Topic 4: Mix Questions
You have been tasked with configuring an access review, which you plan to assigned to a
new collection of reviews. You also have to make sure that the reviews can be reviewed by
resource owners.
You start by creating an access review program and an access review control.
You now need to configure the Reviewers.
Which of the following should you set Reviewers to?
A. Selected users.
B. Members (Self).
C. Group Owners.
D. Anyone.
You have an Azure subscription that contains four Azure SQL managed instances.
You need to evaluate the vulnerability of the managed instances to SQL injection attacks.
What should you do first?
A. Create an Azure Sentinel workspace.
B. Enable Advanced Data Security.
C. Add the SQL Health Check solution to Azure Monitor.
D. Create an Azure Advanced Threat Protection (ATP) instance.
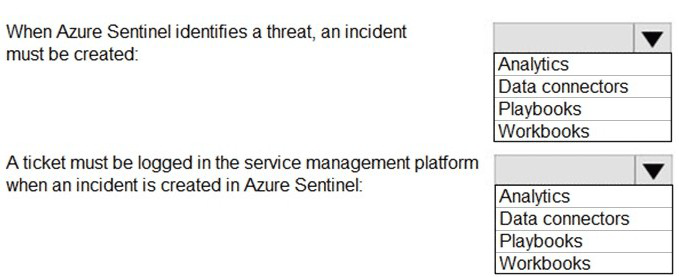
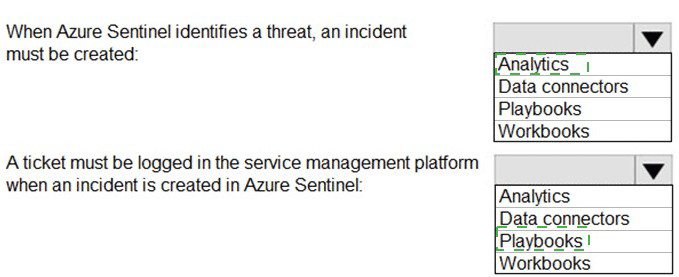
You have an Azure subscription that contains an Azure Sentinel workspace.
Azure Sentinel is configured to ingest logs from several Azure workloads. A third-party
service management platform is used to manage incidents.
You need to identify which Azure Sentinel components to configure to meet the following
requirements:
When Azure Sentinel identifies a threat, an incident must be created.
A ticket must be logged in the service management platform when an incident is
created in Azure Sentinel.
Which component should you identify for each requirement? To answer, select the
appropriate options in the answer area.
NOTE: Each correct selection is worth one point.
You have an Azure subscription named Sub1.
In Azure Security Center, you have a security playbook named Play1. Play1 is configured
to send an email message to a user named User1.
You need to modify Play1 to send email messages to a distribution group named Alerts.
What should you use to modify Play1?
A. Azure DevOps
B. Azure Application Insights
C. Azure Monitor
D. Azure Logic Apps Designer
You have an Azure subscription that uses Microsoft Defender for Cloud. The subscription
contains the Azure Policy definitions shown in the following table.
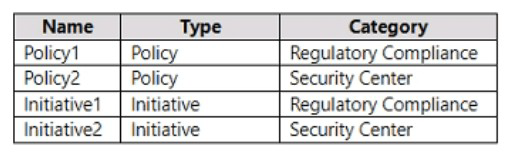
Which definitions can be assigned as a security policy in Defender for Cloud?
A. Policy1 and Policy2 only
B. Initiative1 and Initiative2 only
C. Policy1 and Initiative1 only
D. Policy2 and Initiative2 only
E. Policy1, Policy2, Initiative1, and Initiative2
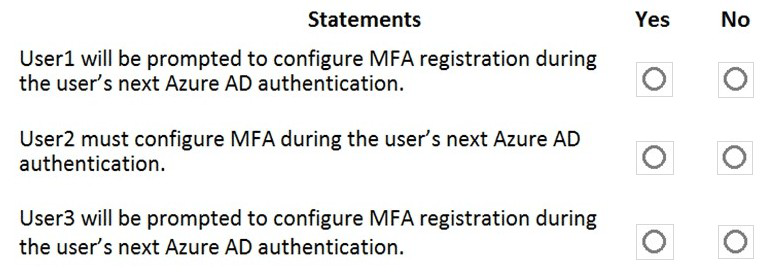
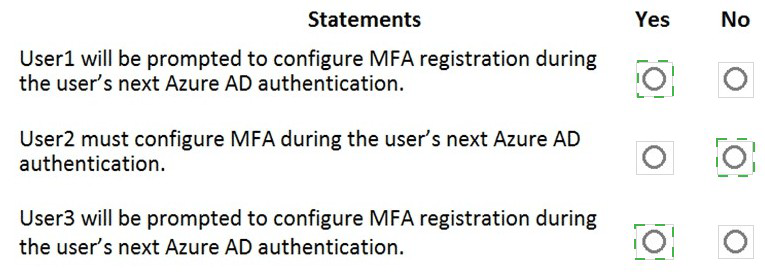
You network contains an on-premises Active Directory domain that syncs to an Azure
Active Directory (Azure AD) tenant. The tenant contains the users shown in the following
table.
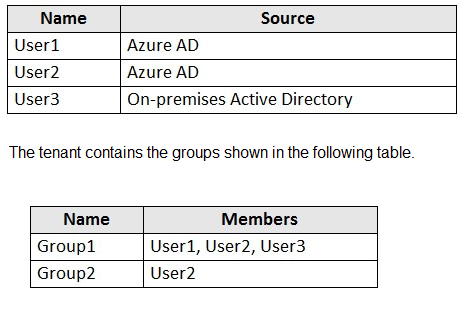
You configure a multi-factor authentication (MFA) registration policy that and the following
settings:
Assignments:
Controls: Require Azure MFA registration
Enforce Policy: On
For each of the following statements, select Yes if the statement is true. Otherwise, select No.
Lab Task
Task 7
You need to ensure that connections through an Azure Application Gateway named
Homepage-AGW are inspected for malicious requests.
Answer: see the task answer with step by step below:
You have an Azure subscription that contains a virtual network named VNet1. The
subscription contains an Azure App Service web app named App1.
You have an Azure Front Door profile named AFD1 that has an Azure Web Application
Firewall (WAF) policy.
You need to ensure that all inbound traffic to App1 is filtered through AFD1.
What should you do?
A. For VNet1, configure network security group (NSG) rules.
B. For App1, configure the HTTP headers filter settings.
C. For App1, enable virtual network integration.
D. Configure Microsoft Entra application proxy.
You have a hybrid configuration of Azure Active Directory (Azure AD). You have an Azure
SQL Database instance that is configured to support Azure AD authentication.
Database developers must connect to the database instance and authenticate by using
their on-premises
Active Directory account.
You need to ensure that developers can connect to the instance by using Microsoft SQL
Server Management
Studio. The solution must minimize authentication prompts.
Which authentication method should you recommend?
A. Active Directory - Password
B. Active Directory - Universal with MFA support
C. SQL Server Authentication
D. Active Directory - Integrated
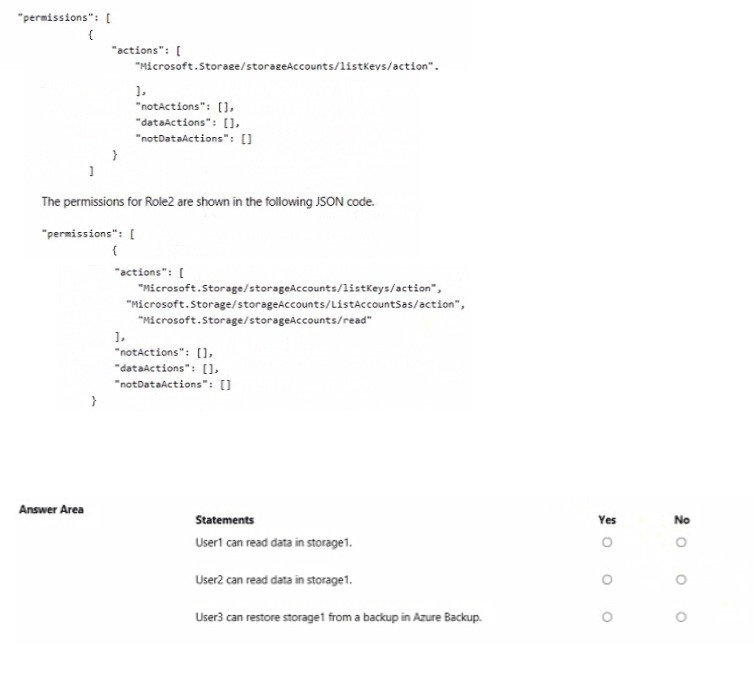
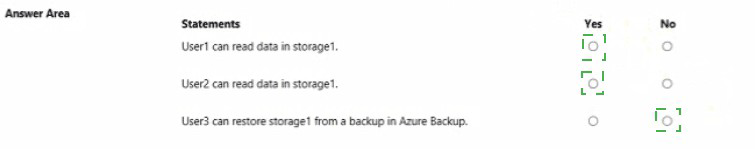
You have an Azure subscription mat contains a resource group named RG1. RG1 contains
a storage account named storage1.
You have two custom Azure rotes named Role1 and Role2 that are scoped to RG1.
The permissions for Role1 are shown in the following JSON code.
| Page 7 out of 50 Pages |