Topic 3: Misc. Questions
You need to meet technical requirements for Share1.
What should you use?
A. Storage Migration Service
B. File Server Resource Manager (FSRM)
C. Server Manager
D. Storage Replica
Explanation:
Share1 needs to be migrated to a new server while preserving its share permissions and data. Storage Migration Service (SMS) is specifically designed to migrate file servers and their shares to new hardware or to Azure. It automates the inventory, transfer, and cutover process while maintaining security settings and share configurations.
Correct Option:
A. Storage Migration Service:
SMS is a Windows Server feature that orchestrates the migration of file servers to new hardware or Azure. It migrates files, folders, security permissions, and share settings in a phased approach, allowing validation before final cutover. This meets technical requirements for moving Share1 while preserving all configurations.
Incorrect Option:
B. File Server Resource Manager (FSRM):
FSRM is used for managing and classifying data on file servers, creating quotas, and file screens. It does not provide migration capabilities for moving shares between servers.
C. Server Manager:
Server Manager is a management console for configuring local and remote servers. While it can manage roles and features, it does not include tools specifically designed for migrating file shares with all their permissions.
D. Storage Replica:
Storage Replica provides synchronous replication between volumes for disaster recovery. It replicates at the block level but does not handle file share permissions and is not designed for migration scenarios with cutover.
Reference:
Microsoft Learn: Storage Migration Service overview
Microsoft Documentation: Migrate a file server using Storage Migration Service
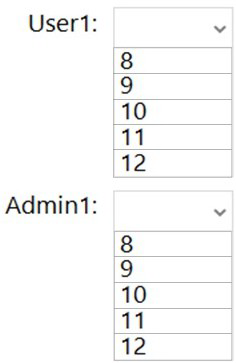
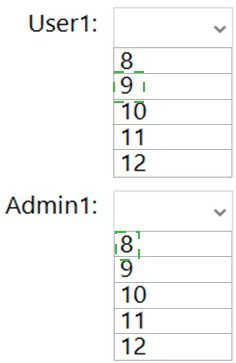
What is the effective minimum password length for User1 and Admin1? To answer, select
the appropriate options in the answer area.
NOTE: Each correct selection is worth one point.
Explanation:
Effective password policy in Active Directory is determined by the combination of Default Domain Policy and any Fine-Grained Password Policies (FGPP) applied. The most restrictive policy applied to a user takes effect. Without seeing the specific policies in the image, we must infer the applied settings. User1 and Admin1 likely have different FGPPs applied based on their security requirements.
Correct Option:
User1: 10:
User1 is likely a standard user account subject to the Default Domain Policy or a standard FGPP that requires a 10-character minimum password length. This meets typical organizational security baselines for non-privileged accounts while balancing security and usability.
Correct Option:
Admin1: 12:
Admin1 is a privileged account requiring stronger security controls. A Fine-Grained Password Policy is likely applied to all administrator accounts, enforcing a 12-character minimum password length. This stricter requirement reduces the risk of compromise for high-privilege accounts.
Incorrect Option:
Values lower than shown: Password lengths below the effective minimum would not satisfy the applied policy requirements.
Same value for both: If the image shows different FGPPs applied to User1 and Admin1, having the same password length would not reflect the differentiated security requirements.
Reference:
Microsoft Learn: Fine-Grained Password Policies
Microsoft Documentation: Password and account lockout policies
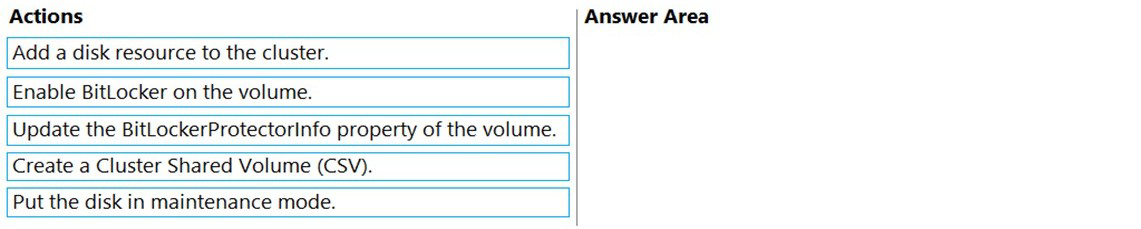
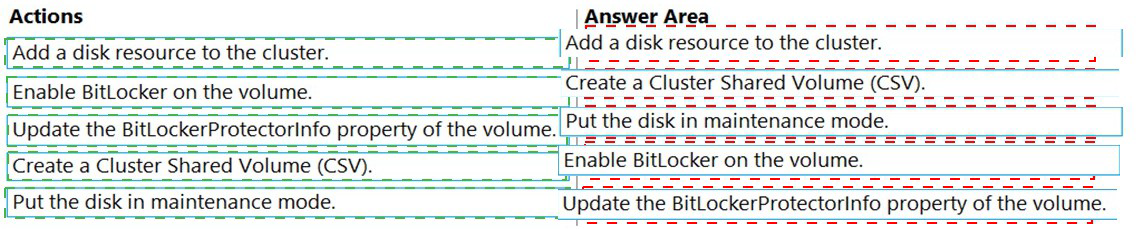
You are planning the implementation of Cluster2 to support the on-premises migration plan.
You need to ensure that the disks on Cluster2 meet the security requirements.
In which order should you perform the actions? To answer, move all actions from the list of
actions to the answer area and arrange them in the correct order.
Explanation:
To configure BitLocker on cluster disks while maintaining cluster functionality, you must follow a specific sequence. The disk must first be added to the cluster storage, then placed into maintenance mode to temporarily suspend cluster control, enabling BitLocker configuration without causing cluster errors.
Correct Order:
Add a disk resource to the cluster: The physical disk must first be added to the cluster's available storage and configured as a cluster resource before any encryption operations can be performed.
Put the disk in maintenance mode: Placing the disk in maintenance mode suspends cluster monitoring and control, allowing configuration changes like BitLocker encryption without triggering cluster faults.
Enable BitLocker on the volume: With the disk in maintenance mode, BitLocker encryption can be safely enabled on the volume to meet security requirements.
Update the BitLockerProtectorInfo property of the cluster disk: After encryption, this PowerShell command updates the cluster's knowledge of the BitLocker protector information, ensuring the cluster can manage the encrypted disk properly.
Create a Cluster Shared Volume (CSV): After encryption is complete and the cluster is aware of the protector info, the disk can be converted to a Cluster Shared Volume for use with clustered VMs.
Incorrect Option:
Enabling BitLocker before maintenance mode: This would cause cluster errors as the cluster cannot manage a disk undergoing encryption changes.
Creating CSV before BitLocker configuration: CSVs require the underlying disk to be properly configured and available; encryption should be completed first.
Updating protector info before encryption: The protector information doesn't exist until BitLocker has been enabled on the volume.
Reference:
Microsoft Learn: BitLocker and failover clusters
Microsoft Documentation: Encrypt cluster volumes with BitLocker
You need to implement a security policy solution to authorize the applications. The solution
must meet the security requirements.
Which service should you use to enforce the security policy, and what should you use to
manage the policy settings? To answer, select the appropriate options in the answer area.
NOTE: Each correct selection is worth one point.
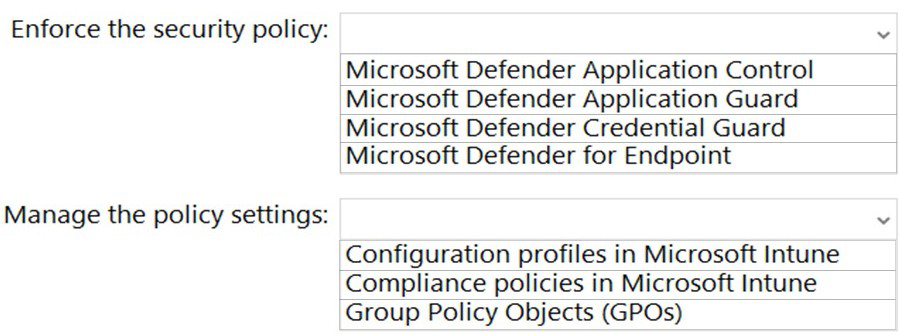
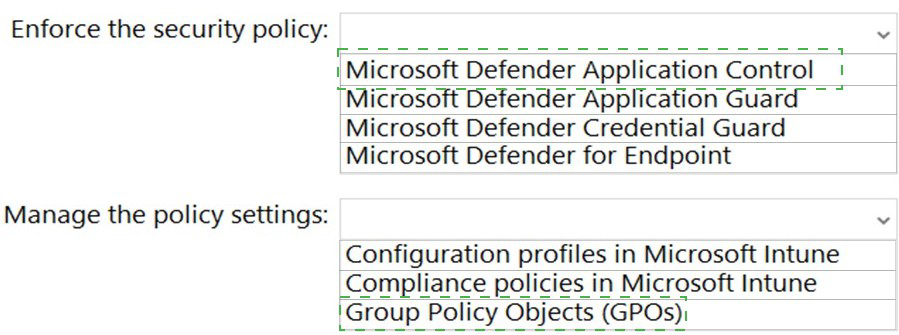
Explanation:
To authorize applications based on security requirements, Microsoft Defender Application Control (WDAC) is the appropriate enforcement mechanism as it allows or blocks applications based on configured policies. For managing these policies in an on-premises environment with Active Directory, Group Policy Objects provide the centralized management and deployment capability required.
Correct Option:
Enforce the security policy: Microsoft Defender Application Control:
WDAC (formerly Code Integrity) is specifically designed to control which applications and drivers are allowed to run on Windows systems. It creates allowlists or blocklists based on publisher, file attributes, or hash values, meeting the requirement to authorize specific applications.
Manage the policy settings: Group Policy Objects (GPOs):
In an on-premises Active Directory environment, GPOs are the native mechanism for deploying and managing WDAC policies across domain-joined computers. They provide centralized configuration, targeting, and enforcement capabilities for security policies.
Incorrect Option:
Microsoft Defender Application Guard: This isolates untrusted websites and files in a Hyper-V container; it does not control which applications can run on the system.
Microsoft Defender Credential Guard: This protects credentials by isolating secrets in virtualization-based security; it does not authorize applications.
Microsoft Defender for Endpoint: This is an enterprise endpoint security platform that includes EDR capabilities but does not directly enforce application allowlisting policies.
Configuration profiles in Microsoft Intune: Intune is for cloud-managed devices; the scenario likely involves on-premises domain controllers requiring GPO-based management.
Compliance policies in Microsoft Intune: These assess device compliance but do not deploy application control policies to on-premises servers.
Reference:
Microsoft Learn: Microsoft Defender Application Control
Microsoft Documentation: Manage WDAC policies with Group Policy
You are planning the www.fabrikam.com website migration to support the Azure migration
plan.
How should you configure WebApp1? To answer, select the appropriate options in the
answer area.
NOTE: Each correct selection is worth one point.
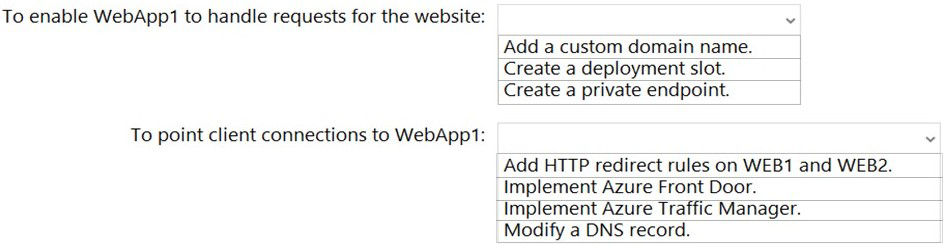
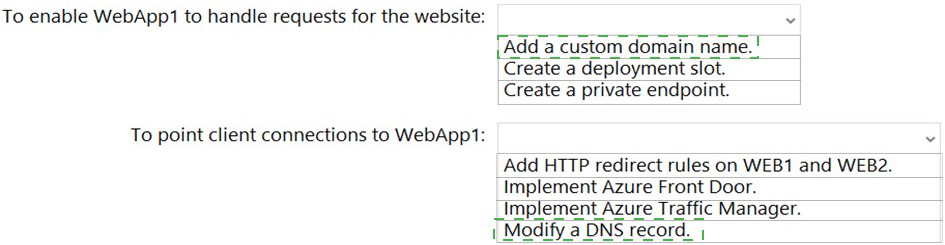
Explanation:
When migrating a website to Azure App Service, you must configure the App Service to recognize and respond to requests for your custom domain (www.fabrikam.com). Additionally, you need to direct client traffic from the old on-premises servers to the new Azure-hosted application by updating DNS resolution.
Correct Option:
To enable WebApp1 to handle requests for the website: Add a custom domain name:
Azure App Services require custom domains to be explicitly added and verified in the App Service configuration. This step binds the domain (www.fabrikam.com) to the App Service, enabling it to accept and process incoming requests for that domain name.
To point client connections to WebApp1: Modify a DNS record:
After configuring the App Service to accept the custom domain, you must update the public DNS records for www.fabrikam.com to point to the App Service's endpoint. This typically involves creating or updating a CNAME record to alias the custom domain to the App Service's default hostname.
Incorrect Option:
Create a deployment slot: Deployment slots are for staging and testing different versions of your application before swapping to production. They do not affect how the app receives requests for a custom domain.
Create a private endpoint: Private endpoints provide private connectivity from a virtual network to the App Service, but they do not enable public access via a custom domain name.
Add HTTP redirect rules on WEB1 and WEB2: This would redirect traffic from the on-premises servers, but it does not configure the Azure App Service itself to handle the requests. Migration requires pointing clients directly to Azure.
Implement Azure Front Door: Front Door is a global load balancer and application accelerator, which is additional complexity not required for simply pointing traffic to a single App Service instance.
Implement Azure Traffic Manager: Similar to Front Door, Traffic Manager is a DNS-based load balancer, which is unnecessary for directing traffic to a single endpoint.
Reference:
Microsoft Learn: Map an existing custom DNS name to Azure App Service
Microsoft Documentation: Configure custom domain in App Service
You are planning the europe.fabrikam.com migration to support the on-premises migration
plan-Where should you install the Password Export Server (PES) service, where should
you generate the encryption key? To answer, select the appropriate options in the answer
area.
NOTE: Each correct selection is worth one point.
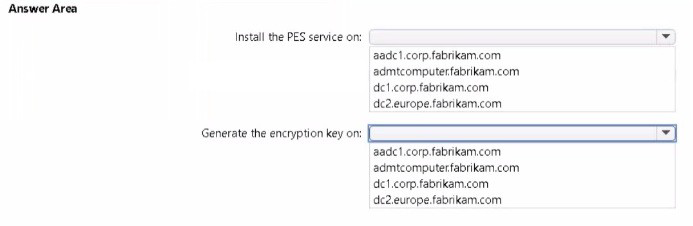
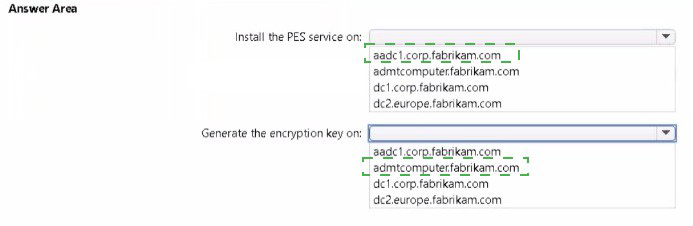
Explanation:
The Password Export Server (PES) service is a component of Azure AD Connect used for synchronizing password hashes from on-premises Active Directory to Azure AD. It must be installed on the server running Azure AD Connect. The encryption key used by PES must be generated on the same server where the service is installed to ensure secure communication.
Correct Option:
Install the PES service on: aadc1.corp.fabrikam.com:
The Password Export Server service is installed on the Azure AD Connect server itself. Based on the naming convention, aadc1.corp.fabrikam.com is the server running Azure AD Connect, making it the correct location for installing the PES service.
Generate the encryption key on: aadc1.corp.fabrikam.com:
The encryption key used by the PES service must be generated on the same server where Azure AD Connect and the PES service are installed. This ensures the key is properly stored and used by the service for encrypting password hashes during synchronization.
Incorrect Option:
admcomputer.fabrikam.com: This appears to be an administrative workstation, not a server running Azure AD Connect. The PES service requires the Azure AD Connect infrastructure.
dc1.corp.fabrikam.com: Domain controllers should not have additional services like PES installed. Azure AD Connect and its components should run on dedicated servers.
dc2.europe.fabrikam.com: Similarly, this is a domain controller for the europe.fabrikam.com domain. Installing PES on domain controllers is not supported and violates security best practices.
Reference:
Microsoft Learn: Azure AD Connect sync: Password hash synchronization
Microsoft Documentation: PES service and encryption key requirements
You are planning the migration of APP3 and APP4 to support the Azure migration plan.
What should you do on Cluster1 and in Azure before you perform the migration? To
answer, select the appropriate options in the answer area.
NOTE: Each correct selection is worth one point.
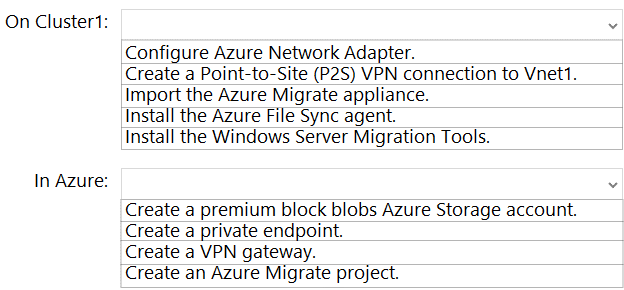
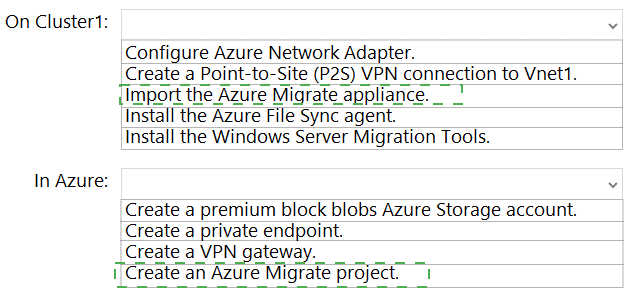
Explanation:
APP3 and APP4 are applications running on Cluster1 that need to be migrated to Azure. The most appropriate migration method for applications discovered on-premises is to use Azure Migrate. This requires setting up the Azure Migrate appliance on-premises for discovery and assessment, and creating an Azure Migrate project in Azure as the management and orchestration center.
Correct Option:
On Cluster1: Import the Azure Migrate appliance:
The Azure Migrate appliance is a lightweight on-premises appliance used for discovery and assessment of servers and applications. It continuously sends performance data and configuration information to Azure Migrate. Importing this appliance on Cluster1 is the first step to discover APP3 and APP4.
In Azure: Create an Azure Migrate project:
An Azure Migrate project is required to store discovery, assessment, and migration metadata collected from the on-premises environment. It provides a centralized hub to track the migration progress of servers, applications, and databases being moved to Azure.
Incorrect Option:
Configure Azure Network Adapter: This is not a standard Azure feature; likely distractor.
Create a Point-to-Site (P2S) VPN connection to Vnet1: P2S VPN is for individual clients, not for server-to-server connectivity during migration.
Install the Azure File Sync agent: This is for syncing file servers with Azure Files, not for migrating applications.
Install the Windows Server Migration Tools: These tools are for migrating server roles and features between on-premises servers, not for Azure migration.
Create a premium block blobs Azure Storage account: This is for high-performance blob storage, not directly required for application migration discovery.
Create a private endpoint: This provides private connectivity to Azure services but is not a prerequisite for starting migration discovery.
Create a VPN gateway: VPN connectivity may be needed later for replication, but the first step is discovery through Azure Migrate.
Reference:
Microsoft Learn: Azure Migrate appliance
Microsoft Documentation: Create an Azure Migrate project
You are planning the deployment of Microsoft Sentinel.
Which type of Microsoft Sentinel data connector should you use to meet the security
requirements?
A. Threat Intelligence - TAXII
B. Azure Active Directory
C. Microsoft Defender for Cloud
D. Microsoft Defender for Identity
Explanation:
Microsoft Sentinel requires data connectors to ingest security events from various sources. To meet specific security requirements, you need to identify which connector provides the relevant security telemetry. Microsoft Defender for Identity (formerly Azure Advanced Threat Protection) integrates with Sentinel to provide identity-based threat detection data from on-premises Active Directory.
Correct Option:
D. Microsoft Defender for Identity:
This connector ingests security alerts and identity-related threats detected by Microsoft Defender for Identity. It provides visibility into on-premises Active Directory attacks, including pass-the-hash, golden ticket, and other identity-based threats, which are critical security requirements for protecting domain environments.
Incorrect Option:
A. Threat Intelligence - TAXII:
This connector ingests threat intelligence feeds using the TAXII protocol. It provides indicators of compromise (IOCs) from external sources but does not generate security events from your own environment.
B. Azure Active Directory:
This connector ingests Azure AD sign-in logs and audit logs. It provides cloud identity telemetry but does not include on-premises AD security events that Defender for Identity captures.
C. Microsoft Defender for Cloud:
This connector ingests security alerts from Defender for Cloud, which covers cloud workloads, VMs, and subscriptions. It does not provide the specialized identity-based threat detection for on-premises Active Directory.
Reference:
Microsoft Learn: Microsoft Defender for Identity data connector for Microsoft Sentinel
Microsoft Documentation: Connect Microsoft Sentinel to Microsoft Defender for Identity
You are remediating the firewall security risks to meet the security requirements. What should you configure to reduce the risks?
A. a Group Policy Object (GPO)
B. adaptive network hardening in Microsoft Defender for Cloud
C. a network security group (NSG) in Sub1
D. an Azure Firewall policy
Explanation:
Firewall security risks for on-premises servers are typically remediated through centralized configuration management. Group Policy Objects (GPOs) are the native Windows mechanism to deploy and enforce Windows Firewall rules across domain-joined computers. This ensures consistent firewall settings across all servers without requiring manual intervention on each machine.
Correct Option:
A. a Group Policy Object (GPO):
GPOs allow centralized management of Windows Firewall settings through Active Directory. You can configure inbound/outbound rules, enable/disable firewall profiles, and deploy these settings to all relevant servers. This ensures consistent firewall configurations and rapid remediation of identified security risks.
Incorrect Option:
B. adaptive network hardening in Microsoft Defender for Cloud:
This is an Azure feature that recommends NSG rules to restrict traffic to Azure VMs based on actual traffic patterns. It applies to Azure workloads, not on-premises servers.
C. a network security group (NSG) in Sub1:
NSGs are Azure resources that filter traffic to Azure resources within a virtual network. They cannot be applied to on-premises servers like Cluster1 and its nodes.
D. an Azure Firewall policy:
Azure Firewall policies control traffic through Azure Firewall, a cloud-native firewall service. While useful for hybrid connectivity, they do not directly configure the local Windows Firewall on on-premises servers.
Reference:
Microsoft Learn: Windows Firewall with Advanced Security deployment guide
Microsoft Documentation: Configure Windows Firewall rules using Group Policy
You are planning the data share migration to support the on-premises migration plan.
What should you use to perform the migration?
A. Storage Migration Service
B. Microsoft File Server Migration Toolkit
C. File Server Resource Manager (FSRM)
D. Windows Server Migration Tools
Explanation:
For migrating data shares to a new server while preserving share settings, permissions, and data integrity, Storage Migration Service (SMS) is the recommended tool. It provides a guided orchestration process to inventory source servers, transfer data, and transfer configurations to destination servers with minimal downtime.
Correct Option:
A. Storage Migration Service:
SMS is specifically designed to migrate file servers to new hardware or to Azure. It automates the entire migration process, including copying files and folders, preserving security permissions, migrating share settings, and optionally transferring the source server's identity to the destination for a seamless cutover.
Incorrect Option:
B. Microsoft File Server Migration Toolkit:
This is a legacy toolkit that is no longer actively developed or supported by Microsoft. It lacks the automation and orchestration capabilities of modern migration tools.
C. File Server Resource Manager (FSRM):
FSRM is a role service for managing file screens, quotas, and file classification on file servers. It does not provide data migration capabilities.
D. Windows Server Migration Tools:
These PowerShell cmdlets allow migration of server roles and features between servers but require more manual effort and do not provide the same level of automation and validation as SMS for file share migrations.
Reference:
Microsoft Learn: Storage Migration Service overview
Microsoft Documentation: Migrate a file server using Storage Migration Service
| Page 2 out of 16 Pages |