Topic 4: Misc. Questions
You have a Microsoft 365 E5 subscription that uses Microsoft Defender for Cloud Apps and Conditional Access policies. You need to block access to cloud apps when a user is assessed as high risk. Which type of policy should you create in the Microsoft Defender for Cloud Apps?
A. OAuth app policy
B. anomaly detection polio
C. access policy
D. activity policy
You have an Azure AD tenant that contains the users shown in the following table.
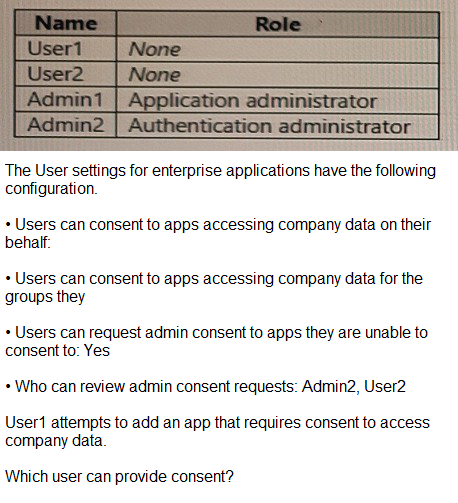
A. User1
B. User2
C. Admin1
D. Admin2
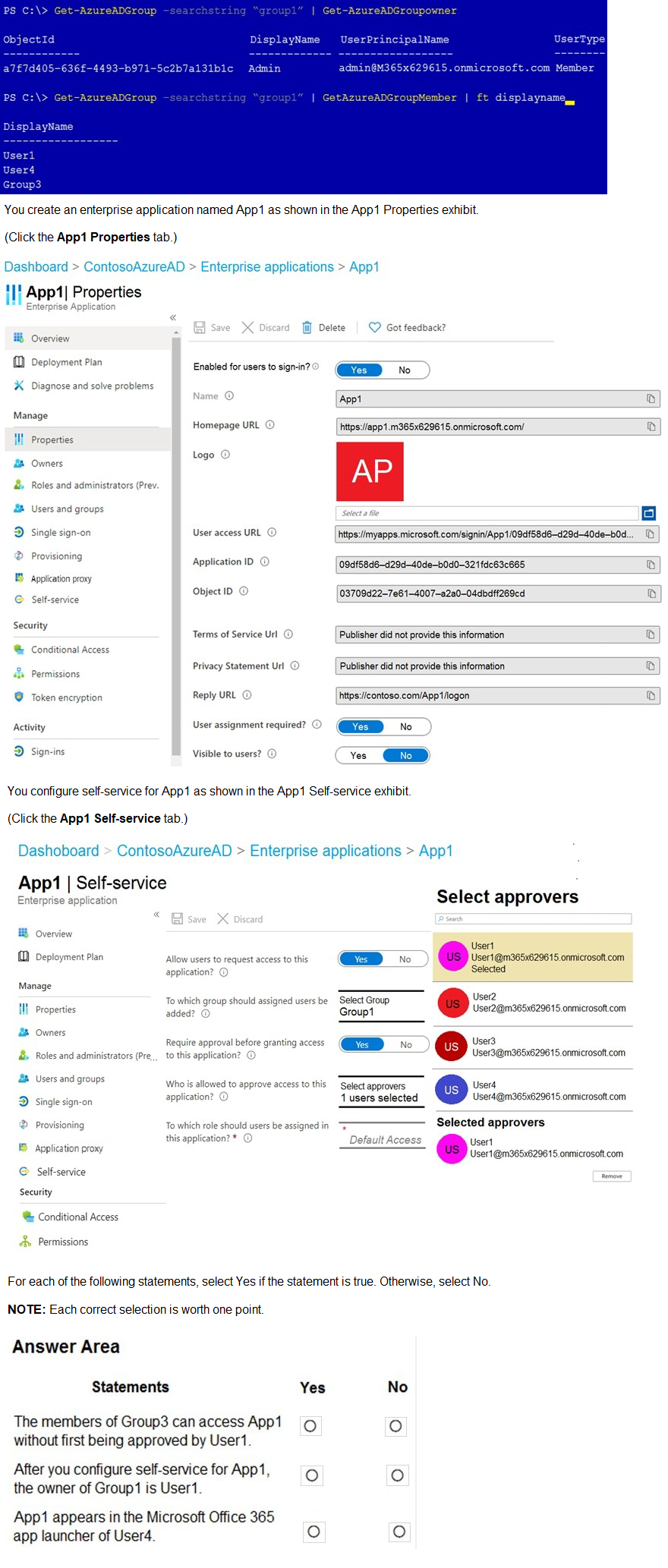
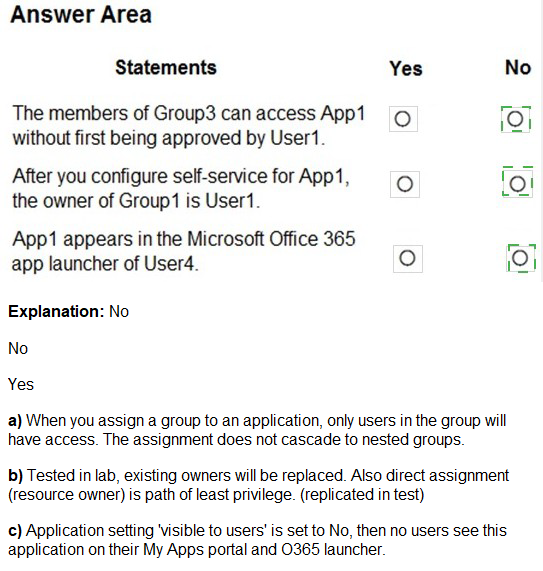
You have a Microsoft 365 tenant that contains a group named Group1 as shown in the Group1 exhibit. (Click the Group1 tab.)
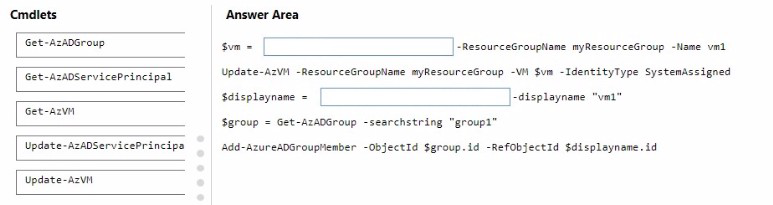
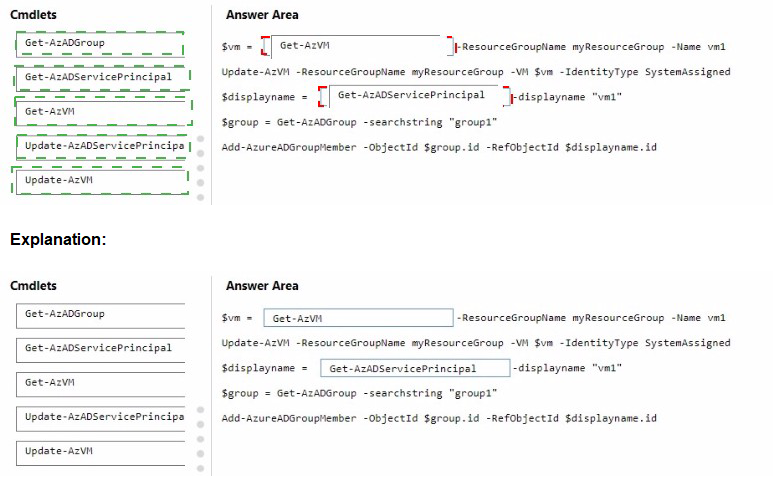
You have an Azure subscription that is linked to a Microsoft Entra tenant named contoso.com. The subscription contains a group named Group1 and a virtual machine named VM1.
You need to meet the following requirements:
- Enable a system-assigned managed identity for VM1.
- AddVM1 to Group1.
NOTE: Each correct selection is worth one point.
You create a new Microsoft 365 E5 tenant.
You need to ensure that when users connect to the Microsoft 365 portal from an
anonymous IP address, they are prompted to use multi-factor authentication (MFA).
What should you configure?
A. a sign-in risk policy
B. a user risk policy
C. an MFA registration policy
You have an Azure AD tenant.
You need to bulk create 25 new user accounts by uploading a template file.
Which properties are required in the template file?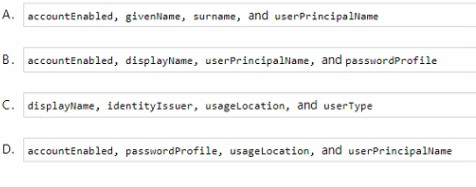
A. Option A
B. Option B
C. Option C
D. Option D
You have a Microsoft 365 E5 subscription that uses Microsoft Defender for Cloud Apps.
You need to identify which users access Facebook from their devices and browsers. The
solution must minimize administrative effort.
What should you do first?
A. From the Microsoft Defender for Cloud Apps portal, unsanctioned Facebook
B. Create an app configuration policy in Microsoft Endpoint Manager
C. Create a Defender for Cloud Apps access policy
D. Create a Conditional Access policy
You have an Azure AD tenant that contains an access package named Package1 and a user named User1. Package1 is configured as shown in the following exhibit.
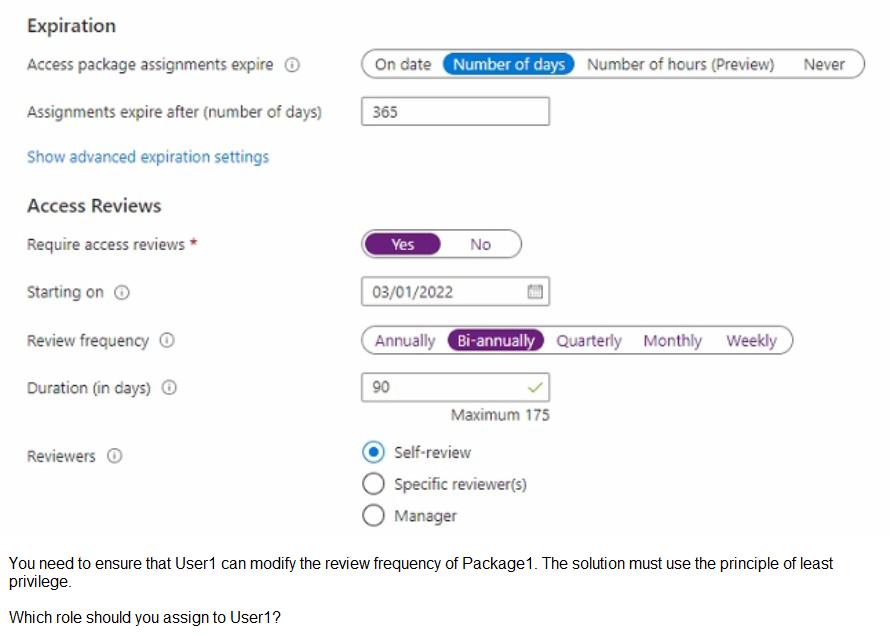
A. Privileged role administrator
B. User administrator
C. External Identity Provider administrator
D. Security administrator
Your company has a Microsoft 365 tenant.
The company has a call center that contains 300 users. In the call center, the users share desktop computers.
and might use a different computer every day. The call center computers are NOT
configured for biometric
identification.
The users are prohibited from having a mobile phone in the call center.
You need to require multi-factor authentication (MFA) for the call center users when they
access Microsoft 365
services.
What should you include in the solution?
A. a named network location
B. the Microsoft Authenticator app
C. Windows Hello for Business authentication
D. FIDO2 tokens
You have a Microsoft 365 tenant.
You have an Active Directory domain that syncs to the Azure Active Directory {Azure AD)
tenant.
Users connect to the internet by using a hardware firewall at your company. The users
authenticate to the firewall by using their Active Directory credentials.
You plan to manage access to external applications by using Azure AD.
You need to use the firewall logs to create a list of unmanaged external applications and
the users who access them.
What should you use to gather the information?
A. Cloud App Discovery in Microsoft Defender for Cloud Apps
B. enterprise applications in Azure AD
C. access reviews in Azure AD
D. Application Insights in Azure Monitor
| Page 12 out of 36 Pages |