Topic 4: Mix Questions
You have an Azure subscription named Sub1.
You have an Azure Active Directory (Azure AD) group named Group1 that contains all the
members of your IT team.
You need to ensure that the members of Group1 can stop, start, and restart the Azure
virtual machines in Sub1. The solution must use the principle of least privilege.
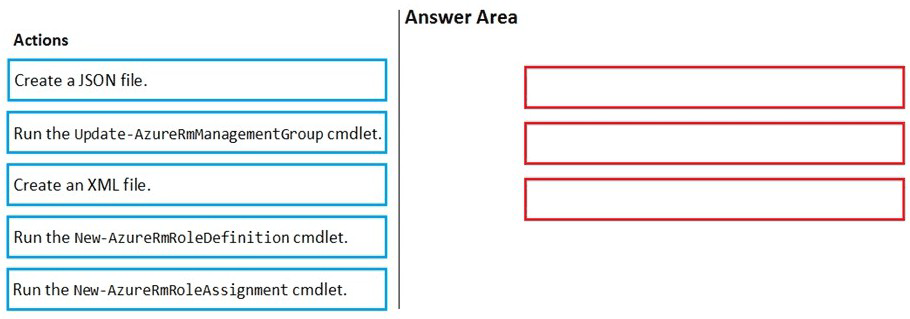
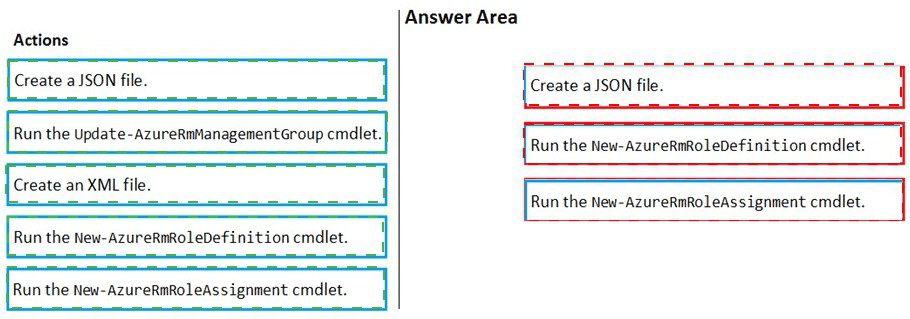
Which three actions should you perform in sequence? To answer, move the appropriate
actions from the list of actions to the answer area and arrange them in the correct order.
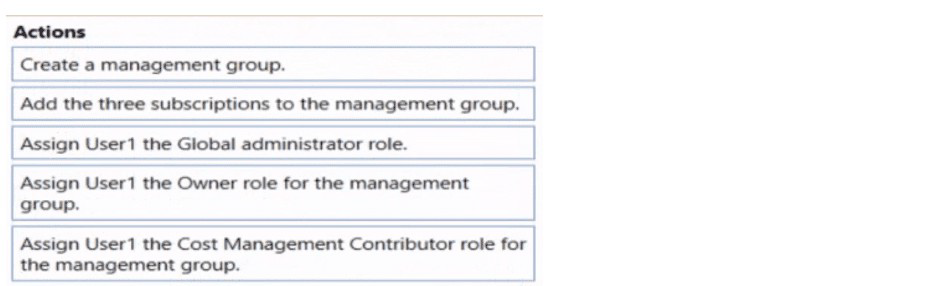
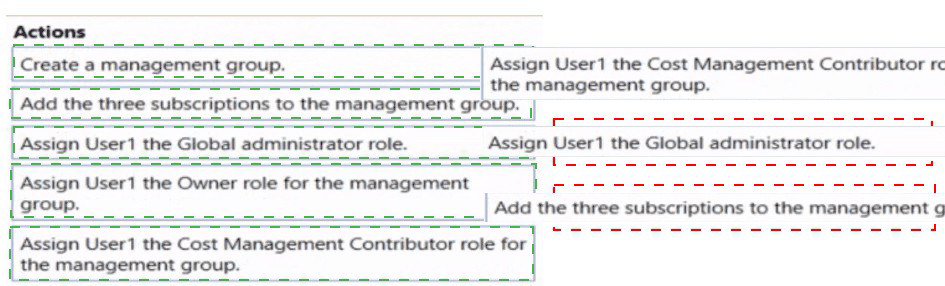
You have three Azure subscriptions and a user named User1.
You need to provide User1 with the ability to manage and view costs for the resources
across all three subscriptions. The solution must use the principle of least privilege.
Which three actions should you perform in sequence? To answer, move the appropriate
actions from the list of actions to the answer area and arrange them in the correct order.
NOTE: More than one order of answer choices is correct. You will receive credit for any of
the correct orders you select.
You have an Azure subscription named Sub1.
In Azure Security Center, you have a workflow automation named WF1. WF1 is configured
to send an email message to a user named User1.
You need to modify WF1 to send email messages to a distribution group named Alerts.
What should you use to modify WF1?
A. Azure Application Insights
B. Azure Monitor
C. Azure Logic Apps Designer
D. Azure DevOps
You have an Azure subscription that contains the Azure App Service apps shown in the
following table.
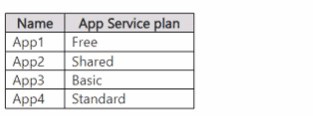
You purchase custom SSL certificates from a trusted third-party authority.
To which apps can you assign the custom SSL certificates?
A. App4 only
B. App3 and App4 only
C. App2. App3. and App4 only
D. App1. App2, App3. and App4
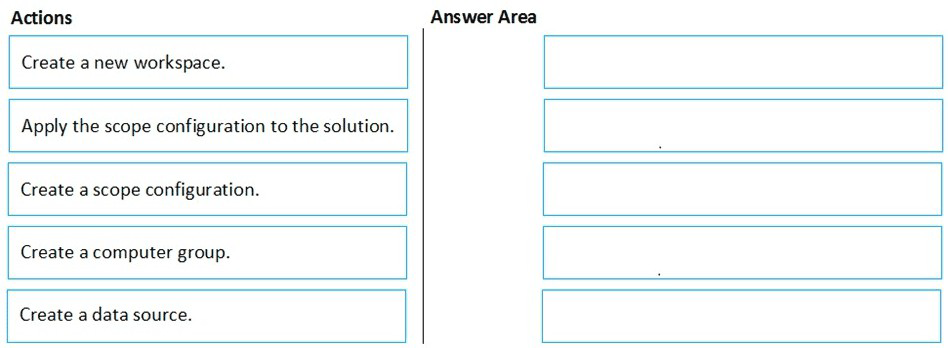
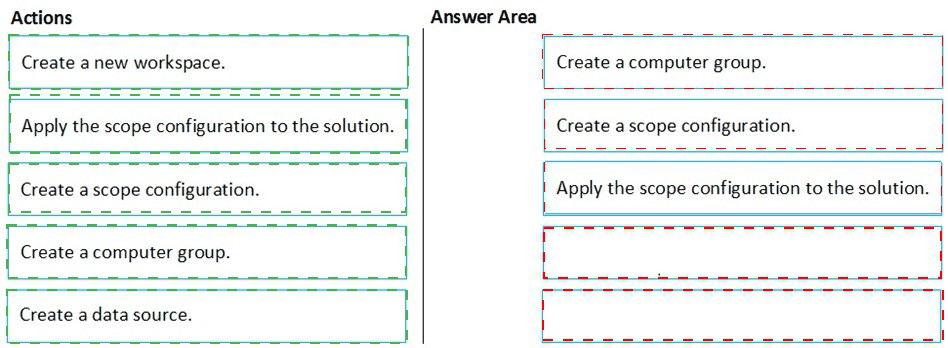
You have an Azure subscription named Sub1 that contains an Azure Log Analytics
workspace named LAW1.
You have 500 Azure virtual machines that run Windows Server 2016 and are enrolled in
LAW1.
You plan to add the System Update Assessment solution to LAW1.
You need to ensure that System Update Assessment-related logs are uploaded to LAW1
from 100 of the virtual machines only.
Which three actions should you perform in sequence? To answer, move the appropriate
actions from the list of actions to the answer area and arrange them in the correct order.
You are testing an Azure Kubernetes Service (AKS) cluster. The cluster is configured as
shown in the exhibit. (Click the Exhibit tab.)
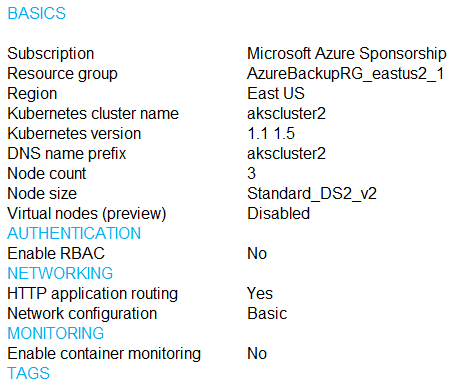
You plan to deploy the cluster to production. You disable HTTP application routing.
You need to implement application routing that will provide reverse proxy and TLS
termination for AKS services by using a single IP address.
What should you do?
A. Create an AKS Ingress controller.
B. Install the container network interface (CNI) plug-in.
C. Create an Azure Standard Load Balancer.
D. Create an Azure Basic Load Balancer.
Lab Task
use the following login credentials as needed:
To enter your username, place your cursor in the Sign in box and click on the username
below.
To enter your password. place your cursor in the Enter password box and click on the
password below.
Azure Username: Userl -28681041@ExamUsers.com
Azure Password: GpOAe4@lDg
If the Azure portal does not load successfully in the browser, press CTRL-K to reload the
portal in a new browser tab.
The following information is for technical support purposes only:
Lab Instance: 28681041
Task 8
You need to prevent HTTP connections to the rg1lod28681041n1 Azure Storage account.
Answer: Check below steps in explanation for Task.
You have Azure Resource Manager templates that you use to deploy Azure virtual
machines.
You need to disable unused Windows features automatically as instances of the virtual
machines are provisioned.
What should you use?
A. security policies in Azure Security Center
B. Azure Logic Apps
C. an Azure Desired State Configuration (DSC) virtual machine extension
D. Azure Advisor
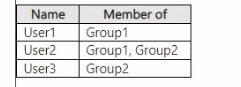
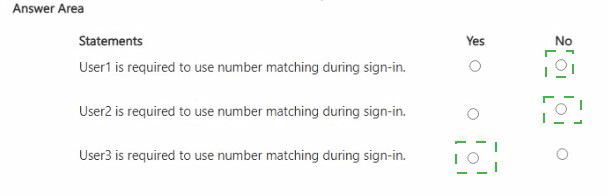
You have a Microsoft Entra tenant that contains the users shown in the following table.
You configure a Conditional Access policy that has the following settings:
• Name: CAPolicy1
• Assignments
o Users or workload identities: Group1
o Target resources: All cloud apps
• Access controls
o Grant access: Require multifactor authentication
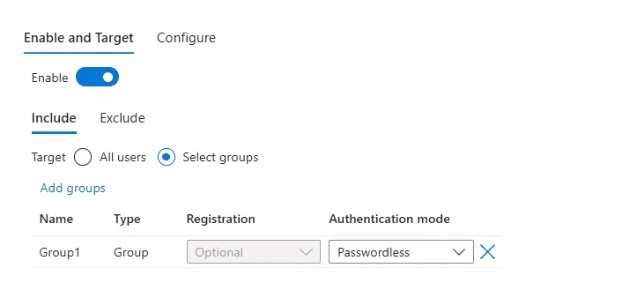
From Microsoft Authenticator settings for the tenant, the Enable and Target settings are
configured as shown in the Enable and Target exhibit. (Click the Enable and Target tab.)
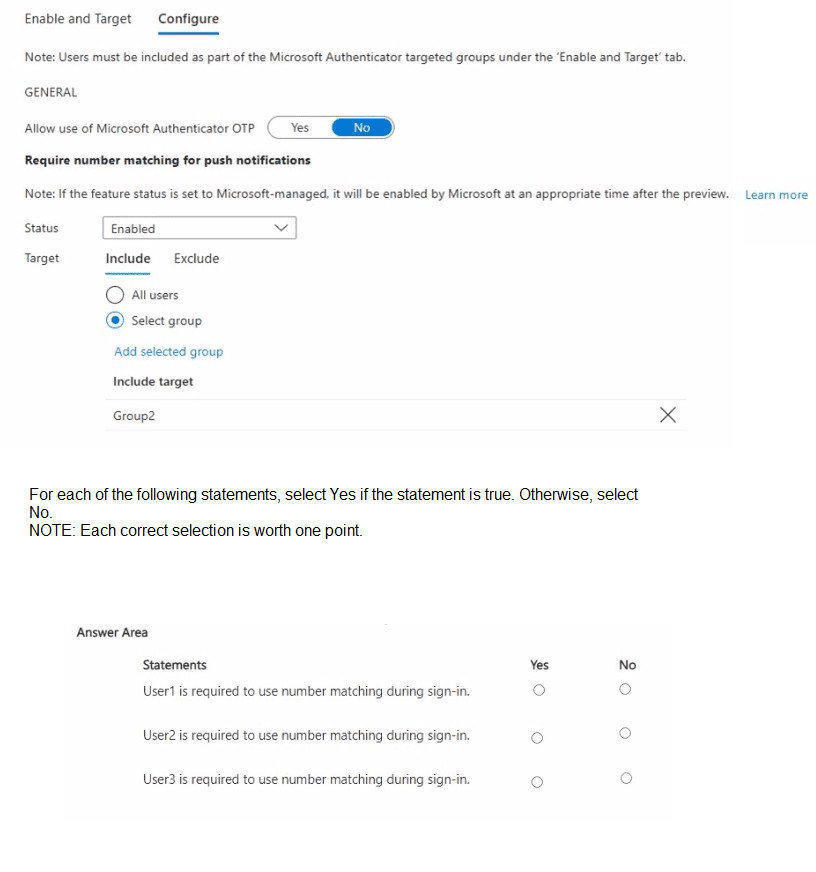
From Microsoft Authenticator settings for the tenant, the Configure settings are configured
as shown in the Configure exhibit. (Click the Configure tab.)
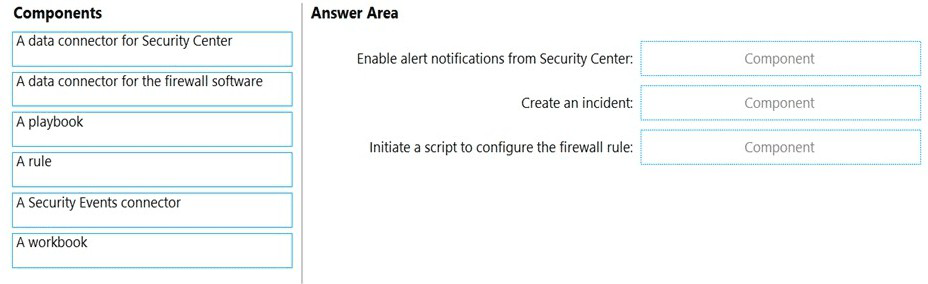
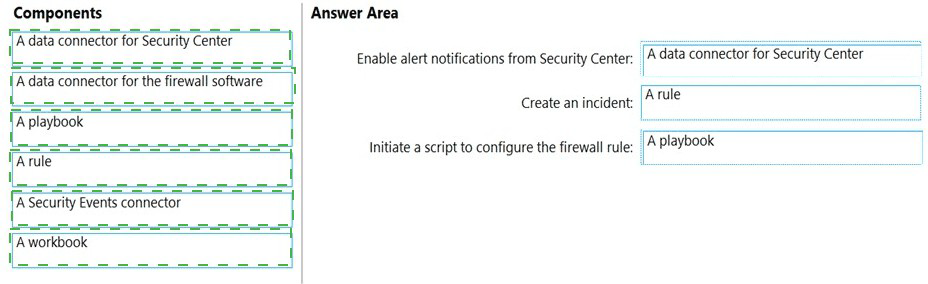
You have an Azure subscription that contains the following resources:
A network virtual appliance (NVA) that runs non-Microsoft firewall software and
routes all outbound traffic from the virtual machines to the internet
An Azure function that contains a script to manage the firewall rules of the NVA
Azure Security Center standard tier enabled for all virtual machines
An Azure Sentinel workspace
30 virtual machines
You need to ensure that when a high-priority alert is generated in Security Center for a
virtual machine, an incident is created in Azure Sentinel and then a script is initiated to
configure a firewall rule for the NVA.
How should you configure Azure Sentinel to meet the requirements? To answer, drag the
appropriate components to the correct requirements. Each component may be used once,
more than once, or not at all. You may need to drag the split bar between panes or scroll to
view content.
NOTE: Each correct selection is worth one point.
| Page 9 out of 50 Pages |