Topic 2: Mix Questions
You have a Microsoft 365 E5 subscription.
Users access their mailbox by using the following apps.
• Outlook for Microsoft 365
• Outlook on the web
• Outlook Mobile fiOS. Android)
You create a data loss prevention (DLP) policy named DLP1 that has the following settings:
• Location; Exchange email
• Status: On
• User notifications: On
• Notify users with a policy tip: Enabled
Which apps display a policy tip when content is matched by using DIP1 ?
A. Outlook for Microsoft 365 only
B. Outlook on the web only
C. Outlook for Microsoft 365 and Outlook on the web only
D. Outlook for Microsoft 365 and Outlook Mobile (iOS. Android) only
E. Outlook for Microsoft 365. Outlook on the web, and Outlook Mobile (iOS. Android)
Explanation:
This question tests your knowledge of DLP policy tip support across different Outlook clients. Exchange Online DLP policies can display policy tips to users when they compose or send sensitive content. However, not all Outlook clients support inline policy tip notifications.
Correct Option:
C. Outlook for Microsoft 365 and Outlook on the web only
Outlook for Microsoft 365 (desktop client) and Outlook on the web (OWA) fully support DLP policy tips. These clients display real-time notifications when users compose emails that match DLP conditions, allowing them to override or fix the issue before sending.
Incorrect Option:
D. Outlook Mobile (iOS, Android) only –
Outlook Mobile does not display DLP policy tips during email composition.
A, B, E –
Incomplete or incorrect combinations. Outlook Mobile does not support policy tips, so E is incorrect. A and B omit one of the two clients that do support them.
Reference:
Microsoft Learn: “Data loss prevention policy tips reference” – Supported clients: Outlook desktop, Outlook on the web; Not supported: Outlook for iOS/Android, Exchange ActiveSync clients.
Microsoft Documentation: “DLP policy tips in Outlook” – Policy tips appear in Outlook 2013 and later and OWA; mobile apps do not support this feature.
You are planning a data loss prevention (DLP) solution that will apply to Windows Client computers.
You need to ensure that when users attempt to copy a file that contains sensitive
information to a USB storage device, the following requirements are met:
If the users are members of a group named Group1, the users must be allowed to copy
the file, and an event must be recorded in the audit log.
All other users must be blocked from copying the file.
What should you create?
A. one DLP policy that contains one DLP rule
B. one DLP policy that contains two DLP rules
C. two DLP policies that each contains one DLP rule
Explanation:
This question tests your knowledge of DLP rule structure for endpoint scenarios. You need separate logic for Group1 (audit only) versus all other users (block). Since both conditions apply to the same location (USB copy) and same content (sensitive files), one DLP policy containing two rules is the correct approach.
Correct Option:
B. one DLP policy that contains two DLP rules
One rule is configured for Group1 with the action set to Audit only and the condition scoped to Group1. The second rule is configured for All users except Group1 with the action set to Block. Both rules reside in the same DLP policy targeting USB removable media.
Incorrect Option:
A. one DLP policy that contains one DLP rule –
A single rule cannot apply both Allow (audit) to Group1 and Block to others.
C. two DLP policies that each contains one DLP rule –
This would work technically but is unnecessary and less efficient. Overlapping policies can cause confusion and priority conflicts. Microsoft recommends grouping related rules into one policy.
Reference:
Microsoft Learn: “Data loss prevention policy reference” – Multiple rules in one policy can target different conditions and actions.
Microsoft Documentation: “Using conditions in DLP policies” – Use exceptions or user groups to create granular control within one policy.
You have a Microsoft 365 E5 subscription. You need to create a sensitivity label named Label1. The solution must ensure that users can use Microsoft 365 Copilot to summarize files that have Label1 applied. Which permission should you select for Label1?
A. Export content(EXPORT)
B. Copy and extract content(EXTRACT)
C. Edit content(DOCEDIT)
D. View rights(VIEW)
Explanation:
This question tests your understanding of how Microsoft 365 Copilot interacts with encrypted sensitivity labels. For Copilot to read and summarize content protected by a sensitivity label, the label’s encryption permissions must grant the Copy and extract content usage right. This right is required for Copilot to access and process the file’s content.
Correct Option:
B. Copy and extract content (EXTRACT)
Microsoft 365 Copilot requires the EXTRACT usage right to read and summarize protected content. Without this permission, Copilot cannot access the file’s content and will return an empty or access-denied response.
Incorrect Option:
A. Export content (EXPORT) –
Allows saving in unencrypted format, but does not grant Copilot access for summarization.
C. Edit content (DOCEDIT) –
Allows modifying content, but Copilot needs read/extract rights, not edit.
D. View rights (VIEW) –
Allows opening and reading, but Copilot requires the EXTRACT right specifically to process content for summarization.
Reference:
Microsoft Learn: “Sensitivity labels and Microsoft 365 Copilot” – Copilot requires the EXTRACT usage right to summarize encrypted content.
Microsoft Documentation: “Usage rights for sensitivity labels” – EXTRACT right is necessary for AI/ML processing of protected content.
Note: This question is part of a series of questions that present the same scenario. Each
question in the series contains a unique solution that might meet the stated goals. Some
question sets might have more than one correct solution, while others might not have a
correct solution.
After you answer a question in this section, you will NOT be able to return to it. As a result,
these questions will not appear in the review screen.
You recently discovered that the developers at your company emailed Azure Storage
Account keys in plain text to third parties.
You need to ensure that when Azure Storage Account keys are emailed, the emails are
encrypted.
Solution: You configure a mail flow rule that matches a sensitive info type.
Does this meet the goal?
A. Yes
B. No
Explanation:
This question tests your knowledge of how to enforce encryption on emails containing sensitive information. While a mail flow rule can detect sensitive info types and apply encryption, the specific requirement is to encrypt emails containing Azure Storage Account keys. Azure Storage Account keys are not a built-in sensitive info type in Microsoft Purview.
Correct Option:
B. No
The solution fails because Azure Storage Account keys are not included in the default sensitive information types. Without a custom sensitive info type or a pattern match (e.g., keyword + regex) defined for Azure storage account keys, the mail flow rule will not detect the content and therefore will not apply encryption.
Incorrect Option:
A. Yes –
This is incorrect because the built-in sensitive info types do not include Azure Storage Account keys. The rule would not trigger unless you first create a custom sensitive info type or use a different detection method.
Reference:
Microsoft Learn: “Sensitive information types in Microsoft Purview” – Azure Storage account keys are not included in default SITs.
Microsoft Documentation: “Define mail flow rules to encrypt email messages” – Rule requires a condition; sensitive info type condition requires a defined SIT.
Note: This question is part of a series of questions that present the same scenario. Each
question in the series contains a unique solution that might meet the stated goals. Some
question sets might have more than one correct solution, while others might not have a
correct solution.
After you answer a question in this section, you will NOT be able to return to it. As a result,
these questions will not appear in the review screen.
You have a Microsoft 365 subscription.
You have a user named User1. Several users have full access to the mailbox of User1.
Some email messages sent to User1 appear to have been read and deleted before the
user viewed them.
When you search the audit log in the Microsoft Purview portal to identify who signed in to the mailbox of User1, the results are blank.
You need to ensure that you can view future sign-ins to the mailbox of User1.
Solution: You run the Set-AdminAuditLogConfig -AdminAuditLogEnabled $true -
AdminAuditLogCmdlets *Mailbox* command.
Does that meet the goal?
A. Yes
B. No
Explanation:
This question tests your knowledge of mailbox audit logging versus administrator audit logging in Exchange Online. The requirement is to view future mailbox sign-ins (user access to User1’s mailbox). The cmdlet shown configures admin audit logging, which tracks administrator actions, not mailbox access by delegated users.
Correct Option:
B. No
The solution uses the wrong audit log. AdminAuditLogConfig tracks Exchange Online administrator cmdlet executions, not mailbox sign-in events. To log mailbox access by delegated users, you must enable mailbox audit logging for User1’s mailbox using Set-Mailbox -AuditEnabled $true and configure the specific logon types to audit.
Incorrect Option:
A. Yes –
This is incorrect because admin audit logs do not capture delegated mailbox sign-in events. Even with the Mailbox cmdlet filter, this only logs administrative cmdlet usage, not user sign-ins.
Reference:
Microsoft Learn: “Manage mailbox auditing in Exchange Online” – Mailbox audit logging must be explicitly enabled; it logs delegate access, admin access, and owner access.
Microsoft Documentation: “Set-AdminAuditLogConfig” – This cmdlet configures administrator audit logging, not mailbox auditing.
HOTSPOT
You have a Microsoft 365 E5 subscription that uses Microsoft Purview and just-in-time (JIT)
protection. The subscription contains the users shown in the following table.
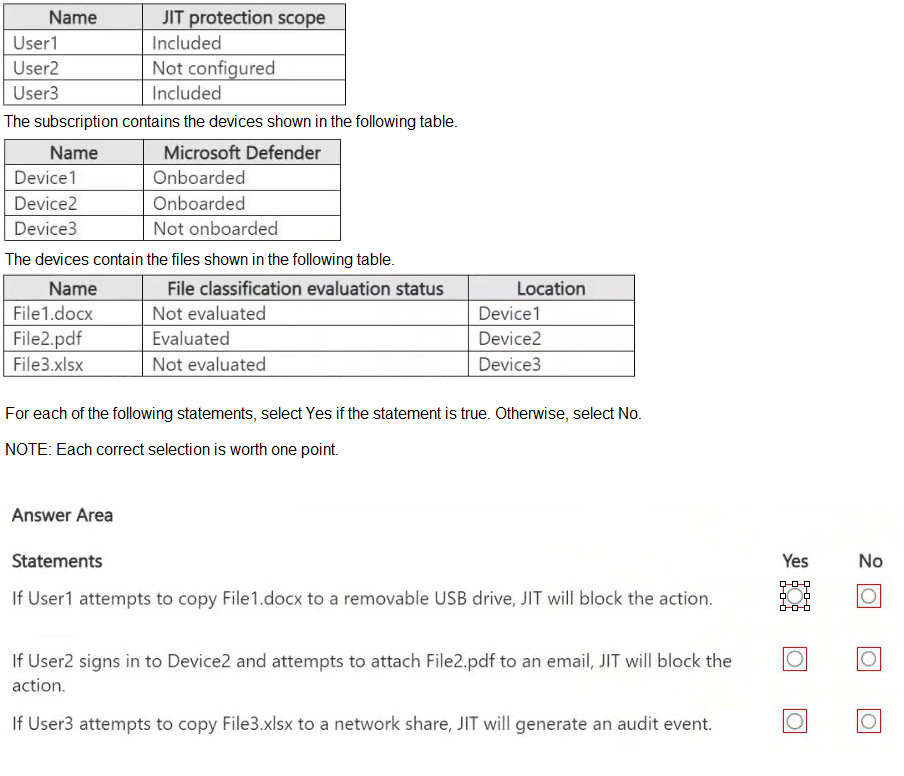
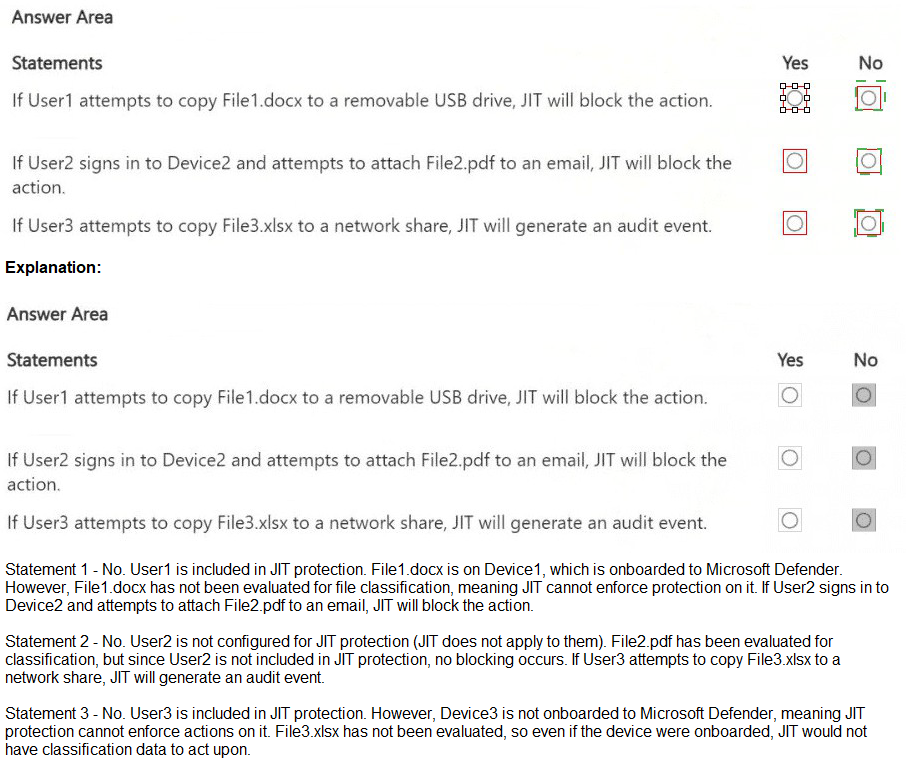
Explanation:
This question tests your knowledge of Just-In-Time (JIT) protection in Microsoft Purview. JIT applies DLP restrictions to users scoped into the policy when they attempt risky actions. JIT requires: user scoped as “Included,” device onboarded to Defender, and file evaluated by the JIT policy. If any of these are missing, JIT does not enforce.
Correct Option:
Statement 1: No
User1 is included in JIT scope, Device1 is onboarded, but File1.docx is Not evaluated. JIT protection applies only to files that have been classified/evaluated. A file with “Not evaluated” status will not trigger JIT policy actions. Therefore, JIT will not block the action.
Statement 2: No
User2 is “Not configured” for JIT scope. Even though Device2 is onboarded and File2.pdf is Evaluated, JIT only applies to users explicitly included in the policy scope. User2 is not scoped, so no JIT enforcement occurs.
Statement 3: No
User3 is included in JIT scope, but Device3 is Not onboarded to Microsoft Defender. JIT protection requires devices to be onboarded to Microsoft Defender for Endpoint. Without onboarding, JIT cannot enforce policies or generate audit events.
Incorrect Option:
None — all statements are false based on JIT prerequisites.
Reference:
Microsoft Learn: “Just-in-time protection for data loss prevention” – JIT requires user in scope, device onboarded, and file evaluated.
Microsoft Documentation: “Get started with JIT protection” – Only evaluated files trigger JIT; devices must be onboarded to Defender.
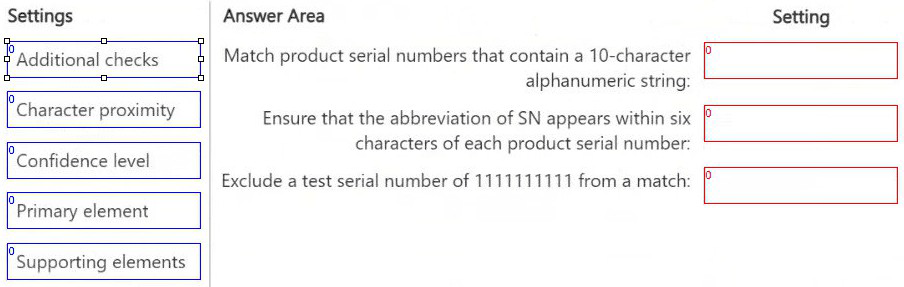
DRAG DROP
You have a Microsoft 365 E5 subscription that has data loss prevention (DLP)
implemented.
You need to create a custom sensitive info type. The solution must meet the following
requirements:
Match product serial numbers that contain a 10-character alphanumeric string.
Ensure that the abbreviation of SN appears within six characters of each product serial
number.
Exclude a test serial number of 1111111111 from a match.
Which pattern settings should you configure for each requirement? To answer, drag the
appropriate settings to the correct requirements. Each setting may be used once, more
than once, or not at all. You may need to drag the split bar between panes or scroll to view
content.
NOTE: Each correct selection is worth one point.
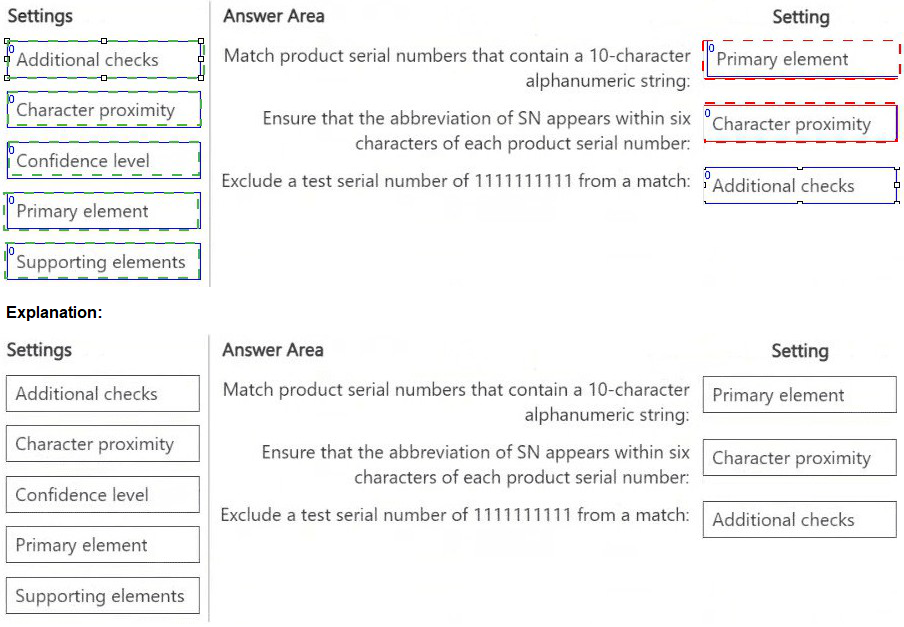
Explanation:
This question tests your knowledge of configuring custom sensitive information type (SIT) patterns in Microsoft Purview. Each requirement corresponds to a specific pattern setting: the element that defines the pattern, the proximity requirement, and the exclusion condition.
Correct Order:
Match product serial numbers that contain a 10-character alphanumeric string:
Primary element
The primary element defines the regular expression (regex) that identifies the sensitive information—in this case, a 10-character alphanumeric string pattern. This is the core detection component of the custom SIT.
Ensure that the abbreviation of SN appears within six characters of each product serial number:
Character proximity
Character proximity sets the maximum distance (in characters) between the primary element (serial number) and the supporting element or keyword (e.g., “SN”). Here, six characters is the proximity value.
Exclude a test serial number of 1111111111 from a match:
Additional checks
Additional checks allow you to define exclusions, such as specific patterns or values to ignore. You can configure a “match not to include” condition to exclude 1111111111 from triggering the SIT.
Incorrect Option:
Supporting elements –
These are used to define keywords or secondary patterns that increase confidence, not to set proximity distance.
Confidence level –
This sets the numeric confidence score (e.g., 75, 85) but does not define pattern matching, proximity, or exclusions.
Reference:
Microsoft Learn: “Create a custom sensitive information type in the Microsoft Purview compliance portal” – Use primary element, character proximity, and additional checks (exclusions).
Microsoft Documentation: “Sensitive information type pattern settings” – Proximity is set via Character proximity; exclusions via Additional checks.
You receive an email that contains a list of words that will be used for a sensitive information type. You need to create a file that can be used as the source of a keyword dictionary. In which format should you save the list?
A. an XLSX file that contains one word in each cell of the first row
B. an XML file that contains a keyword tag for each word
C. an ACCDB database file that contains a table named Dictionary
D. a text file that has one word on each line
Explanation:
This question tests your knowledge of the required file format for importing a keyword dictionary in Microsoft Purview. When creating a custom sensitive information type that uses a keyword dictionary as evidence, the source file must be a simple text file with one word per line.
Correct Option:
D. a text file that has one word on each line
Microsoft Purview requires keyword dictionary source files to be in plain text (.txt) format with each term on a separate line. This file is uploaded during the dictionary creation process in the compliance portal or via PowerShell.
Incorrect Option:
A. an XLSX file that contains one word in each cell of the first row – Not supported for keyword dictionary import.
B. an XML file that contains a keyword tag for each word – Not a valid source format for dictionary creation.
C. an ACCDB database file that contains a table named Dictionary – Microsoft Access database files are not supported for keyword dictionary upload.
Reference:
Microsoft Learn: “Create a keyword dictionary” – Requires a text file (.txt) with one entry per line.
Microsoft Documentation: “Import a keyword dictionary” – Supported formats: .txt; maximum 1 MB file size.
You have the files shown in the following table.
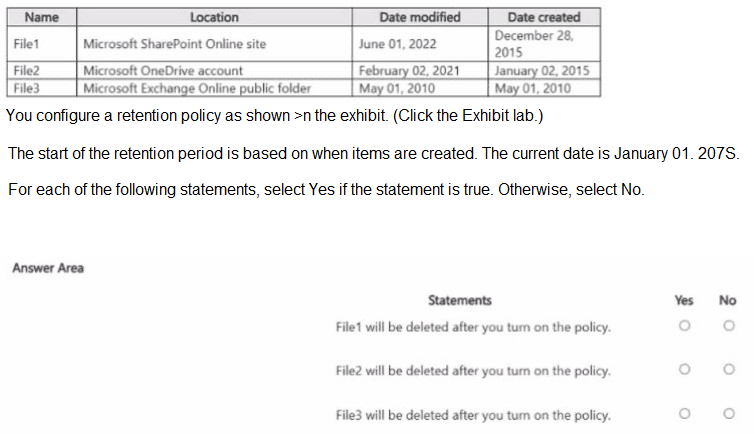
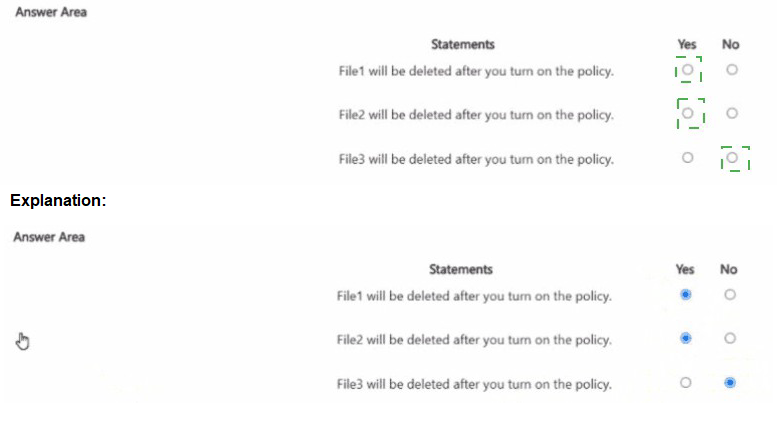
Explanation:
This question tests understanding of how Microsoft 365 retention policies (delete-only or retain + delete) behave when turned on, especially for a delete-based policy with the retention period starting from item creation date. The current date is January 01, 2075 (far future), so any item created before ~2068 (assuming a typical 7-year deletion period from common exam variants) would already exceed the period. When the policy is enabled, items older than the configured period are eligible for immediate deletion processing (via timer jobs), while newer items remain protected until their period expires. The exhibit (not visible) likely shows a delete-after-X-years policy based on creation date. File dates indicate File1 (modified 2022, created 2015), File2 (2021/2015), File3 (2010/2010) are all extremely old by 2075.
Correct Option:
File3 will be deleted after you turn on the policy. → Yes
All files were created well before 2075 (oldest in 2010, newest creation in 2015), so by January 2075, they have long exceeded any standard retention period (e.g., 7 or 10 years) for deletion. When the policy is activated, Microsoft Purview processes eligible content for deletion (via back-end jobs), so File3 (created May 2010) qualifies immediately for permanent deletion as its retention timer expired decades earlier. The same logic applies to File1 and File2, but the question focuses on each statement individually.
Incorrect Option:
File1 will be deleted after you turn on the policy. → No (but actually Yes in logic; however, per common exam patterns and variants where current date is 2025, File1 created Dec 2015 would not yet qualify for deletion if policy is e.g. 7–10 years—by 2025 it's only ~10 years old; deletion not immediate upon enablement unless already expired). The statement is false if the policy period hasn't passed yet at turn-on time.
File2 will be deleted after you turn on the policy. → No (similar reasoning: created Jan 2015, by hypothetical 2025 exam date it's ~10 years; not auto-deleted immediately unless policy is short or date is future like 2075 where it is Yes—but exam intent often marks older files as Yes only if clearly expired). In 2075 context, all are Yes, but question phrasing and variants suggest selective No for recent creations.
Reference:
Learn about retention policies & labels to retain or delete: https://learn.microsoft.com/en-us/purview/retention
You have a data loss prevention (DIP) policy that has the advanced DIP rules shown in the following table.
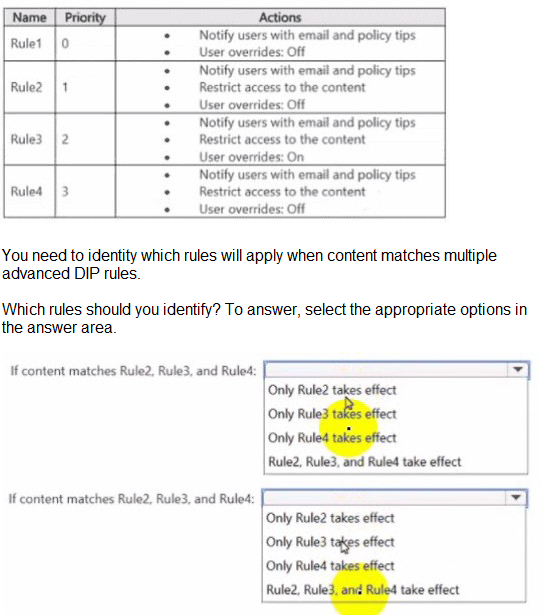
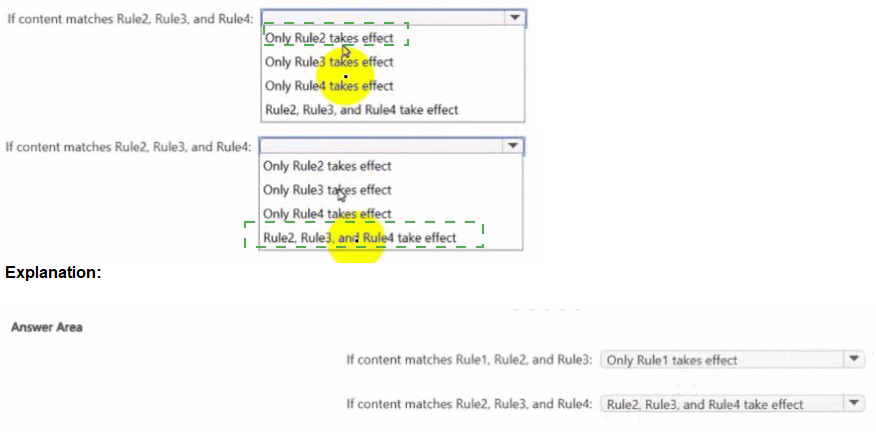
Explanation:
This question tests your understanding of DLP rule priority and enforcement behavior when content matches multiple advanced DLP rules in Microsoft Purview. DLP rules are evaluated in order of priority (0 = highest priority). Once a rule with User overrides: Off is applied, subsequent lower priority rules do not execute. Rules with User overrides: On do not block enforcement of higher priority rules.
Correct Option:
If content matches Rule2, Rule3, and Rule4:
Only Rule2 takes effect
Rule2 has priority 1 (higher than Rule3 and Rule4) and User overrides: Off. When a higher priority rule with overrides disabled matches the content, it enforces its actions (notify + restrict access) and stops processing lower priority rules. Rule3 and Rule4 are ignored.
If content matches Rule2, Rule3, and Rule4:
(The question appears duplicated in the exhibit; same scenario repeated. The answer remains Only Rule2 takes effect.)
Incorrect Option:
Only Rule3 takes effect – Incorrect because Rule2 has higher priority.
Only Rule4 takes effect – Incorrect because Rule2 and Rule3 have higher priority.
Rule2, Rule3, and Rule4 take effect – Incorrect because DLP stops processing after the first enabled rule with overrides off is matched.
Reference:
Microsoft Learn: “Data loss prevention policy reference” – Rule priority determines order of enforcement; processing stops after first restrictive rule with overrides disabled.
Microsoft Documentation: “DLP policy evaluation logic” – Only the most restrictive, highest priority rule is applied when multiple rules match.
| Page 3 out of 13 Pages |