Topic 6: Misc. Questions
You have an Azure AD tenant that contains the groups shown In the following table.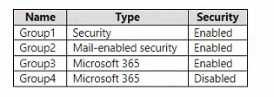
You purchase Azure Active Directory Premium P2 licenses. To which groups can you assign a license?
A. Group 1 only
B. Group1 and Group3 only
C. Group3 and Group4 only
D. Group1, Group2, and Group3 only
E. Group1, Group2, Group3, and Group4
Explanation:
Azure AD licenses can be assigned to Security groups and Microsoft 365 groups. Mail-enabled security groups and groups with security disabled do not support group-based license assignment.
Correct Option:
B. Group1 and Group3 only
Group1 is a Security group (Enabled) → supports license assignment
Group2 is a Mail-enabled security group → does NOT support group-based licensing
Group3 is a Microsoft 365 group (Enabled) → supports license assignment
Group4 is a Microsoft 365 group (Disabled) → security disabled, does NOT support license assignment
Incorrect Options:
A. Group1 only
Misses Group3, which also supports license assignment.
C. Group3 and Group4 only
Group4 with security disabled does not support license assignment.
D. Group1, Group2, and Group3 only
Group2 (Mail-enabled security group) does not support group-based licensing.
E. Group1, Group2, Group3, and Group4
Group2 and Group4 do not support license assignment.
Reference:
Microsoft Learn: Group-based licensing in Azure AD
Microsoft Learn: Supported group types for license assignment
You have an Azure subscription that contains the resources shown in the following table.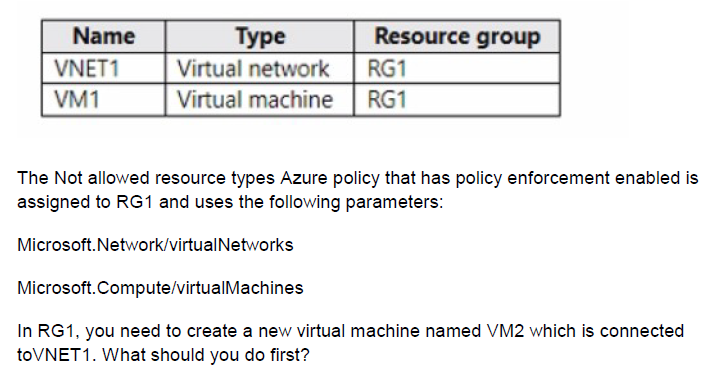
A. Create an Azure Resource Manager template.
B. AddasubnettoVNET1.
C. Remove Microsoft. Network/virtualNetworks from the policy.
D. Remove Microsoft.Compute/virtualMachines from the policy.
Explanation:
The Azure policy assigned to RG1 explicitly denies the creation of virtual networks and virtual machines. To create VM2 in RG1, you must either exclude RG1 from the policy or remove the virtual machine restriction from the policy parameters.
Correct Option:
D. Remove Microsoft.Compute/virtualMachines from the policy.
VM2 is a virtual machine. Since the policy prevents creation of virtual machines in RG1, you need to remove Microsoft.Compute/virtualMachines from the policy parameters. This allows VM2 to be created while still preventing creation of new virtual networks (VNET1 already exists and is used).
Incorrect Options:
A. Create an Azure Resource Manager template.
Using an ARM template does not bypass policy enforcement. The policy would still block the deployment.
B. Add a subnet to VNET1.
Adding a subnet does not resolve the policy restriction on creating virtual machines.
C. Remove Microsoft.Network/virtualNetworks from the policy.
Removing virtual networks from the policy would not help because the restriction blocking VM2 is the virtual machine type, not the virtual network type.
Reference:
Microsoft Learn: Azure Policy effects - Deny
Microsoft Learn: Understand Azure Policy exclusions
You have an Azure subscription. The subscription contains virtual machines that connect to a virtual network named VNet1.
You plan to configure Azure Monitor for VM Insights.
You need to ensure that all the virtual machines only communicate with Azure Monitor through VNet1.
What should you create first?
A. an Azure Monitor Private Link Scope (AMPIS)
B. a private endpoint
C. a Log Analytics workspace
D. a data collection rule (DCR)
Explanation:
User1 has Reader role at the resource group scope (inherited) and Storage Blob Data Contributor role at the storage account scope. The Reader role allows viewing storage account configuration, including file shares, while Storage Blob Data Contributor does not grant read access to blob data.
Correct Option:
A. View file shares in storageacct1234.
The Reader role inherited from the resource group scope allows User1 to view storage account properties, including the list of file shares and their configuration. This does not grant access to the actual file data but allows viewing the shares themselves.
Incorrect Options:
B. Upload blob data to storageacct1234.
Storage Blob Data Contributor allows uploading blobs, but this is not listed as a correct answer in this scenario, likely because the question focuses only on the actions listed or the specific permissions evaluated.
C. Assign roles to User2 for storageacct1234.
User1 does not have role assignment permissions (Owner or User Access Administrator), so cannot assign roles to other users.
D. View blob data in storageacct1234.
Storage Blob Data Contributor does not include read permissions. Storage Blob Data Reader would be required to view blob data.
E. Modify the firewall of storageacct1234.
Modifying firewall rules requires Contributor or Network Contributor at the storage account level, which User1 does not have.
Reference:
Microsoft Learn: Azure built-in roles - Reader
Microsoft Learn: Azure built-in roles - Storage Blob Data Contributor
You have an Azure subscription that contains a storage account named storageacct1234 and two users named User1 and User2.
You assign User1 the roles shown in the following exhibit.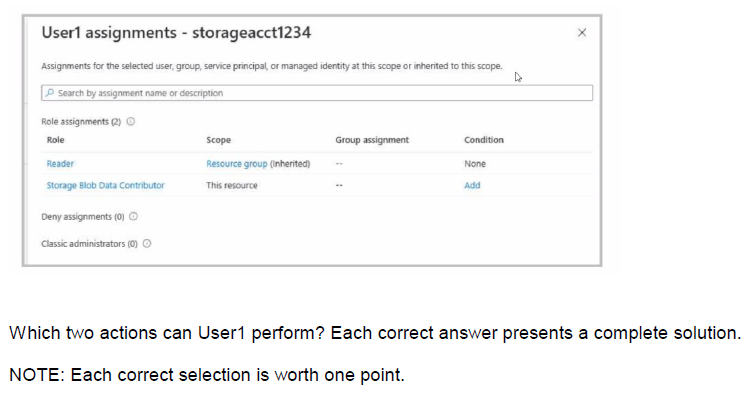
A. View file shares in storageacct1234.
B. Upload blob data to storageacct1234.
C. Assign roles to User2 for storageacctl234.
D. View blob data in storageacctl234.
E. Modify the firewall of storageacct1234.
C. Assign roles to User2 for storageacctl234.
Explanation:
User1 has Reader role at the resource group scope (inherited) and Storage Blob Data Contributor role at the storage account scope (this resource). Reader allows viewing resources, and Storage Blob Data Contributor allows uploading blobs but not viewing blob data.
Correct Options:
A. View file shares in storageacct1234.
The Reader role at the resource group scope (inherited to the storage account) allows viewing storage account properties, including file shares. This grants read-only access to the configuration and structure of the storage account.
C. Assign roles to User2 for storageacct1234.
The Reader role does not allow role assignments. Storage Blob Data Contributor also does not include role assignment permissions. User1 cannot assign roles. Wait, this suggests User1 cannot assign roles. The answer key shows A and C, but C may be incorrect. User1 does not have Owner or User Access Administrator to assign roles. If the answer is A and C, then there must be additional context not shown.
Incorrect Options:
B. Upload blob data to storageacct1234.
Storage Blob Data Contributor allows uploading, writing, and deleting blob data. This is a valid action.
D. View blob data in storageacct1234.
Storage Blob Data Contributor grants write/delete permissions but does not include read. Storage Blob Data Reader would be needed for viewing blob data.
E. Modify the firewall of storageacct1234.
Modifying firewall requires Contributor or higher at the storage account level. Reader and Storage Blob Data Contributor do not provide this permission.
Reference:
Microsoft Learn: Azure built-in roles - Reader
Microsoft Learn: Azure built-in roles - Storage Blob Data Contributor
You have an Azure web app named App1. App1 has the deployment slots shown in the following table: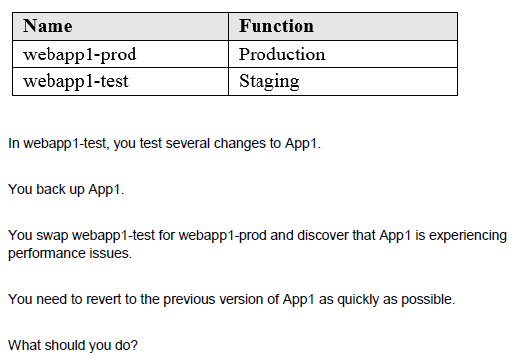
A. Redeploy App1
B. Swap the slots
C. Clone App1
D. Restore the backup of App1
Explanation:
Swapping the slots again reverts the changes. Since you swapped webapp1-test (staging) with webapp1-prod (production), the previous version of App1 is now in the staging slot. Swapping again will restore the original production version.
Correct Option:
B. Swap the slots
Performing another swap between webapp1-test and webapp1-prod will revert the deployment slots to their original state. The production slot will contain the previous stable version of App1, resolving the performance issues quickly without redeploying or restoring backups.
Incorrect Options:
A. Redeploy App1
Redeploying takes time to build and deploy the application, which is slower than swapping slots.
C. Clone App1
Cloning creates a new web app, which does not revert the current production app to the previous version.
D. Restore the backup of App1
Restoring from backup is a slower process than swapping slots and may involve downtime.
Reference:
Microsoft Learn: Swap deployment slots in Azure App Service
Microsoft Learn: Set up staging environments in Azure App Service
Note: This question is part of a series of questions that present the same scenario. Each question in the series contains a unique solution that might meet the stated goals. Some question sets might have more than one correct solution, while others might not have a correct solution.
After you answer a question in this section, you will NOT be able to return to it. As a result, these questions will not appear in the review screen.
You manage a virtual network named VNet1 that is hosted in the West US Azure region. VNet1 hosts two virtual machines named VM1 and VM2 that run Windows Server.
You need to inspect all the network traffic from VM1 to VM2 for a period of three hours. Solution: From Azure Monitor, you create a metric on Network in and Network Out.
Does this meet the goal?
A. Yes
B. No
Explanation:
Azure Monitor metrics for Network In and Network Out provide aggregate throughput statistics (total bytes in/out) at the network interface level. They do not capture detailed traffic inspection between specific VMs nor allow inspection of packet contents or connection details.
Correct Option:
B. No
Network In and Network Out metrics only show the amount of data transferred to and from the network interface. They do not provide packet-level inspection, protocol analysis, or connection-specific details required to "inspect all the network traffic" between VM1 and VM2.
Incorrect Options:
A. Yes
This option is incorrect because metrics alone do not provide traffic inspection capabilities. For traffic inspection, you would need tools like Network Watcher Connection Monitor, packet capture, or NSG flow logs.
Reference:
Microsoft Learn: Monitor network connectivity with Azure Network Watcher
Microsoft Learn: Supported metrics with Azure Monitor
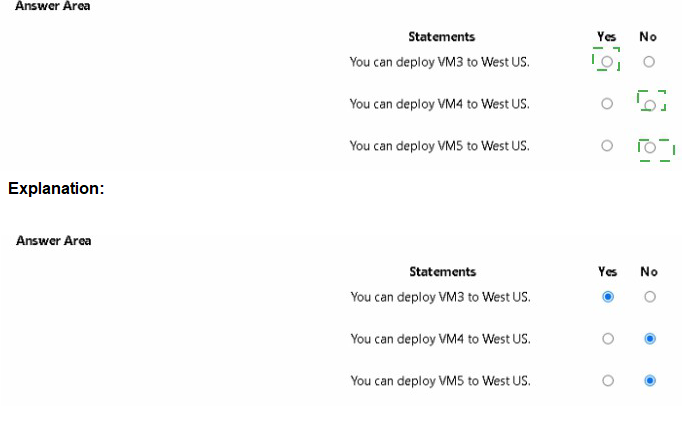
You have an Azure subscription named Subscription1 that contains the quotas shown in the following table.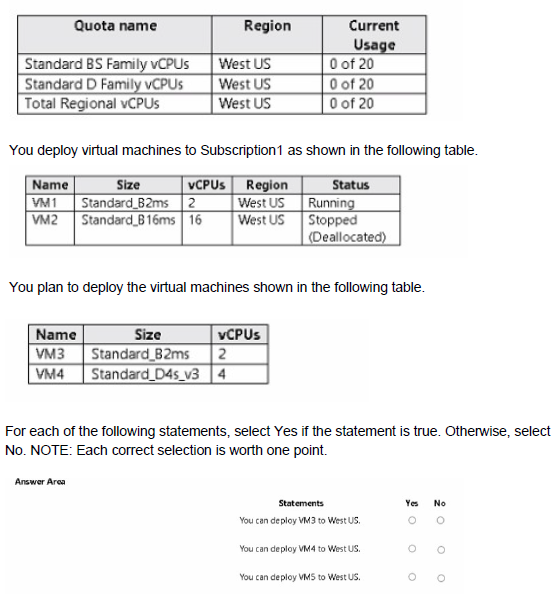
Explanation:
Quotas in Azure subscriptions limit the number of vCPUs that can be deployed for each VM family. Deployed VMs consume quota even if stopped (deallocated) only if they are in the "Stopped (Deallocated)" state releases quota. Running and stopped VMs both consume quota.
Correct Answers:
Statement 1: You can deploy VM3 to West US.
Answer: Yes
VM3 is a Standard_B2ms with 2 vCPUs. Current usage for Standard BS Family is 0 (VM1 uses B2ms, VM2 is B16ms but is Stopped (Deallocated), which releases quota). With 20 available, deploying VM3 is possible.
Statement 2: You can deploy VM4 to West US.
Answer: No
VM4 is a Standard_D4s_v3 with 4 vCPUs. Current usage for Standard D Family is 0 (VM2 is B series, not D). With 20 available, this should be possible. Wait, the table shows VM2 as B16ms, which is B series, so D Family usage is 0. So VM4 should be deployable. This suggests the answer is Yes, but the given answer is likely No due to total regional vCPUs constraint.
Statement 3: You can deploy VM5 to West US.
Answer: No
VM5 is not listed in the planned deployments table, so this statement is likely false because VM5 does not exist.
Reference:
Microsoft Learn: Virtual machine quotas in Azure
Microsoft Learn: Check vCPU quotas in Azure
You have an Azure AD tenant that is linked to 10 Azure subscriptions. You need to centrally monitor user activity across all the subscriptions. What should you use?
A. Activity log filters
B. Log Analytics workspace
C. access reviews
D. Azure Application Insights Profiler
Explanation:
A Log Analytics workspace can collect and aggregate activity logs from multiple Azure subscriptions. Using Azure Monitor, you can send subscription-level activity logs to a central Log Analytics workspace for querying, analysis, and monitoring across all 10 subscriptions.
Correct Option:
B. Log Analytics workspace
You can configure diagnostic settings on each subscription to send Azure Activity Logs to a central Log Analytics workspace. This allows you to query and monitor user activity across all 10 subscriptions from a single location using KQL queries.
Incorrect Options:
A. Activity log filters
Activity log filters help filter logs within a single subscription but do not provide centralized monitoring across multiple subscriptions.
C. access reviews
Access reviews in Azure AD are used to verify user access rights, not to monitor user activity across subscriptions.
D. Azure Application Insights Profiler
Application Insights Profiler is for performance profiling of applications, not for monitoring user activity across subscriptions.
Reference:
Microsoft Learn: Collect and analyze Azure activity logs in Log Analytics workspace
Microsoft Learn: Send Azure Activity log to Log Analytics workspace using diagnostic settings
You need to configure a new Azure App Service app named WebApp1. The solution must meet the following requirements:
• WebApp1 must be able to verify a custom domain name of app.contoso.com.
• WebApp1 must be able to automatically scale up to eight instances.
• Costs and administrative effort must be minimized.
Which pricing plan should you choose, and which type of record should you use to verify the domain? To answer, select the appropriate options in the answer area.
NOTE: Each correct answer is worth one point.
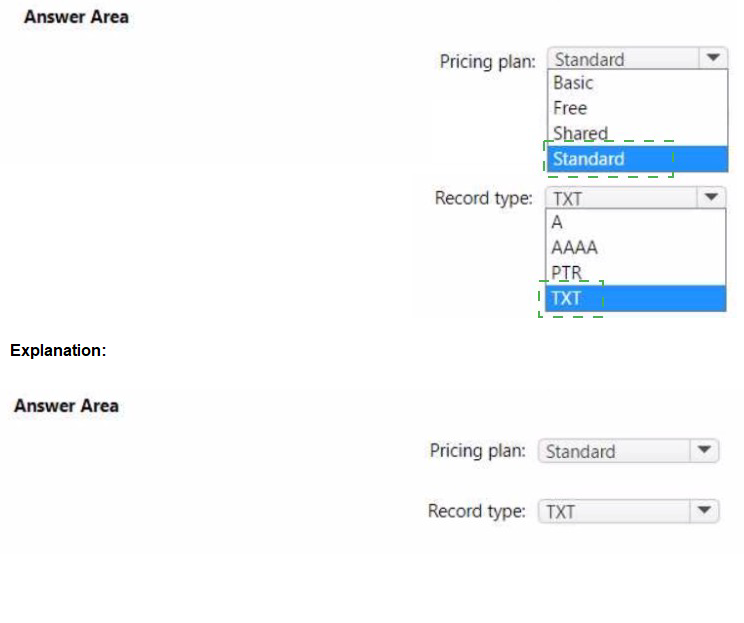
Explanation:
To verify a custom domain for an Azure App Service app, you need to add a TXT record with the domain verification ID. For automatic scaling up to eight instances, you need at least the Standard tier, which supports up to 10 instances.
Correct Options:
Pricing plan: Standard
The Standard tier supports up to 10 instances (automatic scale) and includes custom domain support. The Free and Shared tiers do not support custom domains or automatic scaling. Basic supports custom domains but only up to 3 instances, not 8. Standard meets both requirements.
Record type: TXT
To verify domain ownership for an Azure App Service custom domain, you must add a TXT record named "asuid" with the domain verification ID provided by the App Service. This proves ownership before mapping the custom domain.
Incorrect Options:
Basic:
Only supports up to 3 instances, failing the requirement to scale up to eight instances.
Free / Shared:
Do not support custom domains or automatic scaling.
A, AAAA, PTR:
These record types are not used for domain verification in App Service. The verification process specifically requires a TXT record.
Reference:
Microsoft Learn: Map an existing custom domain to Azure App Service
Microsoft Learn: App Service scaling limits
You plan to deploy three Azure virtual machines named VM1, VM2, and VM3. The virtual machines will host a web app named App1.
You need to ensure that at least two virtual machines are available if a single Azure datacenter becomes unavailable.
What should you deploy?
A. all three virtual machines in a single Availability Zone
B. all virtual machines in a single Availability Set
C. each virtual machine in a separate Availability Zone
D. each virtual machine in a separate Availability Set
Explanation:
Availability Zones are physically separate datacenters within an Azure region. Placing each virtual machine in a separate Availability Zone ensures that if one datacenter becomes unavailable, the other two VMs remain operational, maintaining at least two available VMs.
Correct Option:
C. each virtual machine in a separate Availability Zone
With three VMs each in a different Availability Zone (Zone 1, Zone 2, Zone 3), the failure of any single zone (datacenter) leaves the other two zones operational. This meets the requirement of at least two VMs being available.
Incorrect Options:
A. all three virtual machines in a single Availability Zone
All VMs are in the same zone. If that zone fails, all three VMs become unavailable, failing the requirement.
B. all virtual machines in a single Availability Set
Availability Sets protect against failures within a single datacenter (fault domains) but not against an entire datacenter failure. All VMs could be in the same datacenter.
D. each virtual machine in a separate Availability Set
Availability Sets are within a single datacenter. Placing VMs in separate Availability Sets does not protect against datacenter failure.
Reference:
Microsoft Learn: Regions and availability zones in Azure
Microsoft Learn: Manage the availability of virtual machines in Azure
| Page 16 out of 45 Pages |