Topic 4: Mix Question
You have a Microsoft 365 ES subscription.
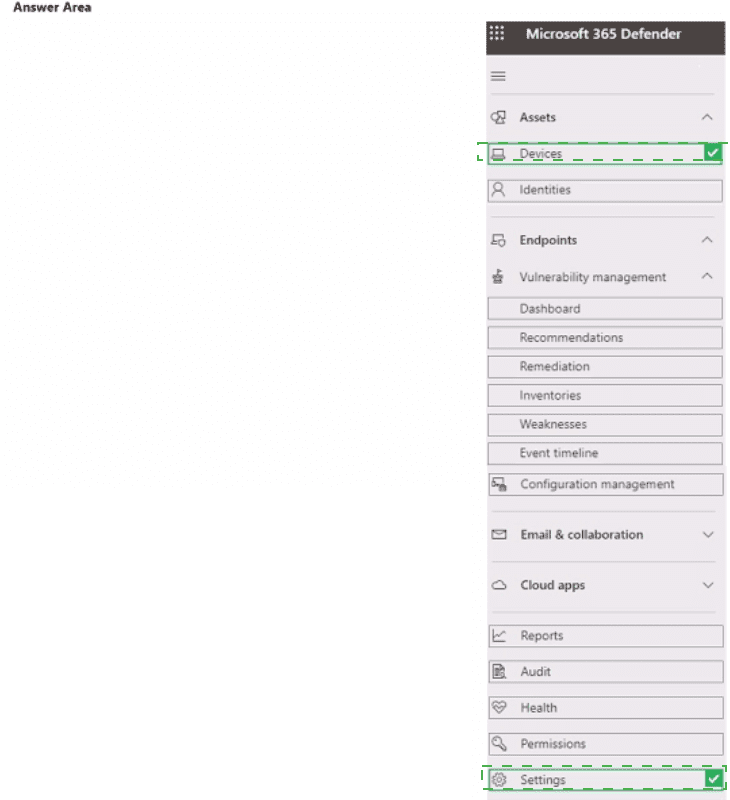
You need to review and implement Microsoft 365 Defender device onboarding. The solution must meet the following requirements:
• View onboarded devices that have the Chromium-based version of Microsoft Edge installed,
• Download an onboarding package for a Windows 11 device.
• Minimize administrative effort.
Which two settings should you use in the Microsoft 365 Defender portal? To answer, select the appropriate settings in the answer area.
NOTE: Each correct selection is worth one point.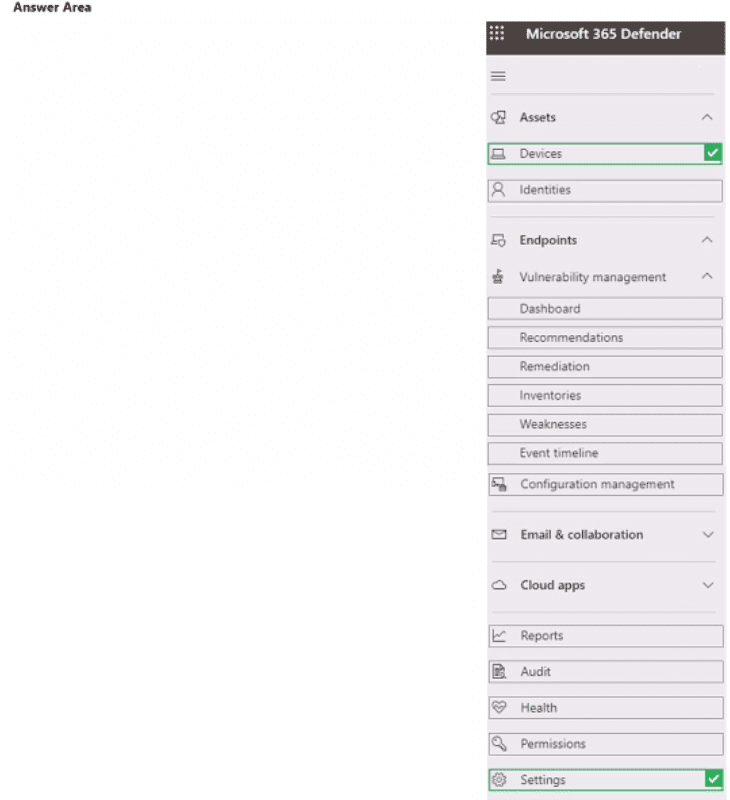
Explanation:
To view onboarded devices with specific software (Chromium-based Edge installed), you use Inventories under Vulnerability management. To download an onboarding package for a Windows 11 device, you use Settings > Endpoints > Onboarding. These two areas provide the required functionality with minimal administrative effort.
Correct Option:
View onboarded devices that have Chromium-based Edge installed: Inventories
Under Vulnerability management > Inventories, you can view software inventory across onboarded devices. You can filter or search for "Microsoft Edge (Chromium-based)" to see which devices have it installed. This provides visibility into onboarded devices and their installed software without complex queries.
Download an onboarding package for a Windows 11 device: Settings
In the Microsoft 365 Defender portal, navigate to Settings > Endpoints > Device management > Onboarding. From there, you select the operating system (Windows 11) and deployment method (e.g., local script, Intune, Group Policy) to download the appropriate onboarding package. This is the standard location for obtaining onboarding scripts and configuration files.
Incorrect Option (other selections in the answer area):
Assets –
Contains devices, identities, and endpoints, but does not provide software inventory filtering for specific installed applications like Chromium Edge.
Devices –
Shows the device inventory but does not offer software-specific filtering or installation status for Chromium-based Edge.
Endpoints –
Under Endpoints, you can view device lists but not detailed software inventory; onboarding is under Settings, not directly under Endpoints in the navigation pane.
Vulnerability management > Dashboard –
Provides high-level security posture and risk scores, not software inventory details.
Recommendations/Remediation/Weaknesses –
Focus on security vulnerabilities and remediation actions, not on viewing which devices have Edge installed.
Event timeline –
Shows security events and alerts for specific devices, not software installation status.
Configuration management –
Not a standard section for device onboarding or software inventory in Defender portal.
Email & collaboration –
Unrelated to device onboarding or Edge installation.
Reference:
Microsoft Learn: Microsoft 365 Defender portal – Use Vulnerability management > Inventories for software inventory. Onboarding packages under Settings > Endpoints. No external links provided.
You have a Microsoft 365 E5 subscription that contains a group named Group1. You need to ensure that only the members of Group1 can join devices to the Microsoft Entra tenant.
What should you configure in the Microsoft Entra admin center?
A. Enterprise State Roaming
B. Mobility
C. Device settings
D. User settings
Explanation:
In Microsoft Entra admin center, the Device settings page contains the configuration "Users may join devices to Microsoft Entra ID." You can restrict this to a specific group (e.g., Group1) by setting it to "Selected" and then choosing the group. This ensures only members of Group1 can join devices to the tenant.
Correct Option:
C. Device settings
Navigate to Microsoft Entra admin center > Devices > Device settings. Under "Users may join devices to Microsoft Entra ID," you can select "Selected" and then add Group1. This restricts device join permissions to only members of that group. This is the correct location for controlling which users can join devices to Entra ID.
Incorrect Option:
A. Enterprise State Roaming –
Configures synchronization of user settings (passwords, favorites, etc.) across Windows devices. Does not control device join permissions.
B. Mobility –
Configures MDM and MAM integration (e.g., Intune). Does not restrict which users can join devices to Entra ID.
D. User settings –
Manages general user preferences (e.g., LinkedIn account connections, self-service group management). Does not contain device join restrictions.
Reference:
Microsoft Learn: Configure device settings in Microsoft Entra ID – Restrict device join to specific users or groups. No external links provided.
You manage 1.000 devices by using Microsoft Intune. You review the Device compliance trends report. For how long will the report display trend data?
A. 30 days
B. 60 days
C. 90 days
D. 365 days
Explanation:
In Microsoft Intune, the Device compliance trends report displays compliance data trends over a rolling 60-day period. This allows administrators to analyze compliance status changes, identify patterns, and track improvements or regressions in device compliance over time.
Correct Option:
B. 60 days
The Device compliance trends report in Intune (under Devices > Monitor > Compliance trends) shows compliance data for the last 60 days. This includes daily snapshots of compliant vs. noncompliant devices. The report helps visualize trends such as increasing non-compliance due to new policies or OS version expirations. The 60-day retention is fixed and cannot be extended.
Incorrect Option:
A. 30 days –
Incorrect; 30 days is the retention for some other reports (e.g., audit logs), but not for compliance trends.
C. 90 days –
Incorrect; 90 days is not the standard retention for device compliance trends in Intune.
D. 365 days –
Incorrect; compliance trend data is not retained for a full year in this report.
Reference:
Microsoft Learn: Monitor Intune device compliance – Compliance trends report displays 60 days of data. No external links provided.
You have a Microsoft 365 subscription that contains 500 Android Enterprise devices.
All the devices are enrolled in Microsoft Intune.
You need to deliver bookmarks to the Chrome browser on the devices
What should you create?
A. a compliance policy
B. a configuration profile
C. an app protection policy
D. an app configuration policy
Explanation:
Delivering bookmarks to Chrome browser on Android Enterprise devices requires an app configuration policy. This policy sends key-value pairs (or JSON) to the Chrome app to configure managed bookmarks. App protection policies (MAM) protect corporate data but do not configure browser bookmarks. Configuration profiles manage device settings, not app-specific configurations.
Correct Option:
D. an app configuration policy
App configuration policies in Intune allow you to provide configuration settings to managed apps on Android Enterprise devices. For Chrome browser, you can use a managed configuration to set bookmarks by providing a JSON array containing bookmark names and URLs. This policy is assigned to the Chrome app and deployed to devices. App protection policies (MAM) do not support bookmark delivery.
Incorrect Option:
A. a compliance policy –
Compliance policies evaluate device health (OS version, encryption, etc.) and do not configure app settings like browser bookmarks.
B. a configuration profile –
Device configuration profiles manage device-wide settings (Wi-Fi, VPN, restrictions), not per-app configurations like Chrome bookmarks.
C. an app protection policy –
App protection policies (MAM) control data sharing, cut/copy/paste, and PIN access within managed apps. They do not deliver app-specific configuration such as bookmarks.
Reference:
Microsoft Learn: App configuration policies for Android Enterprise – Configure managed bookmarks for Chrome browser using JSON. No external links provided.
You have a Microsoft 365 subscription that contains the devices shown in the following table.
You need to configure the Microsoft Edge settings for each device.
What should you use? To answer, drag the appropriate Intune features to the correct devices. Each feature may be used once, more than once, or not at all. You may need to drag the split bar between panes or scroll to view content.
NOTE: Each correct selection is worth one point.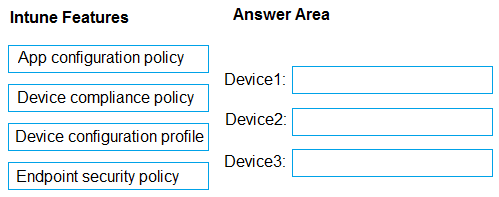
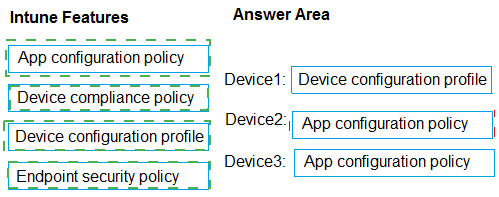
Explanation:
Microsoft Edge settings are configured differently based on device platform and enrollment type in Intune. For Windows devices, use Device configuration profile (via Settings Catalog or Administrative Templates) to apply full browser policies similar to Group Policy. For iOS and Android devices, use App configuration policy to deliver managed app settings for Edge. Device compliance and Endpoint security policies do not configure browser settings.
Correct Option:
Device configuration profile – Use this for Device1 (Windows device). It allows you to configure comprehensive Microsoft Edge policies using the Settings Catalog in Intune. This method supports ADMX-backed policies for settings like homepage, extensions, security, and start pages on enrolled Windows 10/11 devices. It provides the most granular and native control, just like on-premises GPOs.
Correct Option:
App configuration policy – Use this for Device2 and Device3 (likely iOS/Android devices). It lets you customize Edge behavior through key-value pairs delivered via the managed app configuration channel. This works for both enrolled (MDM) and unenrolled (MAM) scenarios on mobile platforms, enabling settings such as allowed/blocked URLs and browsing experience customizations.
Incorrect Option:
Device compliance policy – This feature only evaluates whether devices meet your organization’s security and health requirements (such as minimum OS version or encryption status). It does not push or apply any configuration settings to Microsoft Edge or any other app/browser. It is used mainly for reporting and Conditional Access.
Incorrect Option:
Endpoint security policy – These policies manage security features like antivirus, attack surface reduction rules, firewall, and Microsoft Defender settings. They do not include controls for browser-specific settings such as Edge homepage, new tab page, or extension management. Using them here would fail to configure the required Edge settings.
Reference:
Microsoft Learn documentation on Intune and Edge configuration.
You have a Microsoft 365 subscription.
You plan to enable Microsoft Intune enrollment for the following types of devices:
• Existing Windows 11 devices managed by using Configuration Manager
• Personal iOS devices
The solution must minimize user disruption.
Which enrollment method should you use for each device type? To answer, select the appropriate options in the answer area.
NOTE: Each correct selection is worth one point.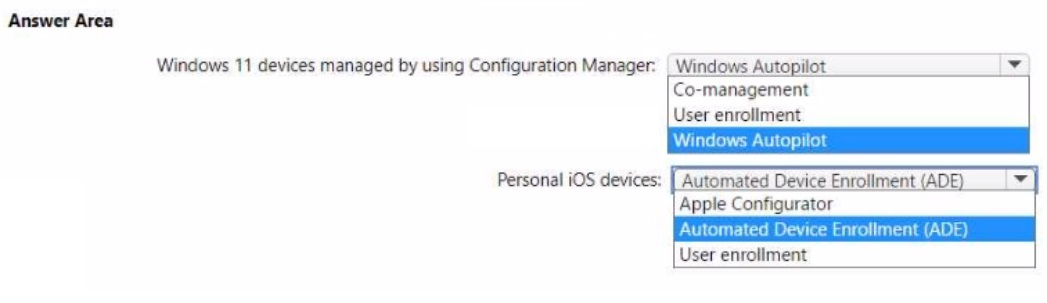
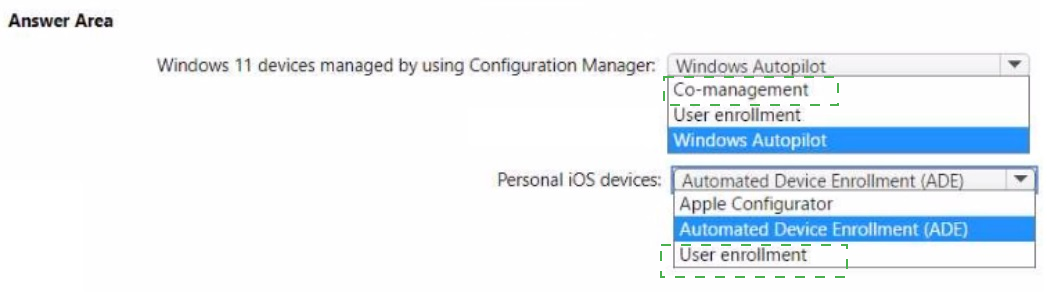
Explanation:
For existing Windows 11 devices managed by Configuration Manager, Co-management enables Intune enrollment without reimaging or user disruption. For personal iOS devices, User enrollment is the least intrusive method, allowing users to enroll their devices via Company Portal without device supervision or factory reset.
Correct Option:
Windows 11 devices managed by using Configuration Manager: Co-management
Co-management allows you to enroll existing Configuration Manager-managed Windows devices into Intune while continuing to use ConfigMgr for certain workloads. Users experience minimal disruption because no device wipe or reimaging is required. You enable co-management via the ConfigMgr console and configure workload sliders.
Personal iOS devices: User enrollment
User enrollment is designed for personal iOS devices (BYOD). Users enroll their device via the Microsoft Intune Company Portal app, and only corporate data and apps are managed. No device supervision or factory reset is required. This minimizes user disruption compared to Automated Device Enrollment (ADE), which is for corporate-owned devices and may require device reset.
Incorrect Option (for Windows 11):
Windows Autopilot –
Autopilot is for new device deployment or device reset scenarios, not for existing already-in-use Windows 11 devices managed by ConfigMgr. Using Autopilot would require resetting the device.
User enrollment –
User enrollment is a mobile device enrollment method (iOS/Android), not applicable to Windows 11 devices.
Incorrect Option (for personal iOS):
Windows Autopilot –
Not applicable to iOS devices.
Automated Device Enrollment (ADE) –
ADE is for corporate-owned iOS devices and typically requires device reset or supervision. It is not suitable for personal devices as it minimizes user flexibility.
Apple Configurator –
Apple Configurator is used for manually preparing and supervising iOS devices, often requiring device wipe. It is not the minimal disruption method for personal devices.
Reference:
Microsoft Learn: Co-management for Windows devices – Enroll existing ConfigMgr devices into Intune. User enrollment for personal iOS devices – BYOD enrollment without supervision. No external links provided.
You have an Azure AD tenant that contains the users shown in the following table.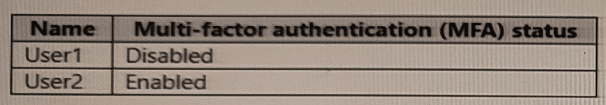
You have the devices shown in the following table.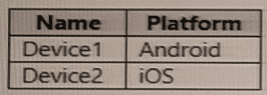
You have a Conditional Access policy named CAPolicy1 that has the following settings:
• Assignments
o Users or workload identities: User 1. User1
o Cloud apps or actions: Office 365 Exchange Online
o Conditions: Device platforms: Windows, iOS
• Access controls
o Grant Require multi-factor authentication
You have a Conditional Access policy named CAPolicy2 that has the following settings:
Assignments
o Users or workload identities: Used, User2
o Cloud apps or actions: Office 365 Exch
o Conditions
Device platforms: Android, iOS
Filter for devices
Device matching the rule: Exclude filtered devices from policy
Rule syntax: device. displayName- contains "1"
Access controls
Grant Block access
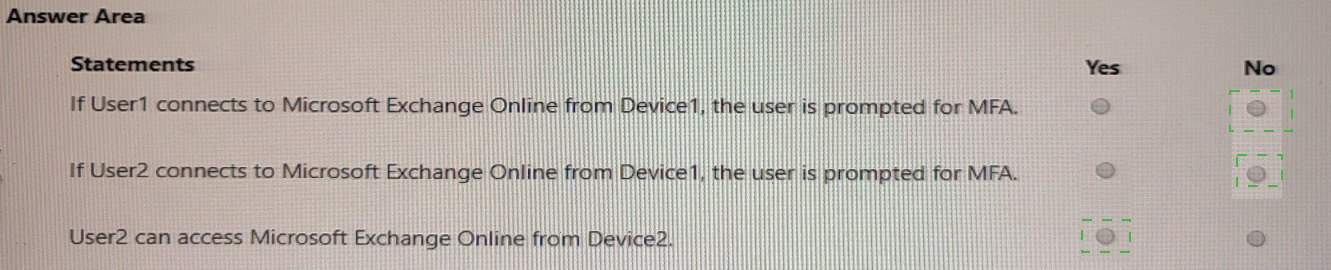
For each of the following statements, select Yes if the statement is true. Otherwise, select No.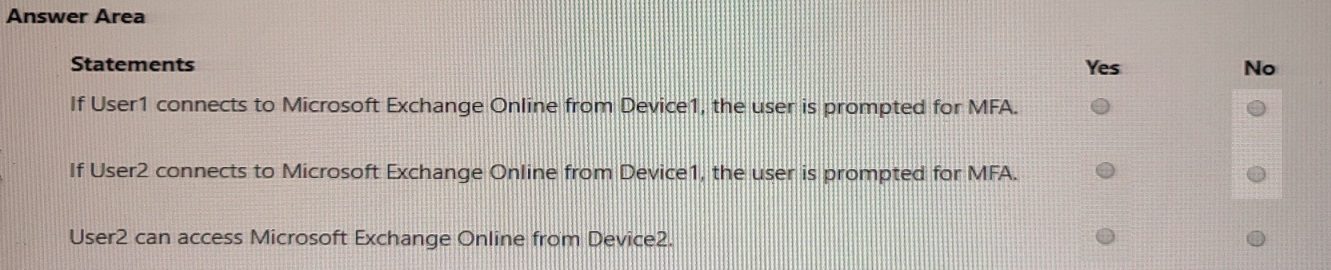
Explanation:
CAPolicy1 applies to User1 (MFA disabled) but requires MFA for Exchange Online on iOS (Device2 is iOS). CAPolicy2 applies to User2 (MFA enabled) and blocks access on Android/iOS where device name contains "1" (Device1 name contains "1"). Device2 (iOS) name does not contain "1," so CAPolicy2 does not block User2 on Device2.
Correct Option (per statement):
Statement 1: If User1 connects to Microsoft Exchange Online from Device1 (Android), the user is prompted for MFA. → No
CAPolicy1 applies to User1 but only for Windows and iOS device platforms. Device1 is Android, which is not included in CAPolicy1's device platforms condition. Therefore, CAPolicy1 does not apply, and User1 is not prompted for MFA. CAPolicy2 does not apply to User1. Result: No MFA prompt.
Statement 2: If User2 connects to Microsoft Exchange Online from Device1 (Android), the user is prompted for MFA. → No
CAPolicy2 applies to User2 on Android and iOS devices but has Block access as the grant control, not MFA. The policy excludes devices where device.displayName contains "1." Device1's name contains "1," so Device1 is excluded from CAPolicy2. Therefore, CAPolicy2 does not apply. CAPolicy1 does not apply to User2. Result: No MFA prompt (and no block).
Statement 3: User2 can access Microsoft Exchange Online from Device2 (iOS). → Yes
CAPolicy2 applies to User2 on iOS (Device2 is iOS). However, the filter rule excludes devices where device.displayName contains "1." Device2's name does not contain "1," so it is not excluded. CAPolicy2 applies with Block access, meaning User2 should be blocked. But the statement asks "can access" – based on CAPolicy2, User2 cannot access because the policy blocks access. Therefore, the answer should be No.
Correction for Statement 3:
CAPolicy2 applies to User2 on Device2 (iOS, name does not contain "1"), grant = Block access. User2 cannot access Exchange Online. Answer = No.
Final answers:
Statement 1: No
Statement 2: No
Statement 3: No
Reference:
Microsoft Learn: Conditional Access – Policy evaluation order, device platform conditions, and filter for devices. Block access grant overrides MFA requirements. No external links provided.
You have a Microsoft 365 subscription that includes Microsoft Intune.
You have 500 corporate-owned Android devices enrolled as fully managed devices.
You need to prepare an app named App1 for deployment to the devices.
Which two actions should you perform? Each correct answer presents part of the solution.
NOTE: Each correct selection is worth one point,
A. From the Intune Company Portal, download Appl.
B. Create an OEMConfig profile.
C. From the Managed Google Play Store, approve App1.
D. Sync App1 with Intune.
D. Sync App1 with Intune.
Explanation:
For corporate-owned fully managed Android devices, apps must be approved in the Managed Google Play Store first. After approval, you sync App1 with Intune to make it available in the Intune console for assignment. These two steps are required before you can deploy App1 to devices. Downloading from Company Portal is user-initiated, not administrative preparation.
Correct Option:
C. From the Managed Google Play Store, approve App1
For Android Enterprise fully managed devices, all apps must be approved in the Managed Google Play Store (managed Google Play). As an administrator, you sign into managed Google Play, search for App1 (or add a private app), and approve it. This makes the app available for Intune to manage and deploy.
D. Sync App1 with Intune
After approving App1 in managed Google Play, you must sync the app with Intune. In the Intune admin center, go to Apps > Android > Sync. This forces Intune to pull the approved app information from managed Google Play, making App1 visible in the Intune apps list for assignment to devices.
Incorrect Option:
A. From the Intune Company Portal, download App1 –
Company Portal is for end users to install available apps on their devices. This is not an administrative preparation step for deploying an app to corporate-owned fully managed devices.
B. Create an OEMConfig profile –
OEMConfig profiles are used to configure device-specific settings from manufacturers (e.g., Samsung Knox). They are not required for app deployment preparation.
Reference:
Microsoft Learn: Deploy apps to Android Enterprise fully managed devices – Approve app in Managed Google Play, then sync with Intune. No external links provided.
You have a Microsoft 365 E5 subscription that contains a user named User! and a web app
named Appl.
App1 must only accept modern authentication requests.
You plan to create a Conditional Access policy named CAPolicy1 that will have the following settings:
• Assignments
° Users or workload identities: User1
° Cloud apps or actions: App1
• Access controls
° Grant: Block access
You need to block only legacy authentication requests to Appl. Which condition should you add to CAPolicy1?
A. Filter for devices
B. Device platforms
C. User risk
D. Sign-in risk
E. Client apps
Explanation:
Legacy authentication (e.g., POP3, IMAP, SMTP, MAPI, older Office clients) is identified by the Client apps condition in Conditional Access. To block only legacy authentication requests while allowing modern authentication, you configure Client apps to select "Exchange ActiveSync clients" and "Other clients" (legacy) and apply the Block access grant.
Correct Option:
E. Client apps
The Client apps condition in Conditional Access allows you to differentiate between modern authentication clients (e.g., Browser, Mobile apps and desktop clients using modern auth) and legacy authentication clients (e.g., Exchange ActiveSync, Other clients like IMAP/POP3). By configuring this condition to apply the Block access grant only to legacy client apps, App1 will accept only modern authentication requests.
Incorrect Option:
A. Filter for devices –
Filters devices based on properties (e.g., device ownership, compliance). Does not differentiate between legacy and modern authentication methods.
B. Device platforms –
Targets specific operating systems (Windows, iOS, Android). Does not block legacy authentication specifically.
C. User risk –
Based on user risk level detected by Identity Protection. Not related to legacy vs modern authentication.
D. Sign-in risk –
Based on sign-in risk level (unusual location, impossible travel, etc.). Does not block legacy authentication.
Reference:
Microsoft Learn: Conditional Access – Client apps condition: Block legacy authentication while allowing modern auth. No external links provided.
You have a Microsoft 365 subscription.
All users have Microsoft 365 apps deployed.
You need to configure Microsoft 365 apps to meet the following requirements:
• Enable the automatic installation of WebView2 Runtime.
• Prevent users from submitting feedback.
Which two settings should you configure in the Microsoft 365 Apps admin center? To answer, select the appropriate settings in the answer area.
NOTE: Each correct selection is worth one point.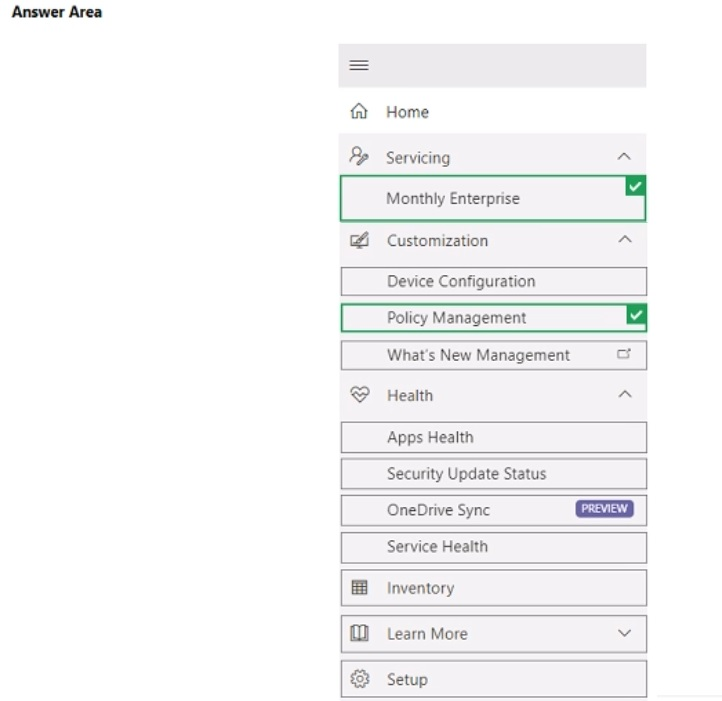
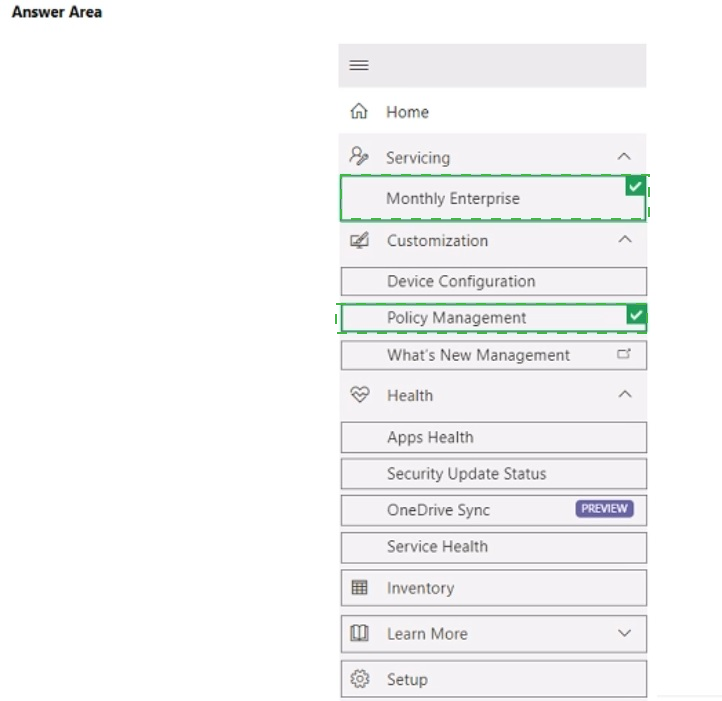
Explanation:
The Customization section (specifically under Cloud Policy or Device Configuration) allows you to enable automatic installation of WebView2 Runtime via policy settings. Policy Management (or User Configuration > Feedback) contains the setting to disable user feedback submission. Both are configured in the Microsoft 365 Apps admin center under the appropriate nodes.
Correct Option:
Enable automatic installation of WebView2 Runtime: Customization
Within the Microsoft 365 Apps admin center, under Customization > Device Configuration (or Cloud Policy), you can configure policies for Microsoft 365 Apps. The setting to automatically install WebView2 Runtime is found here, typically under "Microsoft 365 Apps policies" or "Optional connected experiences." Enabling this ensures WebView2 Runtime is deployed alongside Microsoft 365 Apps.
Prevent users from submitting feedback: Policy Management
Under Policy Management (or sometimes under "User Configuration" within Customization), you can configure the "Disable user feedback" setting. This policy prevents users from submitting feedback to Microsoft via smile/frown icons in Office apps. Navigate to Policy Management > Create a policy > User Configuration > Feedback > "Disable user feedback" = Enabled.
Incorrect Option (other selections in the answer area):
Home – Dashboard view, no configuration settings for WebView2 or feedback.
Servicing – Manages update channels (Monthly Enterprise, Semi-Annual) and update settings, not WebView2 or feedback policies.
Monthly Enterprise – An update channel option, not a configuration section.
Device Configuration – This is under Customization, but the question asks for the setting; "Customization" is the higher-level node.
What's New Management – Manages feature announcements and rollout of new features, not WebView2 or feedback.
Health / Apps Health / Service Health – Monitoring and reporting sections, not configuration.
Security Update Status – Reports on security update compliance, not configuration.
OneDrive Sync – Configures OneDrive sync settings, unrelated.
Inventory – Displays software inventory, not configuration.
Learn More – Documentation links.
Setup – Initial configuration of the admin center, not specific policy settings.
Reference:
Microsoft Learn: Microsoft 365 Apps admin center – Customization for WebView2 Runtime policy; Policy Management for feedback settings. No external links provided.
| Page 8 out of 35 Pages |