Free Microsoft SC-401 Practice Test Questions MCQs
Stop wondering if you're ready. Our Microsoft SC-401 practice test is designed to identify your exact knowledge gaps. Validate your skills with Administering Information Security in Microsoft 365 questions that mirror the real exam's format and difficulty. Build a personalized study plan based on your free SC-401 exam questions mcqs performance, focusing your effort where it matters most.
Targeted practice like this helps candidates feel significantly more prepared for Administering Information Security in Microsoft 365 exam day.
21210+ already prepared
Updated On : 7-Apr-2026121 Questions
Administering Information Security in Microsoft 365
4.9/5.0
Topic 2: Mix Questions
| Page 1 out of 13 Pages |
Administering Information Security in Microsoft 365 Practice Exam Questions
These SC-401 practice questions with explanations help candidates learn how to manage information security in Microsoft environments. Topics include data protection, compliance, identity management, and threat prevention. Each question includes a detailed explanation that helps learners understand security concepts and policies. This approach supports deeper learning and real-world application. By practicing consistently, candidates can strengthen their understanding of information security and confidently prepare for the certification exam.Winning Strategy for SC-401: Information Security in Microsoft 365
The SC-401 is not about isolated tools; its about administering the integrated Microsoft 365 Defender ecosystem. Your strategy must center on configuring, monitoring, and responding across the Microsoft 365 security suite.
Phase 1: Master the Three Pillars of the Exam
Your study must balance these interconnected areas:
1. Defender Suite Administration (60% Focus)
Microsoft Defender XDR: This is the central nervous system. You must know how to navigate incidents, manage actions, and use the advanced hunting query language (KQL) inside the unified portal.
Component Defenders: Deep-dive into configuring and managing:
Defender for Office 365: Anti-phishing policies, Safe Attachments, Safe Links.
Defender for Endpoint: Security baselines, device onboarding, threat & vulnerability management.
Defender for Identity: Configuring sensors, monitoring identity-based alerts.
2. Data Governance & Compliance (25% Focus)
Purview Insider Risk Management: Understand policy triggers, indicators, and case management. This is a heavily tested, scenario-driven topic.
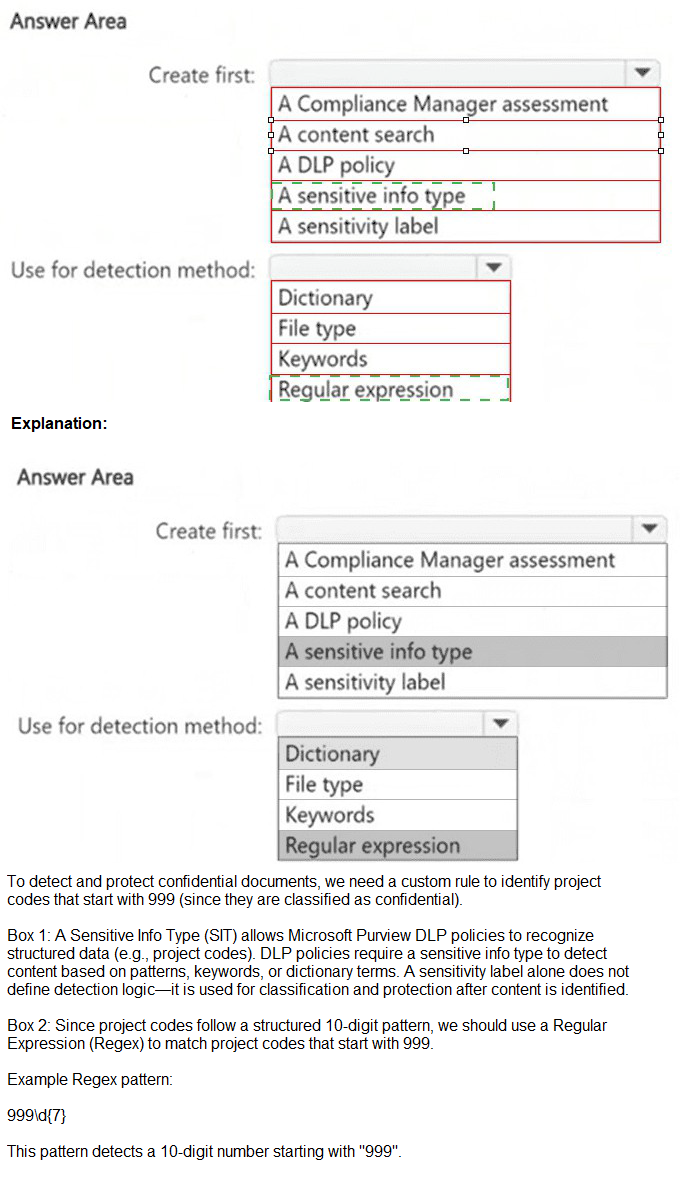
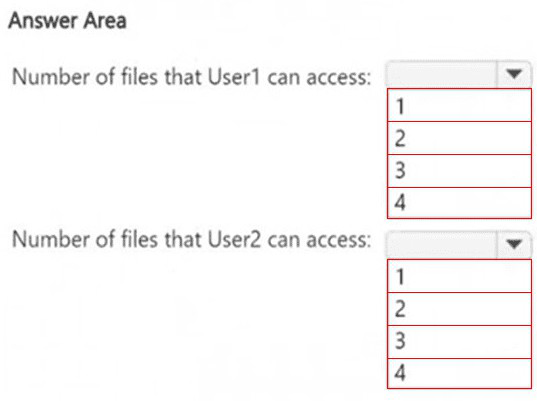
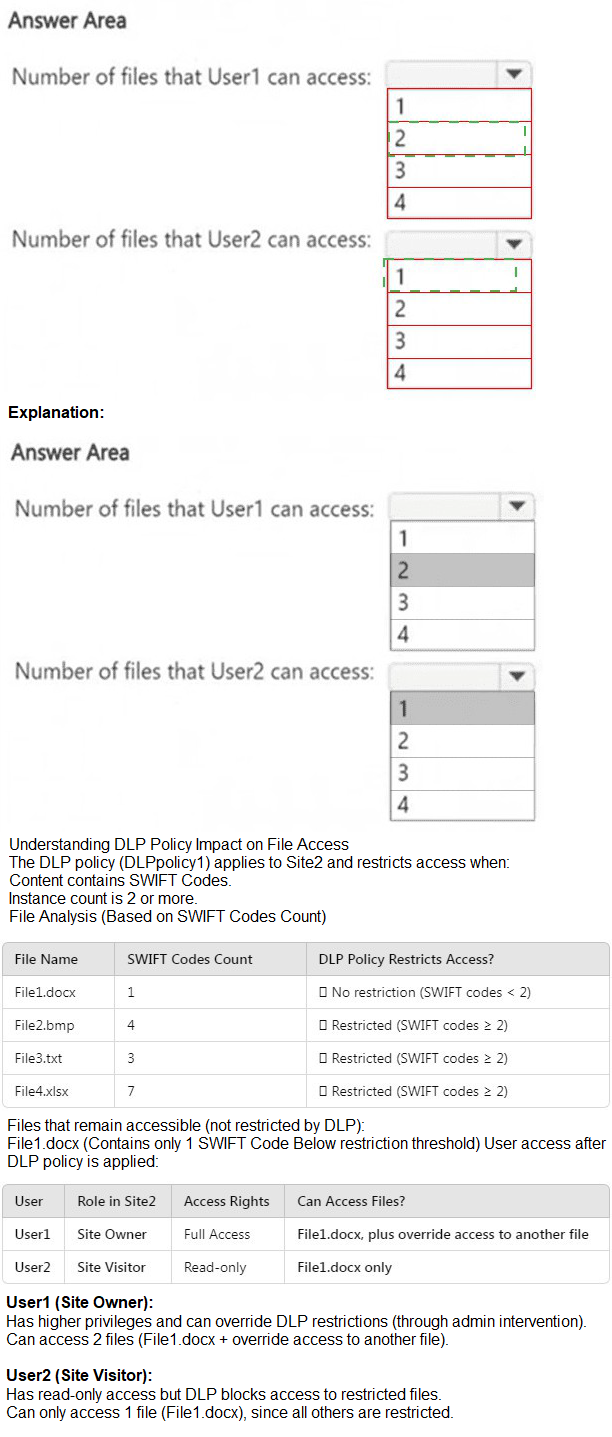
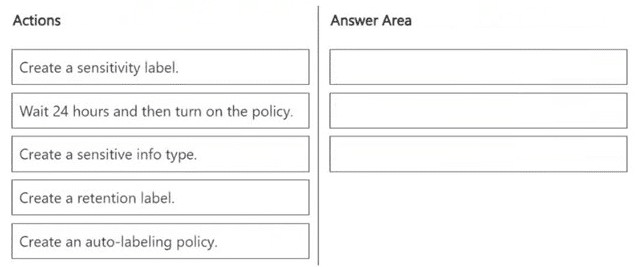
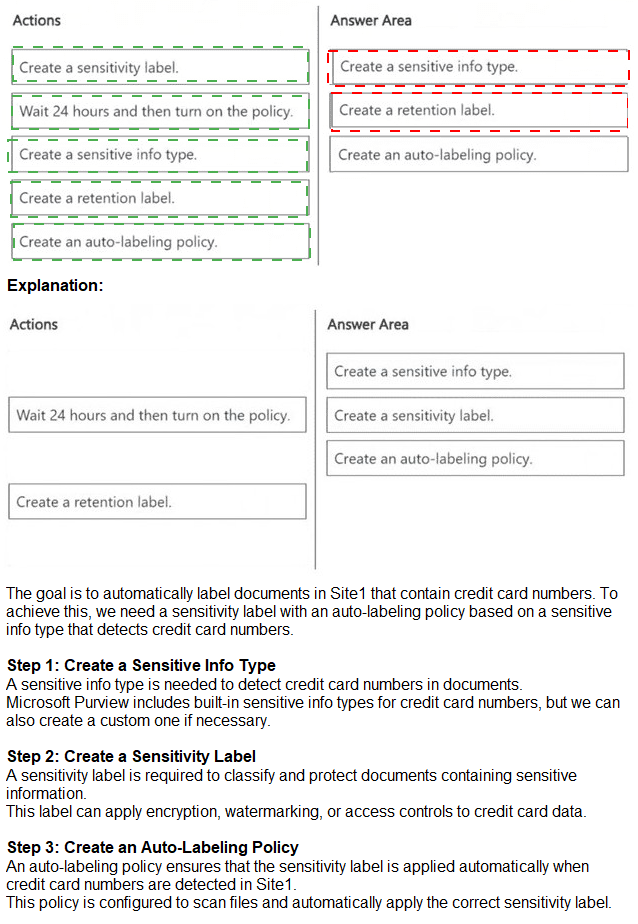
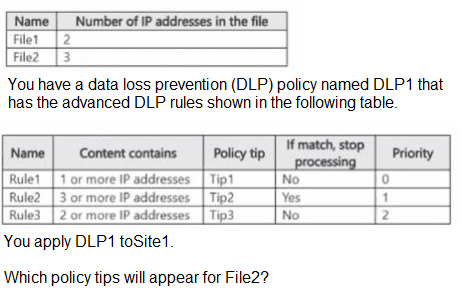
Data Loss Prevention (DLP): Know how to create, test, and tune DLP policies for Exchange Online, SharePoint, Teams, and Endpoint.
3. Identity & Access Security (15% Focus)
Entra ID Security: Focus on Conditional Access for Zero Trust, identity protection policies, and privileged access management.
Phase 2: The Execution Blueprint (4-6 Weeks)
Week 1-2: Foundation Through Labs
Do not start with theory. Immediately access a Microsoft 365 developer tenant (free for 90 days, renewable).
Go to the Microsoft 365 Defender portal and click every tab. Create a simple DLP policy. Trigger a test alert. Learn by breaking things in a safe environment. Complete the official Microsoft Learn SC-401 modules alongside your exploration.
Week 3-4: Integration & Scenarios
This is the critical phase. Study how the tools connect.
How does a Defender for Identity alert feed into a Defender XDR incident?
How does a DLP policy trigger an Insider Risk Management case?
Use platforms like MSmcqs.com for targeted scenario SC-401 practice questions. Their questions force you to apply knowledge to realistic administrative decisions—exactly what the exam tests. Analyze every wrong answer to identify conceptual gaps.
Week 5: KQL Mastery & Policy Deep Dive
You must be comfortable writing basic KQL queries for advanced hunting. Practice daily in the Defender portal hunting lab. Focus on where, summarize, join, and project operators.
Revisit complex policy creation (Anti-phishing, Insider Risk) until you can list the configuration steps from memory.
Week 6: Final Review & Exam Simulation
Take full-length, timed Administering Information Security in Microsoft 365 practice exams to build stamina.
Review only your weak areas using the official skills outline as a final checklist.
Winning Mantra: "Configure, Correlate, Contain." You are being tested on your ability to configure the security stack, correlate signals across it, and contain threats using the tools you administer. Prioritize hands-on practice in the Defender portals above all else.
Results That Speak for Themselves
Information protection and compliance topics were easier to master with MSmcqs SC-401 practice test for Microsoft Certified: Information Security Administrator Associate. The realistic questions improved exam readiness significantly.
William Scott | Canada