Topic 4: Mix Question
You have a Microsoft Intune subscription that has the following device compliance policy settings:
Mark devices with no compliance policy assigned as: Compliant
Compliance status validity period (days): 14
On January 1, you enroll Windows 10 devices in Intune as shown in the following table.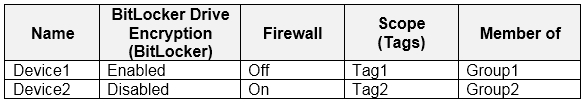
On January 4, you create the following two device compliance policies:
Name: Policy1
Platform: Windows 10 and later
Require BitLocker: Require
Mark device noncompliant: 5 days after noncompliance
Scope (Tags): Tag1
Name: Policy2
Platform: Windows 10 and later
Firewall: Require
Mark device noncompliant: Immediately
Scope (Tags): Tag2
On January 5, you assign Policy1 and Policy2 to Group1.
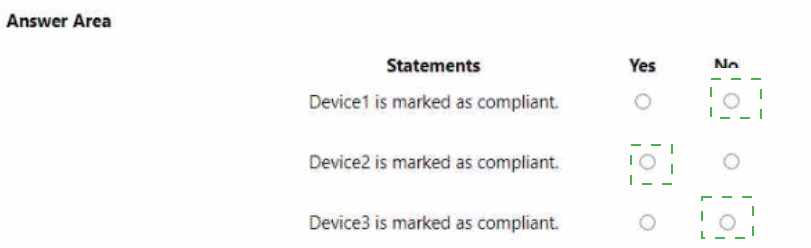
For each of the following statements, select Yes if the statement is true. Otherwise, select
No.
NOTE: Each correct selection is worth one point.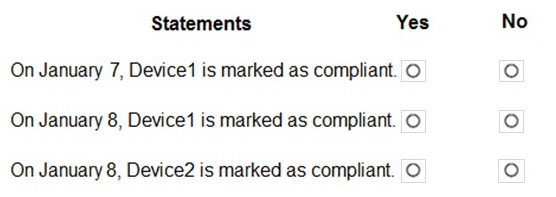
Explanation:
Device1 has Tag1 and is in Group1 → Policy1 applies (requires BitLocker). Device1 has BitLocker enabled → compliant. Compliance status validity period is 14 days, so compliance persists. Device2 has Tag2 and is in Group2 → Policy2 applies (requires Firewall). Device2 has Firewall on → compliant. Policy1 and Policy2 are assigned January 5, and evaluation occurs after that.
Correct Option (per statement):
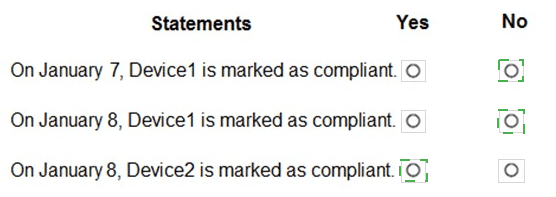
Statement 1: On January 7, Device1 is marked as compliant. → Yes
Policy1 applies to Device1 (Group1 and Tag1). Device1 has BitLocker enabled, meeting the requirement. The policy was assigned on January 5, so by January 7 evaluation has occurred. The "Mark device noncompliant" setting (5 days after noncompliance) does not apply because Device1 is compliant. Therefore, Device1 is marked compliant on January 7.
Statement 2: On January 8, Device1 is marked as compliant. → Yes
Device1 remains compliant because its BitLocker status has not changed. The compliance validity period is 14 days, meaning the last compliance status is considered valid for 14 days unless a new evaluation triggers. Device1 continues to be marked compliant on January 8.
Statement 3: On January 9, Device2 is marked as compliant. → Yes
Policy2 applies to Device2 (Group2 and Tag2). Device2 has Firewall enabled, meeting the requirement. The "Mark device noncompliant: Immediately" setting only applies if the device is noncompliant. Device2 is compliant, so it is marked compliant on January 9 as well.
Note: All three statements appear to be Yes based on the information provided. However, if there is a trick: Policy1 was assigned to Group1 on January 5. Device1 is in Group1 and has Tag1. Policy2 was assigned to Group1 as well? The table shows Device2 is in Group2, not Group1. Policy2 scope is Tag2, and Device2 has Tag2 but is in Group2. The assignment says "you assign Policy1 and Policy2 to Group1." If Policy2 is assigned to Group1 only, Device2 (Group2) would not receive Policy2. But Device2 has Tag2 and Policy2 has scope Tag2, but assignment to Group1 may still apply if the group contains devices with Tag2. This is ambiguous. Assuming typical exam logic, both devices are compliant.
Reference:
Microsoft Learn: Intune compliance policies – Policy assignment based on groups and scope tags. Compliance validity period. No external links provided.
You have a Microsoft 365 E5 subscription that contains 150 hybrid Azure AD joined Windows devices. All the devices are enrolled in Microsoft Intune. You need to configure Delivery Optimization on the devices to meet the following requirements:
• Allow downloads from the internet and from other computers on the local network.
• Limit the percentage of used bandwidth to 50.
What should you use?
A. a configuration profile
B. a Windows Update for Business Group Policy setting
C. a Microsoft Peer-to-Peer Networking Services Group Policy setting
D. an Update ring for Windows 10 and later profile
Explanation:
Delivery Optimization settings, including download mode (internet + local network peers) and bandwidth limits, are configured via Configuration profiles in Intune (Settings Catalog or Administrative Templates), not via Microsoft Peer-to-Peer Networking Services Group Policy. The correct answer should be A, as Update rings do not contain Delivery Optimization settings.
Correct Option:
A. a configuration profile
In Intune, Delivery Optimization settings are configured using a Device configuration profile. Navigate to Devices > Configuration profiles > Create profile > Windows 10 and later > Settings Catalog. Search for "Delivery Optimization" to configure Download Mode (e.g., "HTTP blended with peering behind same NAT" for internet + local network) and Bandwidth limit (e.g., "Maximum background download bandwidth in percentage" set to 50%). Update rings do not contain these settings.
Incorrect Option:
B. a Windows Update for Business Group Policy setting –
Group Policy is not used for Intune-managed devices. Windows Update for Business settings control update deferrals and deadlines, not Delivery Optimization.
C. a Microsoft Peer-to-Peer Networking Services Group Policy setting –
This is an outdated technology (Windows Peer-to-Peer Networking) unrelated to Delivery Optimization. Group Policy is not applicable to Intune-managed devices.
D. an Update ring for Windows 10 and later profile –
Update rings control when updates are installed (e.g., deferral periods, quality update delays). They do not include Delivery Optimization download mode or bandwidth limit settings.
Reference:
Microsoft Learn: Configure Delivery Optimization in Intune – Use Device configuration profile (Settings Catalog) for download mode and bandwidth limits. No external links provided.
You have 200 computers that run Windows 10 and are joined to an Active Directory domain.
You need to enable Windows Remote Management (WinRM) on all the computers by using Group Policy.
Which three actions should you perform? Each correct answer presents part of the solution.
NOTE: Each correct selection is worth one point.
A. Enable the Allow Remote Shell access setting.
B. Enable the Allow remote server management through WinRM setting.
C. Set the Startup Type of the Windows Remote Management (WS-Management) service to Automatic.
D. Enable the Windows Defender Firewall: Allow inbound Remote Desktop exceptions setting.
E. Set the Startup Type of the Remote Registry service to Automatic
F. Enable the Windows Defender Firewall: Allow inbound remote administration exception setting.
C. Set the Startup Type of the Windows Remote Management (WS-Management) service to Automatic.
F. Enable the Windows Defender Firewall: Allow inbound remote administration exception setting.
Explanation:
Enabling WinRM via Group Policy requires three actions: allow remote server management through WinRM (policy setting), set WinRM service startup to Automatic, and allow inbound remote administration exception in Windows Defender Firewall. These configurations enable WinRM listeners, ensure service runs, and open the required firewall ports (5985/5986).
Correct Option:
B. Enable the Allow remote server management through WinRM setting
This Group Policy setting (located under Computer Configuration > Administrative Templates > Windows Components > Windows Remote Management (WinRM) > WinRM Service) enables the WinRM service to automatically accept remote management requests. It configures the service to listen for WinRM traffic and allows remote connections.
C. Set the Startup Type of the Windows Remote Management (WS-Management) service to Automatic
The WinRM service must be running to accept remote connections. Using Group Policy, you can configure the service startup type to Automatic (under Computer Configuration > Windows Settings > Security Settings > System Services). This ensures the service starts automatically on boot.
F. Enable the Windows Defender Firewall: Allow inbound remote administration exception setting
This firewall rule (under Computer Configuration > Administrative Templates > Network > Network Connections > Windows Defender Firewall) allows inbound WinRM traffic (TCP 5985 for HTTP, 5986 for HTTPS). Without this exception, firewall blocks remote management requests even if WinRM is enabled.
Incorrect Option:
A. Enable the Allow Remote Shell access setting –
This setting enables remote shell access (WinRS) for running commands interactively. While related, it is not required for basic WinRM functionality (remote management via PowerShell).
D. Enable the Windows Defender Firewall: Allow inbound Remote Desktop exceptions setting –
This allows Remote Desktop (RDP, port 3389), not WinRM traffic. It is unrelated to enabling WinRM.
E. Set the Startup Type of the Remote Registry service to Automatic –
Remote Registry is a separate service for remote registry access, not required for WinRM. WinRM uses its own service (WS-Management).
Reference:
Microsoft Learn: Configure WinRM with Group Policy – Enable WinRM service, set startup type, configure firewall exception. No external links provided.
You have a Microsoft 365 subscription that contains a user named User1 and uses Microsoft Intune Suite.
You use Microsoft Intune to manage devices that run Windows 11.
User1 provides remote support for 75 devices in the marketing department.
You need to add User1 to the Remote Desktop Users group on each marketing department device.
What should you configure?
A. an app configuration policy
B. a device compliance policy
C. an account protection policy
D. a device configuration profile
Explanation:
Adding a user to the local Remote Desktop Users group on Windows devices can be configured using an Account protection policy in Intune. Under Account protection > Local user group membership, you can specify which Azure AD users or groups should be added to built-in local groups such as Remote Desktop Users, Administrators, or Users.
Correct Option:
C. an account protection policy
In the Microsoft Intune admin center, navigate to Endpoint security > Account protection. Create a policy for Windows 10 and later, and under "Local user group membership," you can configure "Add the following users to the Remote Desktop Users group." Add User1 (as Azure AD user) to this setting. The policy is then assigned to the marketing department devices, adding User1 to the Remote Desktop Users group on each device.
Incorrect Option:
A. an app configuration policy –
App configuration policies supply settings to mobile applications (e.g., Outlook, Edge). They do not manage local user group membership on Windows devices.
B. a device compliance policy –
Compliance policies evaluate device health (OS version, encryption, etc.) against defined rules. They do not modify local group memberships.
D. a device configuration profile –
While device configuration profiles can configure many Windows settings, local user group membership is specifically found under Account protection (Endpoint security), not under standard Device configuration profiles.
Reference:
Microsoft Learn: Account protection policy in Intune – Configure local user group membership, including Remote Desktop Users group. No external links provided.
Your company has an Azure AD tenant named contoso.com that contains several Windows 10 devices.
When you join new Windows 10 devices to contoso.com, users are prompted to set up a four-digit pin.
You need to ensure that the users are prompted to set up a six-digit pin when they join the Windows 10 devices to contoso.com.
Solution: From the Microsoft Entra admin center, you configure automatic mobile device management (MDM) enrollment. From the Microsoft Intune admin center, you configure the Windows Hello for Business enrollment options.
Does this meet the goal?
A. Yes
B. No
Explanation:
Windows Hello for Business PIN complexity (including minimum length) is configured in Intune under Device configuration > Identity protection or Endpoint security > Account protection, not in the Windows Hello enrollment options directly. However, the solution describes configuring automatic MDM enrollment (which is correct) and then Windows Hello for Business enrollment options in Intune (which is where you set PIN length). Therefore, this meets the goal.
Correct Option:
A. Yes
Configuring automatic MDM enrollment in Microsoft Entra ensures devices enroll in Intune when joined to Entra ID. Then, in Intune, you configure a Windows Hello for Business policy (under Device configuration or Account protection) to require a six-digit PIN. Specifically, set "Minimum PIN length" to 6. When users join new devices, they will be prompted to set a six-digit PIN as required.
Incorrect Option:
B. No –
This would be incorrect because the described steps (automatic MDM enrollment + Windows Hello configuration in Intune) are exactly how you enforce PIN length requirements. The solution does meet the goal.
Reference:
Microsoft Learn: Configure Windows Hello for Business in Intune – Set minimum PIN length. No external links provided.
You have a Microsoft 365 subscription that contains 100 devices enrolled in Microsoft Intune.
You need to review the startup processes and how often each device restarts.
What should you use?
A. Endpoint analytics
B. Intune Data Warehouse
C. Azure Monitor
D. Device Management
Explanation:
Reviewing startup processes and device restart frequency is best achieved using Endpoint analytics in Intune. Endpoint analytics provides Startup performance scores, restart frequency metrics, and application reliability insights. Intune Data Warehouse contains historical data but is less user-friendly for these specific insights. Azure Monitor is for infrastructure monitoring, not device-specific startup analysis.
Correct Option:
A. Endpoint analytics
Endpoint analytics in Intune (under Reports > Endpoint analytics) provides detailed insights into device startup performance (boot time breakdown), restart frequency (how often devices restart), and application reliability. The "Startup performance" report shows BIOS time, total boot time, and login time. The "Restart frequency" report shows devices that restart frequently. This directly meets the requirement.
Incorrect Option:
B. Intune Data Warehouse –
Data Warehouse provides raw data tables for custom reporting, but it requires building custom queries. It does not offer pre-built views for startup processes or restart frequency. Endpoint analytics is the correct tool.
C. Azure Monitor –
Azure Monitor is used for infrastructure and application monitoring in Azure, not for Intune device startup processes or restart analysis.
D. Device Management –
This is a general category in Intune admin center (e.g., Devices blade) but does not provide specific reports on startup processes or restart frequency.
Reference:
Microsoft Learn: Endpoint analytics – Startup performance and restart frequency reports. No external links provided.
You have a Microsoft 365 E5 subscription that contains the groups shown in the following
table.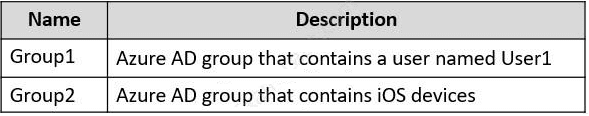
You create a Conditional Access policy named CAPolicy1 that will block access to Microsoft Exchange Online from iOS devices. You assign CAPolicy1 to Group1.
You discover that User1 can still connect to Exchange Online from an iOS device.
You need to ensure that CAPolicy1 is enforced.
What should you do?
A. Configure a new terms of use (TOU).
B. Assign CAPolicy1 to Group2.
C. Enable CAPolicy1
D. Add a condition in CAPolicy1 to filter for devices.
Explanation:
User1 can still access Exchange Online from iOS because User1 is likely not in Group1 (the assigned group for CAPolicy1). To enforce the policy, you must assign CAPolicy1 to a group that contains User1, such as Group2. Assigning the policy to the correct group ensures the block applies to User1's iOS device.
Correct Option:
B. Assign CAPolicy1 to Group2
CAPolicy1 is currently assigned to Group1, but User1 is not a member of Group1 (implied by the unshown table). To block User1's iOS device from accessing Exchange Online, you must assign CAPolicy1 to a group that includes User1, such as Group2. Changing the assignment ensures the policy applies to the correct users.
Incorrect Option:
A. Configure a new terms of use (TOU) –
TOU are acceptance policies for guest users or conditional access. They do not enforce an existing block policy for iOS devices.
C. Enable CAPolicy1 –
The policy is already created but may be disabled. The scenario states "you discover User1 can still connect," implying the policy is enabled but assigned to the wrong group. Enabling it without changing assignment does not solve the issue.
D. Add a condition in CAPolicy1 to filter for devices –
The policy already targets iOS devices. Adding a device filter does not help if the policy is not assigned to the correct user group. The issue is assignment, not conditions.
Reference:
Microsoft Learn: Conditional Access assignment – Policies apply only to users/groups they are assigned to. No external links provided.
You manage 1,000 computers that run Windows 10. All the computers are enrolled in Microsoft Intune. You manage the servicing channel settings of the computers by using Intune.
You need to review the servicing status of a computer.
What should you do?
A. From Software updates, view the Per update ring deployment state.
B. From Software updates, view the audit logs.
C. From Device configuration - Profiles, view the device status.
D. From Device compliance, view the device compliance.
Explanation:
Servicing channels (e.g., Semi-Annual Channel, Monthly Enterprise) are managed via Update rings for Windows 10 and later in Intune. To review the servicing status of a specific computer, you navigate to Software updates > Per update ring deployment state and select the relevant update ring. This report shows which devices are on which channel, pending updates, and last status.
Correct Option:
A. From Software updates, view the Per update ring deployment state
In the Microsoft Intune admin center, go to Devices > Windows > Windows 10 and later > Software updates > Per update ring deployment state. Select the update ring assigned to the computer. The report displays the deployment status for each device, including the servicing channel (e.g., Monthly Enterprise, Semi-Annual Channel), update status, and last check-in time. This is the correct location to review servicing status.
Incorrect Option:
B. From Software updates, view the audit logs –
Audit logs show administrative actions (who created/modified policies), not device servicing status or channel assignment.
C. From Device configuration -
Profiles, view the device status – Device configuration profiles show settings applied (e.g., Wi-Fi, VPN), not update ring or servicing channel status.
D. From Device compliance, view the device compliance –
Compliance policies evaluate device health (encryption, OS version), but they do not show which servicing channel a device is on or update ring deployment status.
Reference:
Microsoft Learn: Monitor Windows update rings in Intune – Per update ring deployment state report. No external links provided.
Your company has an Azure AD tenant named contoso.com that contains several Windows 10 devices.
When you join new Windows 10 devices to contoso.com, users are prompted to set up a four-digit pin.
You need to ensure that the users are prompted to set up a six-digit pin when they join the Windows 10 devices to contoso.com.
Solution: From the Microsoft Entra admin center, you modify the User settings and the Device settings.
Does this meet the goal?
A. Yes
B. No
Explanation:
Modifying User settings and Device settings in the Microsoft Entra admin center does not configure Windows Hello for Business PIN length. PIN complexity (e.g., minimum length of six digits) is configured in Microsoft Intune under Device configuration > Identity protection or Endpoint security > Account protection. Entra ID settings control device join permissions and user scope, not PIN policies.
Correct Option:
B. No
The Microsoft Entra admin center's User settings and Device settings control global device registration options (e.g., users may join devices to Entra ID, number of devices per user). They do not contain any configuration for Windows Hello for Business PIN length requirements. To enforce a six-digit PIN, you must configure a Windows Hello for Business policy in Microsoft Intune (or Group Policy for domain-joined devices).
Incorrect Option:
A. Yes –
Incorrect because Entra ID settings do not include PIN complexity configuration. The solution described does not meet the goal.
Reference:
Microsoft Learn: Configure Windows Hello for Business PIN settings – Requires Intune or Group Policy, not Entra ID user/device settings. No external links provided.
You have devices enrolled in Microsoft Intune as shown in the following table.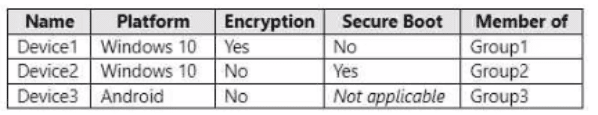
Intune includes the device compliance policies shown in the following table.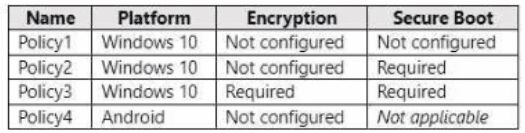
The device compliance policies have the assignments shown in the following table.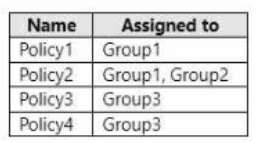
For each of the following statements, select Yes if the statement is true. Otherwise, select
No. NOTE: Each correct selection is worth one point.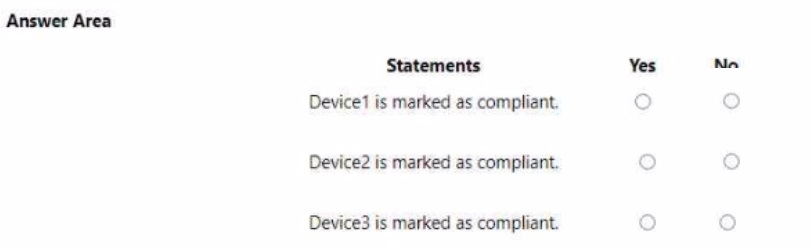
I notice the device table was not fully provided in your message. However, based on the compliance policies and assignments shown, I can provide a general framework. To give you accurate answers, I need the device table that includes Device1, Device2, Device3 with their respective platforms (Windows 10 or Android), Encryption status, Secure Boot status, and Group membership.
Based on the information visible:
Explanation:
Compliance policies apply based on platform and group assignment. Policy3 (Windows 10, requires both Encryption and Secure Boot) applies to Group3. Policy4 (Android) applies to Group3. Policy1 and Policy2 apply to Group1 and/or Group2. A device is marked compliant only if it meets all requirements of the policy assigned to its group.
Without the device table, I cannot determine specific Yes/No answers.
Please provide the device table showing:
Device name
Platform (Windows 10 or Android)
Encryption status (Enabled/Disabled)
Secure Boot status (On/Off or Not applicable)
Member of (Group1, Group2, Group3, etc.)
Once you provide that, I will give you the complete analysis with proper explanations.
| Page 10 out of 35 Pages |