Topic 5: Mix Questions
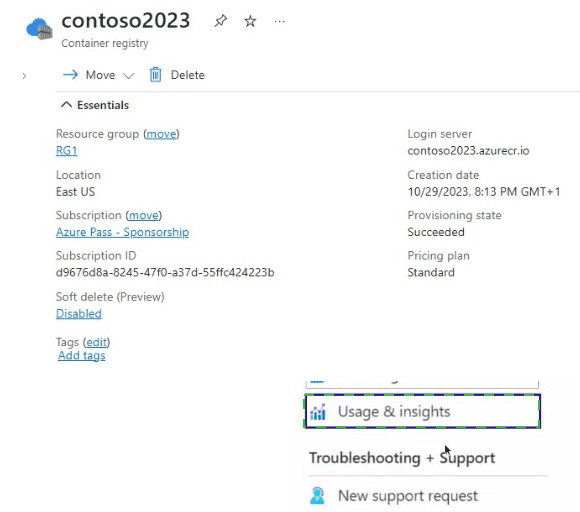
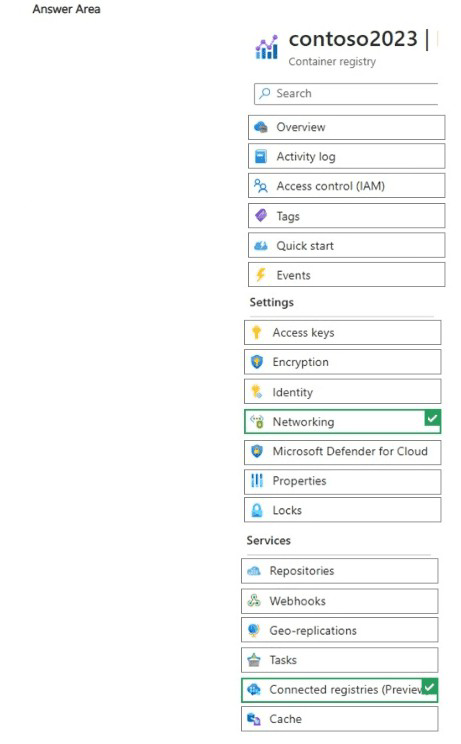
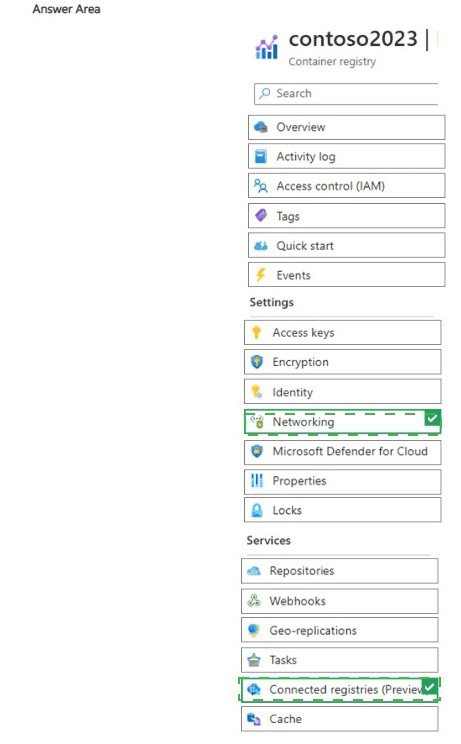
You have an Azure container registry named contoso2023 as shown in the following
exhibit.
Explanation:
The exhibit shows the Azure portal view of a container registry named contoso2023 (Standard tier) with the "Networking" blade selected and "Connected registries (Preview)" highlighted under Services. This preview feature enables creating on-premises or remote replicas that sync images/artifacts from the cloud registry for faster, lower-latency access in distributed or edge scenarios. The question likely tests identifying where to manage this capability, as "Connected registries (Preview)" is explicitly visible and directly related to registry replication/sync features.
Correct Option:
Connected registries (Preview)
This is the correct blade/section because it is the dedicated location in the Azure portal for managing connected registry resources (in Preview at the time). Connected registries allow you to deploy a local/on-premises registry instance that synchronizes content (pull/push) with the cloud-based Azure Container Registry, improving performance for remote locations, reducing WAN traffic, and supporting scenarios like disconnected operations or edge computing. The exhibit highlights this under Services, confirming it's the entry point for configuration.
Incorrect Option:
Networking
While selected in the exhibit, the Networking blade primarily handles public/private endpoint access, firewalls, virtual network integration, and dedicated data endpoints (available in Premium tier). It does not manage connected registries, which are a separate replication/sync feature. Selecting Networking alone won't enable or configure connected registry scenarios.
Incorrect Option:
Usage & insights
This blade (highlighted in the second exhibit) provides monitoring metrics, such as pull/push counts, storage usage, and performance insights for the registry. It is for observability and troubleshooting, not for configuring or enabling connected registries or any synchronization features.
Reference:
Microsoft Learn: What is a connected registry? - https://learn.microsoft.com/en-us/azure/container-registry/intro-connected-registry
Microsoft Learn: Create a connected registry - https://learn.microsoft.com/en-us/azure/container-registry/quickstart-create-connected-registry
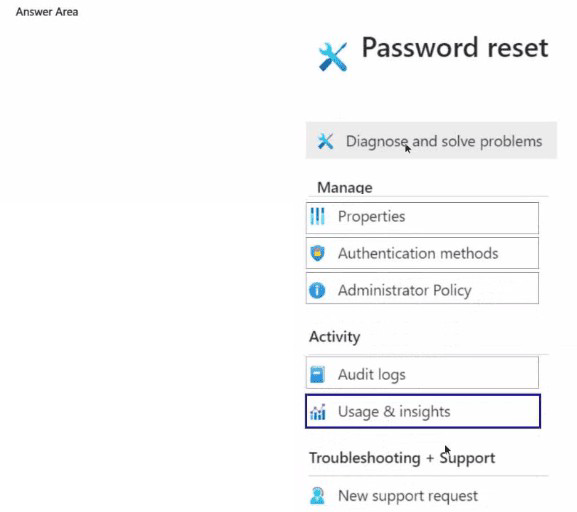
You have an Azure subscription and a Microsoft Entra ID P1 license.
You need to perform the following actions:
* Enable self-service password reset (SSPR) for all users.
* Require the users to answer four questions when registering for SSPR.
Which two settings should you use? To answer, select the appropriate settings in the
answer area.
NOTE: Each correct selection is worth one point.
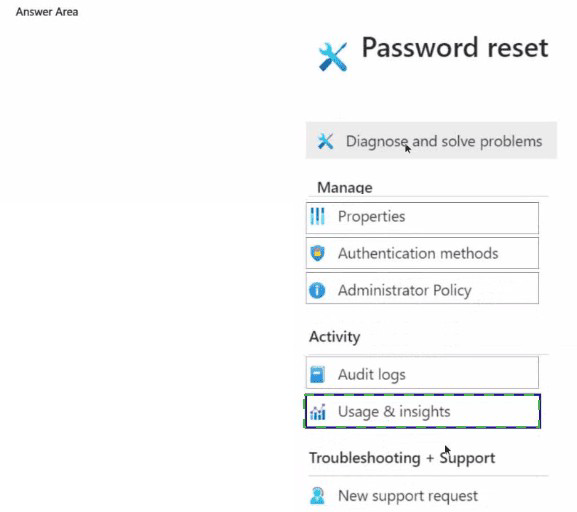
Explanation:
This question tests configuration of Azure AD Self-Service Password Reset (SSPR). SSPR allows users to reset their own passwords without administrator intervention. Enabling it for all users is a global on/off switch, while the number of required security questions for registration is a separate, detailed policy setting.
Correct Options:
Password reset
This is the main configuration blade for SSPR in the Azure AD admin center. Selecting this is the first step, as it's where you navigate to enable SSPR for the desired group of users (in this case, "All") and configure its core behavior. You cannot set any SSPR details without first accessing this area.
Authentication methods
This is a sub-setting within the "Password reset" configuration. Once in the Password reset blade, you select "Authentication methods" to define how users can verify their identity. Here, you configure the number and types of security questions. Specifically, you would set "Number of questions required to register" to 4 and "Number of questions required to reset" (e.g., to 2).
Incorrect Options / Why Other Settings are Not Correct:
Properties:
This blade contains high-level directory properties like the tenant name, technical contact info, and settings for security defaults. It does not contain SSPR configuration.
Administrator Policy:
This is not a standard Azure AD blade. Password policies for administrators are typically enforced via Conditional Access or are the same as for users, configured within the main SSPR settings.
Audit logs:
This is for reviewing historical events and sign-ins, not for configuring services.
New support request: This is for opening a ticket with Microsoft support, not for service configuration.
Reference:
Microsoft Learn documentation, "Tutorial: Enable users to unlock their account or reset passwords using Azure Active Directory self-service password reset". The steps guide you to: 1) Navigate to Azure Active Directory > Password reset. 2) To configure security questions, under the Authentication methods tab, set the number of questions required for registration and reset.
Note: This question is part of a series of questions that present the same scenario. Each
question in the series contains a unique solution that might meet the stated goals. Some
question sets might have more than one correct solution, while others might not have a
correct solution.
After you answer a question in this section, you will NOT be able to return to it. As a result,
these questions will not appear in the review screen.
You have a Microsoft Entra tenant named Adatum.com and an Azure Subscription named
Subscription1. Adatum.com contains a group named Developers. Subscription1 contains a
resource group named Dev.
You need to provide the Developers group with the ability to create Azure logic apps in the
Dev resource group.
Solution: On Dev, you assign the Logic App Contributor role to the Developers group.
Does this meet the goal?
A. Yes
B. No
Explanation:
This question tests the correct application of a built-in Azure role to achieve a specific permission at the resource group scope. The goal is to grant a group the ability to create and manage Azure Logic Apps within a single, specified resource group. The solution must provide the necessary permissions without granting broader, unnecessary access.
Correct Option:
A. Yes.
This solution does meet the goal.
The Logic App Contributor role is the precise built-in role designed for managing Azure Logic Apps. It grants full management capabilities, including the ability to create, modify, manage, and run logic apps.
By assigning this role to the Developers group at the scope of the Dev resource group, you successfully give the group members the required permissions to create Logic Apps within that specific resource group. This follows the principle of least privilege, as the permission is scoped to Dev and not to the entire subscription.
Incorrect Option:
B. No.
Choosing "No" would be incorrect because the solution is valid and fulfills all stated requirements. There is no need for a broader subscription-level assignment, and the chosen role is the correct one for the Logic Apps service.
Reference:
Microsoft Learn documentation, "Azure built-in roles". The description for the Logic App Contributor role states: "Lets you manage logic apps, but not change access to them." This confirms it provides all management permissions for the Logic Apps resource type. Assigning this role at the resource group scope is a standard and correct practice for delegating management of specific services within a contained environment.
You have an Azure virtual network named VNetl that contains the following settings:
• IPv4 address space: 172.16.10.0/24
• Subnet name: Subnetl
• Subnet address range: 172.16.10.0/25
What is the maximum number of virtual machines that can connect to Subnetl?
A. 24
B. 25
C. 123
D. 128
E. 251
Explanation:
The question tests subnetting knowledge in Azure Virtual Networks. VNet1 has an address space of 172.16.10.0/24 (256 total addresses). Subnet1 uses 172.16.10.0/25, which is half of the VNet space. In Azure, each subnet reserves 5 IP addresses for system use (network address, broadcast address, and 3 for Azure services: gateway, DNS, DHCP). The usable IP addresses determine how many virtual machines (or NICs) can be attached to the subnet.
Correct Option:
C. 123
A /25 subnet provides 2^(32-25) = 2^7 = 128 total IP addresses. Azure reserves the first 4 addresses (network + 3 Azure-reserved) and the last address (broadcast), totaling 5 reserved IPs. Therefore, usable addresses = 128 - 5 = 123. This is the maximum number of virtual machines (or network interfaces) that can be connected to Subnet1.
Incorrect Option:
A. 24
This value is incorrect and seems to confuse the /24 VNet space or miscalculate subnetting. A /27 subnet would yield ~27 usable IPs, but Subnet1 is /25, so 24 is far too low.
Incorrect Option:
B. 25
Possibly a misunderstanding of “/25” as directly meaning 25 usable IPs. However, /25 = 128 total IPs, and after Azure’s 5 reserved addresses, the correct usable count is 123, not 25.
Incorrect Option:
D. 128
This represents the total number of IP addresses in a /25 subnet (including network and broadcast). It does not account for the 5 addresses Azure reserves in every subnet, so 128 overestimates the maximum VMs by 5.
Incorrect Option:
E. 251
This is the usable IP count for a /24 subnet (256 total – 5 reserved = 251). Since Subnet1 is carved out as /25 (half the size), this value applies to the parent VNet space, not to Subnet1.
Reference:
Microsoft Learn: Azure virtual network – IP addressing and subnetting
https://learn.microsoft.com/en-us/azure/virtual-network/ip-services/virtual-networks-faq#what-address-ranges-can-i-use-in-my-vnets
Microsoft Learn: Reserved IP addresses in Azure subnets
https://learn.microsoft.com/en-us/azure/virtual-network/virtual-networks-faq#are-there-any-reserved-ip-addresses-in-a-subnet
You have an Azure subscription.
You plan to create a storage account named storage1.
You need to configure a deny assignment for storage1.
What should you use?
A. an Azure Resource Manager (ARM) template
B. Azure Policy
C. a landing zone
D. a deployment stack
Explanation:
This question tests knowledge of different Azure governance tools and their specific purposes. A "deny assignment" is a specific, powerful mechanism that explicitly blocks users from performing certain actions on specific resources, regardless of any other role assignments they might have. It is part of the Azure authorization system.
Correct Option:
B. Azure Policy is the correct answer.
Azure Policy can be used to create and manage deny assignments through policies with a "Deny" effect. When you create a policy definition with a set of rules and the "Deny" effect and assign it to a scope (like the subscription or a resource group containing storage1), Azure Policy automatically creates the underlying deny assignments to enforce the block. This is the primary tool for implementing systematic deny rules at scale.
Incorrect Options:
A. an Azure Resource Manager (ARM) template:
An ARM template (or Bicep) is a declarative tool for deploying and configuring resources. It cannot create a deny assignment. Deny assignments are part of Azure's authorization (RBAC) layer, not the resource provisioning layer.
C. a landing zone:
A landing zone is a cloud environment setup or framework (often following the Cloud Adoption Framework) that includes pre-configured governance, security, and networking. It is a conceptual architecture or an implementation that uses tools like Azure Policy, but it is not a specific tool you use to "configure a deny assignment."
D. a deployment stack:
A deployment stack is an Azure resource type (currently in preview) used to manage a collection of Azure resources as a single unit for lifecycle management (deploy, update, delete). Like ARM templates, it is focused on resource provisioning and management, not on creating authorization deny rules.
Reference:
Microsoft Learn documentation, "Understand how Azure Policy works with RBAC". It explains: "Azure Policy with a Deny effect is an authorization system that prevents actions... When a policy with a Deny effect is assigned, the effect creates deny assignments on the included resource(s)." This directly links the action of configuring a deny assignment to using Azure Policy.
You have an Azure subscription that contains the resources shown in the following table.
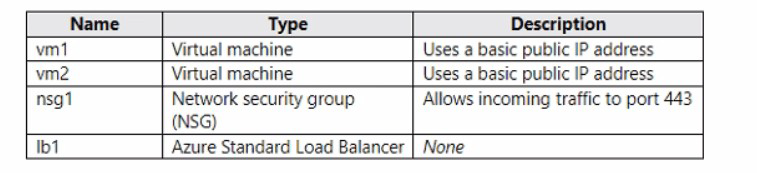 You need to load balance HTTPS connections to vm1 and vm2 by using Ib1.
Which three actions should you perform in sequence? To answer, move the appropriate
actions from the list of actions to the answer area and arrange them in the correct order.
You need to load balance HTTPS connections to vm1 and vm2 by using Ib1.
Which three actions should you perform in sequence? To answer, move the appropriate
actions from the list of actions to the answer area and arrange them in the correct order.
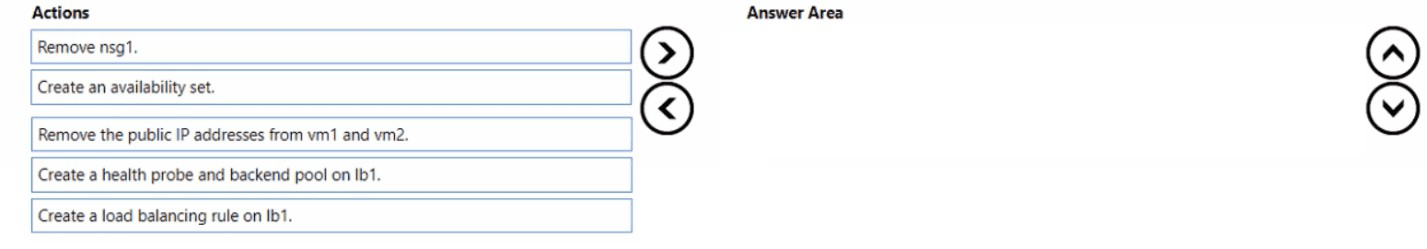
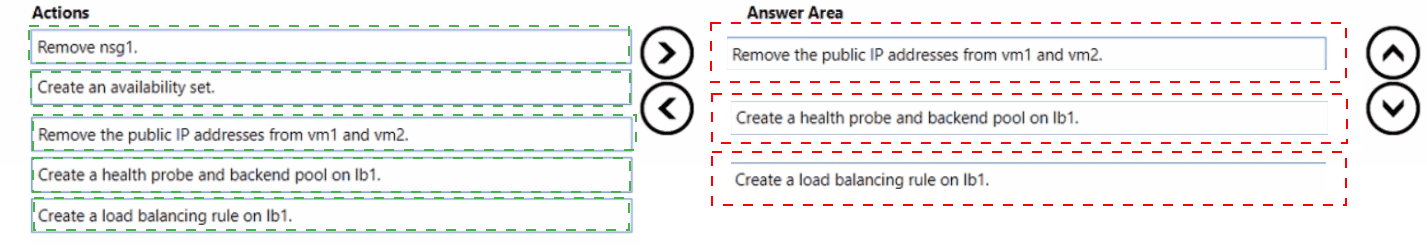
Explanation:
This question tests the steps required to convert two standalone VMs with individual public IPs into a high-availability set load-balanced by a Standard SKU Load Balancer for HTTPS (port 443). The Standard Load Balancer requires VMs to be in a backend pool, which itself requires specific configurations. The order is crucial.
Correct Sequence & Justification:
Remove the public IP addresses from vm1 and vm2.
Why first? The end goal is for clients to connect to the load balancer's public IP address, not directly to the VMs. The VMs' individual basic public IP addresses must be removed so that all inbound HTTPS traffic is forced to come through the load balancer's frontend IP. This is a prerequisite for proper load balancer functionality.
Create an availability set and add vm1 and vm2 to it.
Why second? For a Standard Load Balancer's backend pool, the VMs must be placed into a high-availability construct. The two primary options are an Availability Set or an Availability Zone. Since the table doesn't mention zones, the correct step is to create an Availability Set. This ensures the VMs are placed across different fault and update domains, meeting the high-availability requirement for the load-balanced solution.
Create a health probe and backend pool on lb1.
Why third? After the VMs are prepared (no individual PIPs, in an availability set), you configure the load balancer. The backend pool is the logical grouping of the VMs (vm1 and vm2) that will receive traffic. The health probe (e.g., on port 443) is essential for the load balancer to determine which VM instances are healthy and can receive traffic. This configuration must be done before creating the rule that directs traffic.
*(The final step, implied to complete the solution but not part of the three you select in sequence, would be: Create a load balancing rule on lb1. This rule ties the frontend IP/port (e.g., FrontendIP:443) to the backend pool and health probe, defining the distribution logic.)*
Why Other Actions Are Not in the Sequence:
Remove nsg1:
The existing NSG allowing port 443 is still useful and likely necessary for the load balancer's health probe and for the VMs to accept the load-balanced traffic. Removing it is not a required step and could break connectivity.
Create a load balancing rule on lb1:
This is a critical final step, but it logically comes after the backend pool and health probe are created, as the rule references them. The question asks for the first three sequential actions to set up the foundation.
Reference:
Microsoft Learn documentation, "Tutorial: Load balance internet traffic to VMs using Azure Load Balancer". The standard procedure is: 1) Create VMs in an availability set (or zone), 2) Create a Standard Load Balancer, 3) Create a backend pool and add VMs, 4) Create a health probe, and 5) Create a load-balancing rule.
You have an Azure subscription that contains a resource group named RG1.
You need to prevent administrators from inadvertently modifying the resources in RG1.
How should you complete the PowerShell command? To answer, select the options in the
answer area.
NOTE: Each correct answer is worth one point.
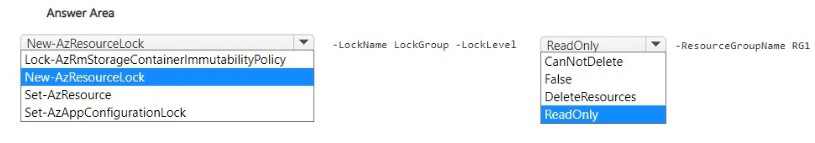
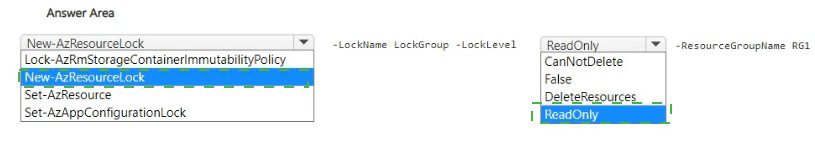
Explanation:
This question tests the use of PowerShell to create an Azure Resource Manager lock. Management locks prevent accidental modification or deletion of resources. A ReadOnly lock prevents all modifications, while a CanNotDelete lock only prevents deletion. The scenario requires preventing administrators from "inadvertently modifying" resources, which calls for the stricter ReadOnly lock.
Correct Command and Options:
The completed PowerShell command to place a ReadOnly lock on the resource group RG1 is:
text
New-AzResourceLock -LockName
Cmdlet: New-AzResourceLock
This is the correct cmdlet specifically designed to create a new management lock on Azure resources or resource groups. The other cmdlets (Lock-AzRmStorageContainerImmutabilityPolicy, Set-AzResource, Set-AzAppConfigurationLock) are for specific, different types of locks or settings.
Parameter for Lock Type: ReadOnly
The -LockLevel parameter accepts either ReadOnly or CanNotDelete. Since the requirement is to prevent modification (not just deletion), the ReadOnly lock is necessary. It blocks all write/update operations, effectively preventing inadvertent changes.
Parameter for Scope: -ResourceGroupName RG1
The -ResourceGroupName parameter specifies the target scope for the lock. Placing the lock at the resource group level applies the lock to all resources within RG1, meeting the requirement to protect all resources in that group.
Incorrect Options:
Lock-AzRmStorageContainerImmutabilityPolicy:
This cmdlet is for enabling immutable blob storage policies on a specific container, not for creating a general ARM management lock on a resource group.
CanNotDelete:
This lock level only prevents deletion. Resources could still be reconfigured or updated, which does not fully meet the goal of preventing modification.
DeleteResources / False:
These are not valid values for the -LockLevel parameter in the New-AzResourceLock cmdlet.
Reference:
Microsoft Learn documentation, "Lock resources to prevent unexpected changes". The article details using the New-AzResourceLock PowerShell cmdlet with the -LockLevel parameter set to ReadOnly or CanNotDelete to lock a subscription, resource group, or resource.
You have an Azure subscription.
You plan to deploy a container.
You need to recommend which Azure services can scale the container automatically.
What should you recommend?
A. Azure Container Apps only
B. Azure Container Instances only
C. Azure Container Apps or Azure App Service only
D. Azure Container Instances or Azure App Service only
E. Azure Container Apps, Azure Container Instances, or Azure App Service
Explanation:
This question tests knowledge of the scaling capabilities of different Azure compute services that support containers. Automatic scaling refers to the ability of a service to increase or decrease the number of running container instances based on metrics like CPU, memory, or HTTP requests, without manual intervention.
Correct Option:
C. Azure Container Apps or Azure App Service only is the correct answer.
Azure Container Apps is a serverless container service built for microservices. It has built-in autoscaling based on HTTP traffic, CPU, memory, or custom metrics (using KEDA).
Azure App Service has robust autoscale capabilities for its web apps, which include containers deployed to Web App for Containers. You can configure scale-out and scale-in rules based on metrics and schedules.
Both services support fully managed, rule-based automatic scaling of container instances.
Incorrect Options:
A. Azure Container Apps only / B. Azure Container Instances only:
These are incorrect because they exclude other valid services (App Service) that also provide autoscaling for containers.
D. Azure Container Instances or Azure App Service only:
This is incorrect because Azure Container Instances (ACI) is a serverless container service for running individual containers or container groups, but it does not natively support automatic scaling. You must manually start, stop, or scale ACI groups.
E. Azure Container Apps, Azure Container Instances, or Azure App Service:
This is incorrect because it includes Azure Container Instances, which lacks native autoscaling. While you could build an autoscaling solution on top of ACI using logic apps or functions, it is not an inherent, built-in feature like it is in Container Apps or App Service.
Reference:
Microsoft Learn documentation:
Azure Container Apps: "Autoscaling in Azure Container Apps" details its event-driven autoscaler.
Azure App Service: "Scale up an app in Azure App Service" and "Set up autoscale for Azure App Service" cover its scaling capabilities.
Azure Container Instances: The service overview highlights its simplicity and per-second billing but does not list autoscaling as a core feature; scaling requires manual intervention or custom automation.
You have an Azure App Services web app named App1.
You plan to deploy App1 by using Web Deploy.
You need to ensure that the developers of App1 can use their Azure Active Directory
(Azure AD) credentials to deploy content to App1. The solution must use the principle of
least privilege.
What should you do?
A. Configure app-level credentials for FTPS.
B. Assign The Website Contributor role to the developers
C. Assign the Owner role to the developers.
D. Configure user-level credentials for FTPS.
Explanation:
This question tests secure deployment practices for Azure App Service using the principle of least privilege. The goal is to allow deployment via Web Deploy using Azure AD credentials, not separate FTP credentials. This requires granting specific Azure RBAC permissions at the App Service scope.
Correct Option:
B. Assign the Website Contributor role to the developers.
This is the precise built-in role for managing web apps without granting broader subscription or resource group control. It grants permissions needed for deployment (like Microsoft.Web/sites/publish/Action) and general management of the app. When assigned to the developers at the App1 scope, they can use their Azure AD identities to authenticate Web Deploy (via the "Get Publish Profile" option in the portal, which includes an Azure AD-authenticated endpoint), fulfilling the requirement with least privilege.
Incorrect Options:
A. Configure app-level credentials for FTPS / D. Configure user-level credentials for FTPS:
These options involve creating separate FTP/FTPS credentials (either for the app or per user). This violates the requirement to use Azure AD credentials. It also creates additional secrets to manage, which is less secure than integrated Azure AD authentication.
C. Assign the Owner role to the developers:
The Owner role grants full control, including the ability to modify permissions and delete the resource. This is excessive and violates the principle of least privilege. The Website Contributor role provides sufficient permissions for deployment without the unnecessary administrative power of the Owner role.
Reference:
Microsoft Learn documentation, "Deploy to App Service using Azure Active Directory authentication". This guide explains that to deploy using Azure AD credentials (via the WEBSITE_WEBDEPLOY_USE_AAD setting or the built-in publish profile), the user must have an appropriate RBAC role like Website Contributor or Contributor on the App Service resource. The Website Contributor role is specifically designed as the least-privilege role for this task.
You have an on-premises network.
You have an Azure subscription that contains two virtual networks named VNet1 and
VNet2. VNet1 uses an IP address space of 192.168.8.0/24. VNet2 uses an IP address
space of 192.168.9.0/24.
You need to configure the virtual networks. The solution must meet the following
requirements:
* Ensure that the resources on VNet1 can communicate with the resources on VNet2.
* Ensure that the resources on the on-premises network can communicate with Azure
resources.
* Minimize costs
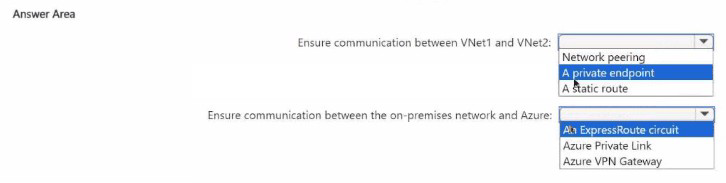
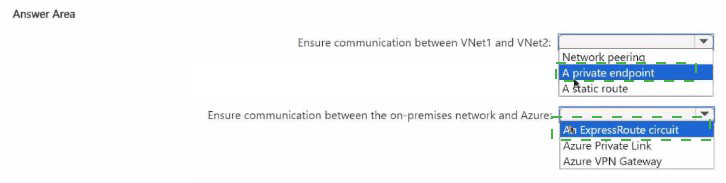
Explanation:
This question tests the selection of appropriate and cost-effective connectivity solutions for different Azure networking scenarios. The requirements are: 1) Connect two Azure VNets, and 2) Connect an on-premises network to Azure. The key constraint is to minimize costs.
Correct Options:
Ensure communication between VNet1 and VNet2: Network peering
VNet Peering is the native, recommended, and most cost-effective method for connecting two virtual networks within the same Azure region (Global VNet Peering for different regions). It creates a direct, low-latency link over the Microsoft backbone. There is no gateway device required and no data transfer charges for traffic between the peered VNets in the same region, aligning perfectly with cost minimization.
Ensure communication between the on-premises network and Azure: Azure VPN Gateway
To connect an on-premises network to Azure, the two primary options are Site-to-Site VPN (VPN Gateway) and ExpressRoute. The requirement to minimize costs dictates choosing Azure VPN Gateway. ExpressRoute provides a private, dedicated connection with higher reliability and bandwidth but at a significantly higher cost (circuit fees, provider charges). A Site-to-Site VPN over the public internet using a VPN Gateway is the standard, lower-cost solution for hybrid connectivity.
Incorrect Options:
For VNet-to-VNet:
A private endpoint:
This is for securely connecting to a specific Azure PaaS service (like Storage, SQL DB) from a VNet, not for general network-to-network connectivity between two VNets.
A static route:
Static routes are configuration elements used within a route table to direct traffic. By themselves, they do not establish connectivity. They might be used in conjunction with a gateway or peering, but are not the primary connectivity solution.
For On-premises-to-Azure:
An ExpressRoute circuit:
While it meets the connectivity requirement, it is a premium, high-cost service and therefore does not satisfy the "minimize costs" requirement.
Azure Private Link:
Similar to a private endpoint, Private Link is for accessing specific Azure PaaS and partner services privately from on-premises or a VNet. It is not a general network connectivity solution for connecting an entire on-premises network to an Azure VNet.
Reference:
Microsoft Learn documentation on "Virtual network peering" and "About VPN Gateway". The peering documentation highlights it as the preferred, low-latency, high-bandwidth connection between VNets. The VPN Gateway documentation positions it as the standard, cost-effective way to create a cross-premises connection.
| Page 3 out of 45 Pages |