Topic 3: Misc. Questions
You have an Azure subscription that has Microsoft Defender for Cloud enabled.
You have 50 Azure virtual machines that run Windows Server.
You need to ensure that any security exploits detected on the virtual machines are
forwarded to Defender for Cloud.
Which extension should you enable on the virtual machines?
A. Vulnerability assessment for machines
B. Microsoft Dependency agent
C. Log Analytics agent for Azure VMs
D. Guest Configuration agent
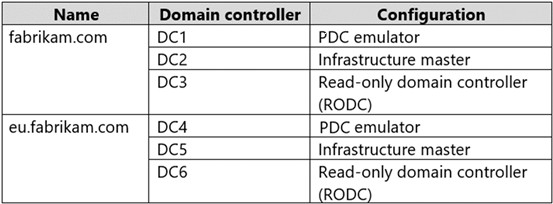
Your network contains an Active Directory Domain Services (AD DS) forest. The forest
contains the domains shown in the following table.
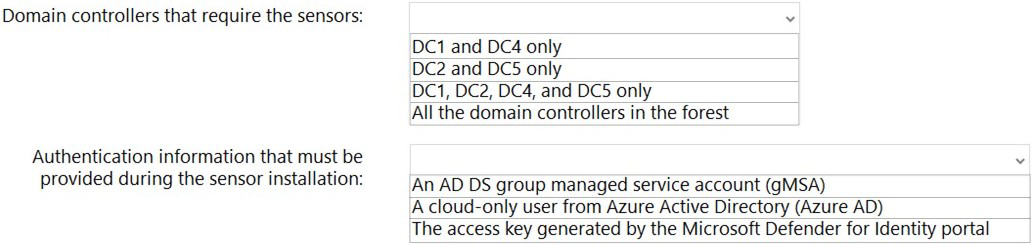
You are implementing Microsoft Defender for Identity sensors.
You need to install the sensors on the minimum number of domain controllers. The solution
must ensure that Defender for Identity will detect all the security risks in both the domains.
What should you identify? To answer, select the appropriate options in the answer area.
NOTE: Each correct selection is worth one point.
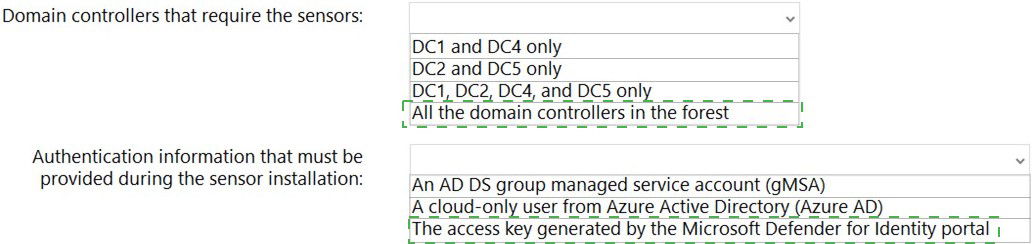
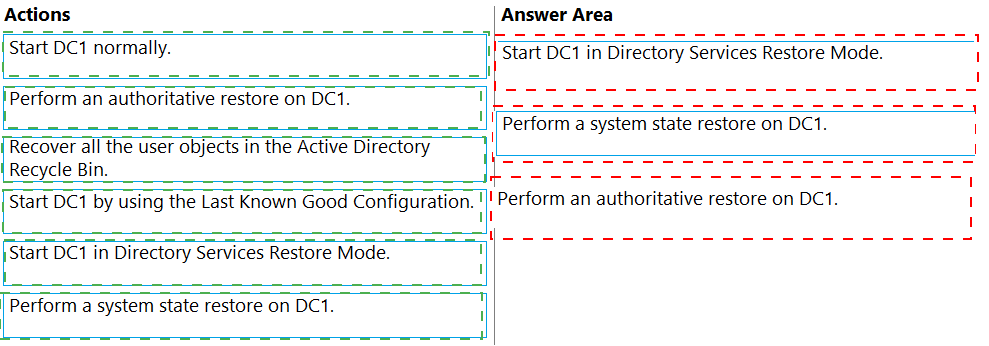
Your network contains an Active Directory Domain Services (AD DS) domain that has the
Active Directory Recycle Bin enabled. The domain contains two domain controllers named
DC1 and DC2. The system state of the domain controllers is backed up daily at 23:00 by
using Windows Server Backup.
You have an organizational unit (OU) named ParisUsers that contains 1,000 users.
At 08:00, DC1 shuts down for hardware maintenance. The maintenance completes, but
DC1 remains shut down.
At 09:00, an administrative error causes the manager attribute of each user in ParisUsers
to be deleted.
You need to recover the user account details as quickly as possible. The solution must
minimize data loss.
Which three actions should you perform in sequence? To answer, move the appropriate
actions from the list of actions to the answer area and arrange them in the correct order.
Your on-premises network contains two subnets. The subnets contain servers that run
Windows Server as shown in the following table.
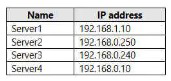
Server4 has the following IP configurations:
Ethernet adapter Ethernet:
Connection-specific DNS Suffix.:
IPv4 Address . . . . . . . . . . . : 192.168.0.10
Subnet Mask . . . . . . . . . . . : 255.255.255.0
Default Gateway . . . . . . . . . : 192.168.0.1
From Server4, you can ping Server1 and Server2 successfully. When you ping Server3,
you get a Request timed out response.
From Server2, you can ping Server1 and Server3 successfully.
The misconfiguration of which component on Server3 can cause the Request timed out
response?
A. default gateway
B. IP address
C. subnet mask
D. DNS server
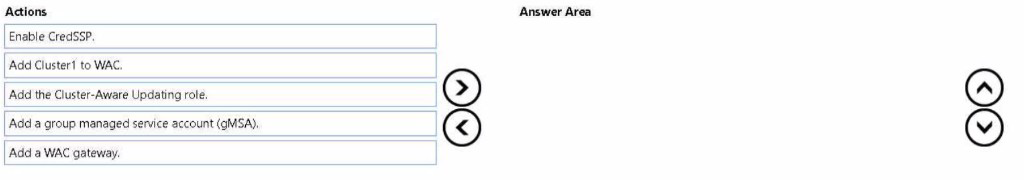
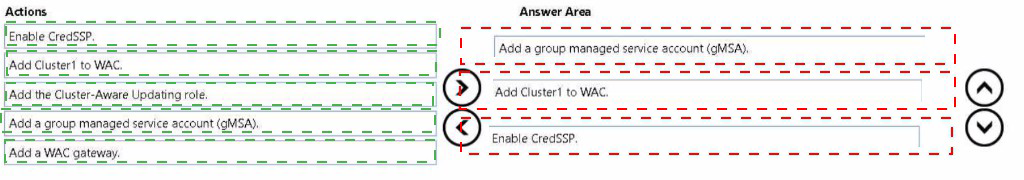
Your network contains an Active Directory Domain Services (AD DS) domain. The domain
contains a failover cluster named Cluster1.
You need to configure Cluster-Aware Updating (CAU) on the cluster by using Windows
Admin Center (WAC).
Which three actions should you perform in sequence? To answer, move the appropriate
actions from the list of actions to the answer area and arrange them in the correct order.
Your on-premises network is connected to Azure.
You have an Azure subscription. The subscription contains a virtual machine named VM1
that runs Windows Server.
You need to identify the latency between the on-premises network and VM1.
Which Azure Network Watcher settings should you use?
A. IP flow verify
B. Connection monitor
C. VPN troubleshoot
D. Connection troubleshoot
Note: This question is part of a series of questions that present the same scenario. Each
question in the series contains a unique solution that might meet the stated goals. Some
question sets might have more than one correct solution, while others might not have a
correct solution.
After you answer a question in this section, you will NOT be able to return to it. As a result,
these questions will not appear in the review screen.
You have a server named Server1 that runs Windows Server.
You need to ensure that only specific applications can modify the data in protected folders
on Server1.
Solution: From Virus & threat protection, you configure Tamper Protection.
Does this meet the goal?
A. Yes
B. No
Note: This question is part of a series of questions that present the same scenario. Each
question in the series contains a unique solution that might meet the stated goals. Some
question sets might have more than one correct solution, while others might not have a
correct solution.
After you answer a question in this section, you will NOT be able to return to it. As a result,
these questions will not appear in the review screen.
You have an on-premises server named Server1 that runs Windows Server.
You have a Microsoft Sentinel instance.
You add the Windows Firewall data connector in Microsoft Sentinel.
You need to ensure that Microsoft Sentinel can collect Windows Firewall logs from Server1.
Solution: You install the Log Analytics agent on Server1
Does this meet the goal?
A. Yes
B. No
Your network contains an Active Directory Domain Services (AD DS) domain named
contoso.com. The domain contains an organizational unit (OU) named 0U1.0U1 contains
servers that run sensitive workloads.
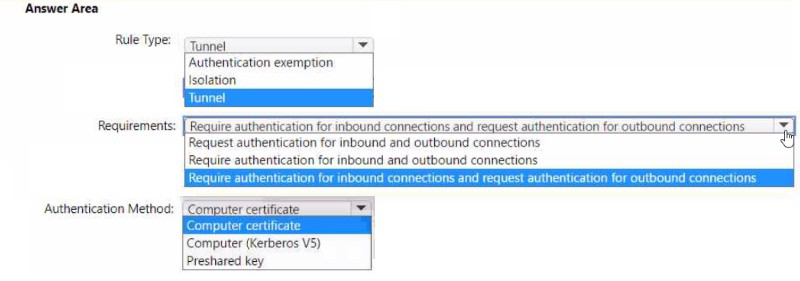
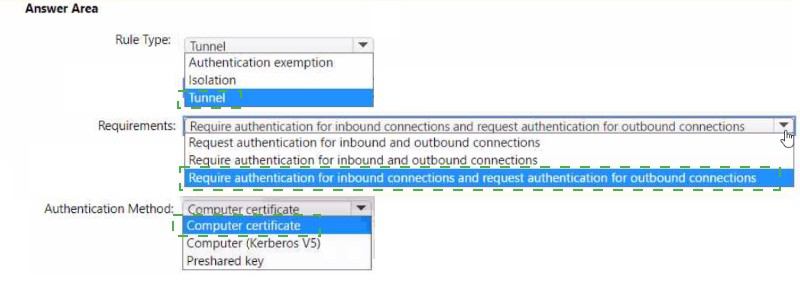
You plan to add connection security rules that meet the following requirements:
• The servers in OU 1 must only accept connections from domain-joined
• The servers in OU 1 must only be able to communicate with domain-joined
You create a Group Policy Object (GPO) named GP01 and link GP01 to contoso.com.
You need to configure a connection security rule in GP01 by using Windows Defender
Firewall with Advanced Security.
How should you configure the rule? To answer, select the appropriate options in the
answer area.
NOTE: Each correct selection is worth one point.
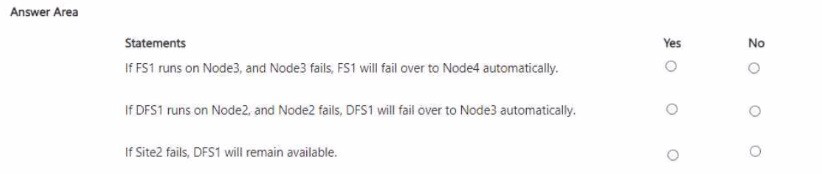
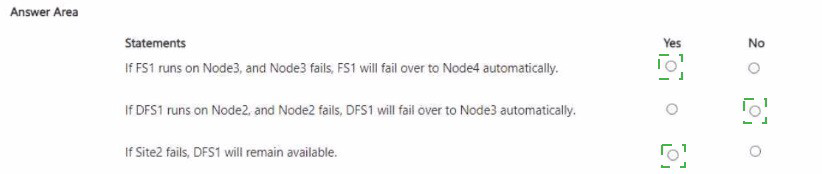
You have a Windows Server failover cluster named Cluster1 that has a cloud witness and
the nodes shown in the following table.
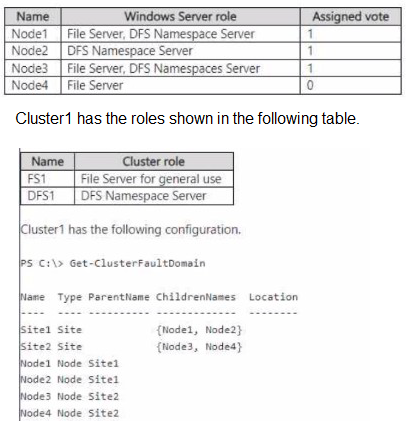
For each of the following statements, select Yes if the statement is true. Otherwise, select
No.
NOTE: Each correct selection is worth one point.
| Page 4 out of 16 Pages |