Topic 4: Misc. Questions
You have a Microsoft 365 E5 subscription that contains a Microsoft SharePoint Online site
named Site!. Site! hosts PDF files
You need to prevent users from printing the files directly from Sitel.
Which type of policy should you create in the Microsoft Defender for Cloud Apps portal?
A. activity policy
B. file policy
C. access policy
D. session policy
You have an Azure subscription that contains a virtual machine named VM1 and an Azure key vault named Vault1. VM1 has a system-assigned managed identity. You need to ensure that VM1 can retrieve the values of secrets stored in Vault 1. The solution must minimize administrative effort. What should you do first?
A. Configure the Resource access settings for Vault1.
B. Configure the permissions model for Vault1
C. Add a user-assigned managed identity to VM1.
D. Assign an Azure role to VM1.
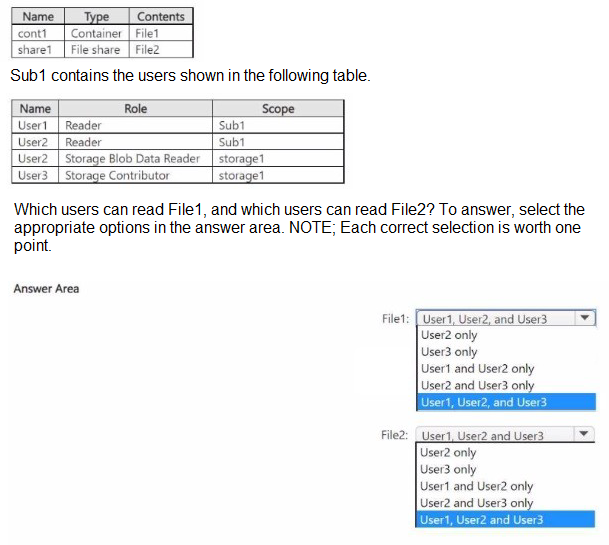
You have an Azure subscription named Sub1 that contains three users named User1. User2, and User3. Sub1 has a storage account named storage1 that contains the resources shown in the following table.
You have a Microsoft 365 tenant.
All users must use the Microsoft Authenticator app for multi-factor authentication (MFA)
when accessing Microsoft 365 services.
Some users report that they received an MFA prompt on their Microsoft Authenticator app
without initiating a sign-in request.
You need to block the users automatically when they report an MFA request that they did
not Initiate.
Solution: From the Azure portal, you configure the Block/unblock users settings for multifactor
authentication (MFA).
Does this meet the goal?
A. Yes
B. No
You have a Microsoft 365 tenant.
In Azure Active Directory (Azure AD), you configure the terms of use.
You need to ensure that only users who accept the terms of use can access the resources
in the tenant. Other
users must be denied access.
What should you configure?
A. an access policy in Microsoft Cloud App Security
B. Terms and conditions in Microsoft Endpoint Manager
C. a conditional access policy in Azure AD
D. a compliance policy in Microsoft Endpoint Manager
You have a Microsoft 365 tenant.
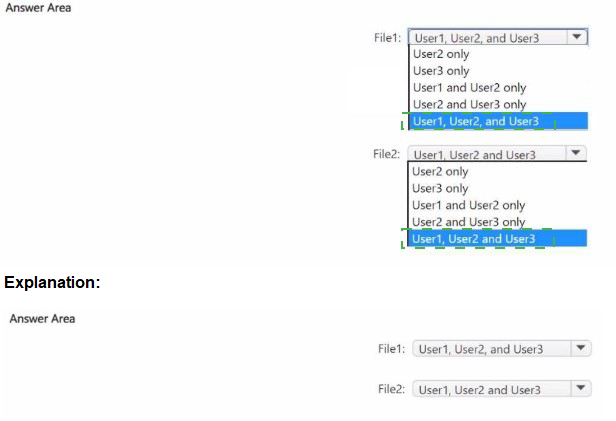
The Azure Active Directory (Azure AD) tenant syncs to an on-premises Active Directory
domain. The domain
contains the servers shown in the following table.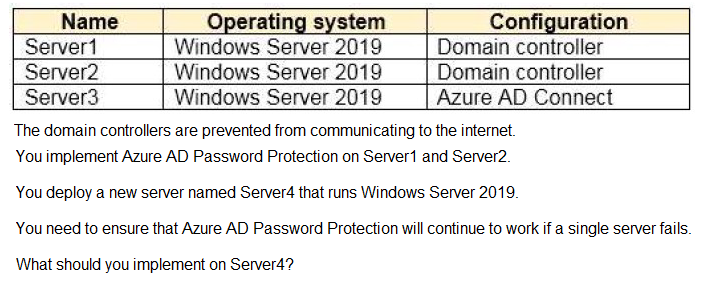
A. Azure AD Connect
B. Azure AD Application Proxy
C. Password Change Notification Service (PCNS)
D. the Azure AD Password Protection proxy service
Note: This question is part of a series of questions that present the same scenario. Each
question in the series contains a unique solution that might meet the stated goals. Some
question sets might have more than one correct solution, while others might not have a
correct solution.
After you answer a question in this section, you will NOT be able to return to it. As a result,
these questions will not appear in the review screen.
You have a Microsoft 365 tenant.
All users must use the Microsoft Authenticator app for multi-factor authentication (MFA)
when accessing Microsoft 365 services.
Some users report that they received an MFA prompt on their Microsoft Authenticator app
without initiating a sign-in request.
You need to block the users automatically when they report an MFA request that they did
not initiate.
Solution: From the Microsoft Entra admin center, you configure the Notifications settings for
multi-factor authentication (MFA).
Does this meet the goal?
A. Yes
B. No
Your company has a Microsoft Entra tenant that contains a user named User 1.
The company has two departments named marketing and finance.
You need to grant permissions to User1 to manage only the users in the marketing
department.
What should you create first?
A. an administrative unit
B. a Microsoft 365 group
C. a management group
D. a resource group
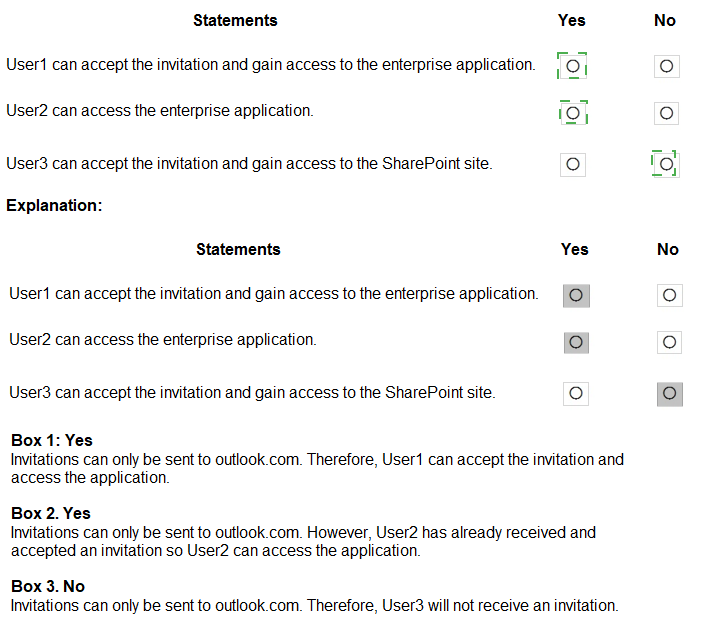
You have a Microsoft 365 tenant named contoso.com.
Guest user access is enabled.
Users are invited to collaborate with contoso.com as shown in the following table.
You have a Microsoft Entra tenant. You need to configure continuous access evaluation for app sign-ins and assign the configuration to users that are assigned the Application Administrator role. What should you configure?
A. a Conditional Access policy
B. the Admin consent settings
C. a sign-in risk policy
D. an access review
| Page 11 out of 36 Pages |