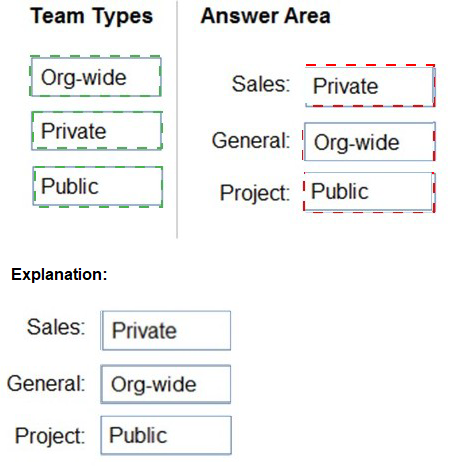
Explanation:
This question focuses on understanding Microsoft Teams team types and their membership behaviors. Teams can be configured as org-wide, private, or public. Org-wide teams automatically include all users in the organization. Public teams allow any user in the organization to join without approval. Private teams require users to be added by owners and require approval for join requests. The requirements for each team dictate which type must be selected.
Correct Option for Sales:
Private
The Sales team requires that users can join only once they are approved. Private teams have controlled membership where users cannot join automatically. When users request to join a private team, the request goes to team owners for approval. This ensures that only approved users gain access to the Sales team, meeting the requirement precisely.
Correct Option for General:
Org-wide
The General team requires that all contoso.com users are included automatically. An org-wide team automatically includes every user in the organization and keeps membership synchronized as users join and leave. This is the only team type that provides automatic inclusion of all users without manual intervention. Org-wide teams are limited to organizations with up to 10,000 users.
Correct Option for Projects:
Public
The Projects team requires that users can join without approval. Public teams allow any user in the organization to discover and join the team directly without needing owner approval. This self-service model enables users to join the Projects team freely whenever they need access to project-related collaboration.
Incorrect Options:
Org-wide would not work for Sales because it would automatically include all users, violating the approval requirement. For Projects, org-wide would include all users unnecessarily rather than allowing optional self-service join. Org-wide is only appropriate for General where automatic inclusion of all users is required.
Private would not work for General or Projects. General requires automatic inclusion of all users, which private teams cannot provide. Projects requires users to join without approval, but private teams require owner approval for all join requests.
Public would not work for Sales because public teams allow anyone to join without approval, violating the approval requirement. Public would also not work for General because it does not automatically include all users; users must proactively join.
Reference:
Create an org-wide team in Microsoft Teams
Manage public and private teams in Microsoft Teams
Team types and membership in Microsoft Teams
Task 6
You need to configure a virtual receptionist for your company's main office located at 1 Microsoft Way, Redmond. The solution must meet the following requirements:
•Callers must press 1 for the company directory to lookup by name.
•Callers must press 0 to hear the company address.
•Callers must be offered the same menu at all times.
Explanation:
This question focuses on configuring Auto Attendants in Microsoft Teams Phone System. Auto Attendants provide menu options for callers to navigate and reach appropriate departments or information. The requirements specify specific key presses for company directory access and company address information, with a consistent menu experience. This requires creating an Auto Attendant with dial scope options and custom menu prompts.
Correct Option:
Create an Auto Attendant with dial scope options configured
An Auto Attendant in Teams Phone System allows you to configure menu options that callers hear when they connect. You need to create an Auto Attendant with a menu prompt that instructs callers to press 1 for the company directory and press 0 to hear the company address. For option 1, configure a dial scope that points to the company directory for name lookup. For option 0, configure an announcement that plays the company address. Set the menu to be available 24/7 to ensure callers always receive the same menu options.
Incorrect Option:
Create a Call Queue
Call Queues are designed to manage incoming calls with features like greeting messages, music on hold, and call distribution to agents. While useful for departments like sales or support, Call Queues do not provide menu-driven navigation or directory lookup capabilities. They handle calls that are already directed to a specific department rather than providing an initial receptionist experience. This would not meet the requirements for directory lookup or company address playback.
Incorrect Option:
Configure a Resource Account with a Calling License
Resource accounts are required for Auto Attendants and Call Queues to have phone numbers assigned, but they are not the solution itself. A resource account must be created and licensed before an Auto Attendant can function, but configuring only a resource account without creating the actual Auto Attendant would not provide any menu options or functionality for callers. This is a prerequisite, not the complete solution.
Incorrect Option:
Configure an Operator Connect number
Operator Connect is a method for obtaining phone numbers from a telecommunications provider. While you need a phone number for your Auto Attendant, simply configuring an Operator Connect number does not create the menu system or directory capabilities. The number must be assigned to a properly configured Auto Attendant to meet the requirements. This option addresses only the connectivity aspect, not the functionality needed.
Reference:
Set up an Auto Attendant for Microsoft Teams
Manage Auto Attendant menus and dial scope
Resource accounts for Auto Attendants and Call Queues
Your company uses Teams. You plan to assign an enhanced encryption policy to enable end-to-end encryption for Teams calls. Which features support end-to-end encryption for one-to-one Teams calls?
A. audio only
B. video only
C. chat only
D. audio and video only
E. audio, video, and chat
Explanation:
This question tests knowledge of end-to-end encryption capabilities in Microsoft Teams calls. End-to-end encryption ensures that communication is encrypted from sender to receiver without intermediate decryption. Microsoft Teams supports end-to-end encryption for one-to-one calls, but it is important to understand which specific features within those calls are actually encrypted end-to-end versus those that use other encryption methods.
Correct Option:
E. audio, video, and chat
Microsoft Teams supports end-to-end encryption for one-to-one calls that includes audio, video, and screen sharing. The chat component during an active call is also covered by end-to-end encryption when the call is encrypted. This comprehensive protection ensures that all real-time communication modalities within the call session remain private between the participants. Users must enable this feature through enhanced encryption policies, and both parties must be using compatible Teams clients for end-to-end encryption to function properly.
Incorrect Option:
A. audio only
This option is incorrect because end-to-end encryption in Teams calls is not limited to only audio. While audio is certainly protected, Microsoft implements end-to-end encryption to cover multiple modalities within the call. Restricting to only audio would leave video and screen sharing unprotected, which does not align with the comprehensive security approach Microsoft has implemented for encrypted calls.
Incorrect Option:
B. video only
This option is incorrect as end-to-end encryption in Teams calls is not restricted to video content only. Video is one component that receives protection, but audio and screen sharing are equally important to encrypt. Microsoft's implementation covers all real-time media streams within the call to ensure complete conversation privacy.
Incorrect Option:
C. chat only
This option is incorrect because chat messages sent during an end-to-end encrypted call are protected, but the encryption extends far beyond just chat. The primary purpose of end-to-end encryption for calls is to protect the media streams (audio and video). Chat alone would not address the need for private voice and video communication.
Incorrect Option:
D. audio and video only
This option is partially correct but incomplete. While audio and video are indeed protected by end-to-end encryption, this option omits screen sharing and in-call chat. Microsoft's end-to-end encryption for one-to-one calls covers all these modalities to provide complete protection for the call session. Excluding screen sharing and chat leaves potential vulnerabilities in the communication.
Reference:
Use end-to-end encryption for one-to-one Microsoft Teams calls
Manage encryption for Teams
Enhanced encryption policies in Microsoft Teams
You have a Microsoft 365 subscription that uses Teams.
You need to create a custom policy named Policy1 that will disable the ability to send
feedback and suggestions about Teams to Microsoft.
How should you complete the PowerShell command? To answer, select the appropriate
options in the answer area.
NOTE: Each correct selection is worth one point.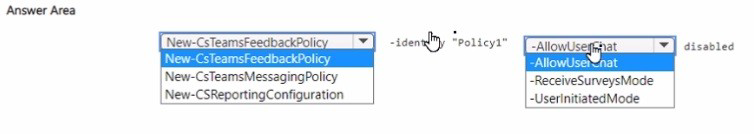
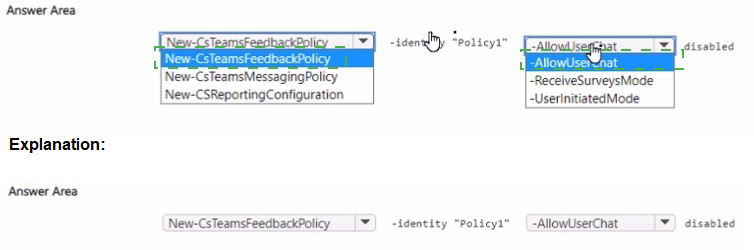
Explanation:
This question tests knowledge of PowerShell commands for managing Teams feedback policies. The New-CsTeamsFeedbackPolicy cmdlet is used to create custom feedback policies that control whether users can send feedback, suggestions, and survey responses to Microsoft. The parameters must be set correctly to disable all feedback capabilities as required.
Correct Option for Identity:
-Identity "Policy1"
The Identity parameter specifies the name of the new feedback policy being created. In this case, the policy must be named "Policy1" as stated in the requirement. This parameter is mandatory when creating a new policy and defines how the policy will be referenced when assigning it to users.
Correct Option for UserInitiatedMode:
-UserInitiatedMode disabled
The UserInitiatedMode parameter controls whether users can voluntarily submit feedback and suggestions to Microsoft. Setting this to "disabled" ensures users cannot initiate feedback submissions through the Teams client. This is a key requirement for preventing users from sending suggestions and feedback about Teams.
Correct Option for ReceiveSurveysMode:
-ReceiveSurveysMode disabled
The ReceiveSurveysMode parameter controls whether users receive survey invitations from Microsoft about their Teams experience. Setting this to "disabled" ensures users will not receive any survey requests. This complements the UserInitiatedMode setting to completely eliminate all feedback channels.
Incorrect Options:
-AllowUserThat This is not a valid parameter for the New-CsTeamsFeedbackPolicy cmdlet.
The correct parameters for controlling feedback capabilities are UserInitiatedMode and ReceiveSurveysMode. This option appears to be a distractor in the answer area.
AllowUser that disabled This is not a valid parameter syntax.
The cmdlet uses specific parameter names like UserInitiatedMode and ReceiveSurveysMode with values like "enabled" or "disabled". This option does not represent a valid PowerShell parameter.
Reference:
New-CsTeamsFeedbackPolicy PowerShell cmdlet
Manage feedback policies in Microsoft Teams
Set up Teams feedback policies for your organization
Task 1
Your company is opening a branch office in Miami. The office uses a network range of 10.10.10.0/24.
You need to restrict Teams bandwidth to 1.000 Kpbs for all the users working at the Miami office. The solution must NOT affect other offices.
Explanation:
This question addresses bandwidth management in Microsoft Teams to control network usage for specific locations. Teams requires sufficient bandwidth for optimal performance, and organizations may need to restrict bandwidth in certain offices to prevent network congestion. The requirement specifies limiting bandwidth to 1000 Kbps (1 Mbps) for all users in the Miami office with the 10.10.10.0/24 network range, without affecting other locations.
Correct Option:
Create and configure a network topology with a network site and assign a bandwidth policy
To restrict Teams bandwidth for specific locations, you need to configure a network topology in the Teams admin center. First, define network sites including the Miami office with its IP subnet 10.10.10.0/24. Then create a bandwidth policy that limits media traffic to 1000 Kbps and assign it to the Miami site. The network roaming policy ensures users connecting from this subnet are automatically identified as being in the Miami site and have the bandwidth restrictions applied without affecting users in other locations.
Incorrect Option:
Configure a Teams meeting policy with bandwidth limitations
Meeting policies control features available in meetings but do not provide granular bandwidth control based on network location. While meeting policies can limit video resolution or disable certain features, they apply to users regardless of where they are connecting from. This would not meet the requirement of restricting only Miami office users while leaving others unaffected, and would not achieve the specific bandwidth limit of 1000 Kbps.
Incorrect Option:
Configure a Teams calling policy
Calling policies control calling features and voicemail settings but do not manage network bandwidth consumption. These policies determine what calling capabilities users have, such as call forwarding or delegation, not how much network bandwidth their media traffic consumes. This option cannot enforce the 1000 Kbps bandwidth restriction required.
Incorrect Option:
Create a Conditional Access policy to restrict media traffic
Conditional Access policies control access to applications based on conditions like location, device compliance, or risk. They are used for security and access control, not for managing network bandwidth or media traffic limitations. Conditional Access cannot enforce bandwidth caps or prioritize network traffic for Teams media.
Reference:
Configure network topology for media traffic in Microsoft Teams
Manage bandwidth policies in Microsoft Teams
Plan for network bandwidth requirements for Microsoft Teams
| Page 1 out of 34 Pages |
Managing Microsoft Teams Practice Exam Questions
These MS-700 practice questions with explanations help candidates learn how to manage and configure Microsoft Teams effectively. The questions focus on governance, security, collaboration settings, and Teams lifecycle management. Each explanation provides clear reasoning behind the correct answer, helping learners understand both technical and administrative concepts. This approach supports deeper learning and real-world application. By practicing regularly, candidates can improve their understanding of Teams management, strengthen their skills, and gain confidence for the certification exam.MS-700 - Managing Microsoft Teams Official Exam Blueprint and Weight:
1. Plan and Configure a Microsoft Teams Environment
Official Exam Weight: 25-30%
Subtopics: Plan Microsoft Teams architecture, manage Microsoft 365 tenant settings for Teams, configure Teams settings and policies, manage Teams licenses and subscriptions, configure network requirements for Teams, implement governance and lifecycle management, manage Teams templates, configure organization-wide settings, plan Teams deployment and adoption strategies, manage Teams clients and updates, configure guest and external access settings, implement compliance and security requirements.
2. Manage Chat Teams Channels and Apps
Official Exam Weight: 20-25%
Subtopics: Create and manage teams and channels, configure channel types including standard private and shared channels, manage team membership and ownership, configure chat settings and messaging policies, manage Teams applications and app permissions, configure app setup policies, deploy and manage custom apps, manage tags and mentions, configure file collaboration and SharePoint integration, monitor team usage and activity, troubleshoot collaboration and communication issues.
3. Manage Meetings Webinars and Town Halls
Official Exam Weight: 15-20%
Subtopics: Configure meeting policies and settings, manage meeting templates, configure audio conferencing and dial-in options, manage webinars and registration settings, configure town halls and large events, manage meeting recordings and transcripts, configure meeting security and compliance settings, manage meeting room devices and resources, troubleshoot meeting quality and connectivity issues, monitor meeting analytics and reports.
4. Manage Calling and Phone Systems
Official Exam Weight: 15-20%
Subtopics: Configure Microsoft Teams Phone, manage phone numbers and calling plans, configure Direct Routing and Operator Connect, manage auto attendants and call queues, configure emergency calling policies, manage voice routing policies, configure voicemail and call settings, manage common area phones and devices, troubleshoot calling and telephony issues, monitor call quality and performance metrics, manage PSTN connectivity solutions.
5. Monitor Secure and Troubleshoot Microsoft Teams
Official Exam Weight: 20-25%
Subtopics: Monitor Teams service health and usage reports, manage Teams administration and analytics, configure Microsoft Purview compliance features, implement retention and data loss prevention (DLP) policies, manage information barriers and eDiscovery, configure security and conditional access policies, manage Microsoft Defender for Office 365 integration, troubleshoot Teams client and service issues, monitor network performance and call quality, manage audit logs and compliance reporting, implement best practices for Teams operations and governance.
| Domain | Title | Exam Weight |
|---|---|---|
| 1 | Plan and Configure a Microsoft Teams Environment | 25-30% |
| 2 | Manage Chat Teams Channels and Apps | 20-25% |
| 3 | Manage Meetings Webinars and Town Halls | 15-20% |
| 4 | Manage Calling and Phone Systems | 15-20% |
| 5 | Monitor Secure and Troubleshoot Microsoft Teams | 20-25% |
Trusted by Our Customers
Teams administration has become critical for modern collaboration. The MS-700 exam covers governance, security, and meeting policies. MSmcqs.com provided practice test that mirrored the real exam scenarios perfectly. I felt completely prepared and passed on my first attempt. Highly recommended!
Patricia Morgan, Teams Administrator | New York, NY