Topic 4, Misc. Questions
You need to implement a solution to resolve the retail store location data issue.
Which three Azure Blob features should you enable? Each correct answer presents pan ol
the solution.
NOTE Each correct selection is worth one point
A.
Immutability
B.
Snapshots
C.
Versioning
D.
Soft delete
E.
Object replication
F.
Change feed
Versioning
D.
Soft delete
F.
Change feed
Explanation:
Scenario: You must perform a point-in-time restoration of the retail store location data due
to an unexpected and accidental deletion of data.
Before you enable and configure point-in-time restore, enable its prerequisites for the
storage account: soft delete, change feed, and blob versioning.
Reference:
https://docs.microsoft.com/en-us/azure/storage/blobs/point-in-time-restore-manage
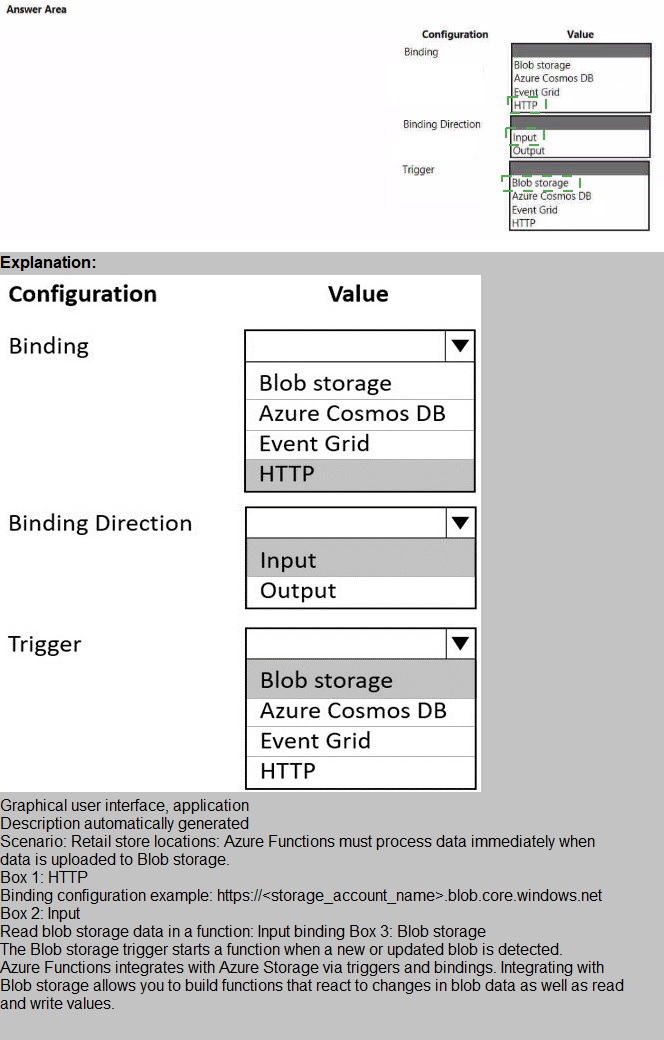
You need to Implement the retail store location Azure Function.
How should you configure the solution? To answer, select the appropriate options in the answer area. NOTE: Each correct selection is worth one point.
You need to secure the Azure Functions to meet the security requirements.
Which two actions should you perform? Each correct answer presents part of the solution.NOTE: Each correct selection is worth one point.
A.
Store the RSA-HSM key in Azure Cosmos DB. Apery the built-in policies for customermanaged
keys and allowed locations.
B.
Create a free tier Azure App Configuration instance with a new Azure AD service
principal.
C.
Store the RSA-HSM key in Azure Key Vault with soft-delete and purge-protection
features enabled.
D.
Store the RSA-HSM key in Azure Blob storage with an Immutability policy applied to the
container.
E.
Create a standard tier Azure App Configuration instance with an assigned Azure AD
managed identity.
Store the RSA-HSM key in Azure Key Vault with soft-delete and purge-protection
features enabled.
E.
Create a standard tier Azure App Configuration instance with an assigned Azure AD
managed identity.
Explanation:
Scenario: All Azure Functions must centralize management and distribution of configuration
data for different environments and geographies, encrypted by using a company-provided
RSA-HSM key.
Microsoft Azure Key Vault is a cloud-hosted management service that allows users to
encrypt keys and small secrets by using keys that are protected by hardware security
modules (HSMs).
You need to create a managed identity for your application.
Reference:
https://docs.microsoft.com/en-us/azure/app-service/app-service-key-vault-references
You need to access data from the user claim object in the e-commerce web app.
What should you do first?
A.
Write custom code to make a Microsoft Graph API call from the e-commerce web app.
B.
Assign the Contributor RBAC role to the e-commerce web app by using the Resource Manager create role assignment API.
C.
Update the e-commerce web app to read the HTTP request header values.
D.
Using the Azure CLI, enable Cross-origin resource sharing (CORS) from the ecommerce checkout API to the e-commerce web app.
Update the e-commerce web app to read the HTTP request header values.
Explanation:
Methods to Get User Identity and Claims in a .NET Azure Functions App include:
ClaimsPrincipal from the Request Context
The ClaimsPrincipal object is also available as part of the request context and can be
extracted from the HttpRequest.HttpContext.
User Claims from the Request Headers.
App Service passes user claims to the app by using special request headers.
Reference:
https://levelup.gitconnected.com/four-alternative-methods-to-get-user-identity-and-claimsin-
a-net-azurefunctions-app-df98c40424bb
You need to retrieve all order line items from Order.json and sort the data alphabetically by the city. How should you complete the code? To answer, select the appropriate options in the answer area. NOTE: Each correct selection is worth one point.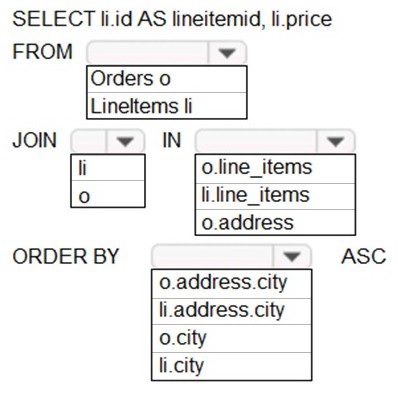
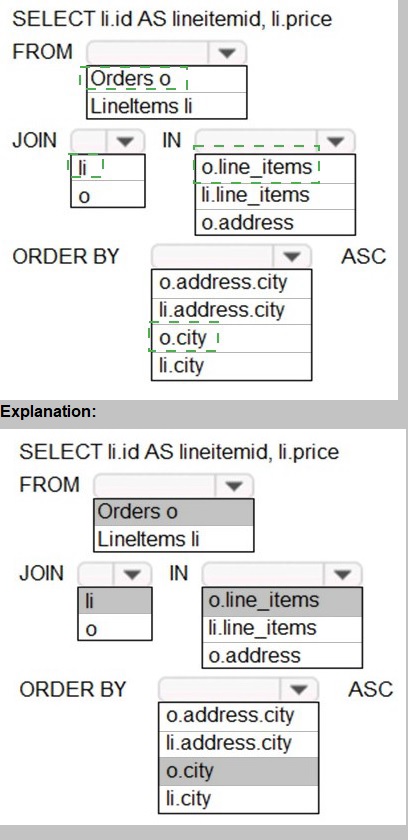
You need to add code at line PC32 in Processing.cs to implement the GetCredentials
method in the Processing class.
How should you complete the code? To answer, drag the appropriate code segments to
the correct locations. Each code segment may be used once, more than once, or not at all.
You may need to drag the split bar between panes or scroll to view content.
NOTE: Each correct selection is worth one point.
You need to resolve the log capacity issue.
What should you do?
A.
Create an Application Insights Telemetry Filter
B.
Change the minimum log level in the host.json file for the function
C.
Implement Application Insights Sampling
D.
Set a LogCategoryFilter during startup
Implement Application Insights Sampling
Explanation:
Scenario, the log capacity issue: Developers report that the number of log message in the
trace output for the processor is too high, resulting in lost log messages.
Sampling is a feature in Azure Application Insights. It is the recommended way to reduce
telemetry traffic and storage, while preserving a statistically correct analysis of application
data. The filter selects items that are related, so that you can navigate between items when
you are doing diagnostic investigations. When metric counts are presented to you in the
portal, they are renormalized to take account of the sampling, to minimize any effect on the
statistics.
Sampling reduces traffic and data costs, and helps you avoid throttling.
Reference:
https://docs.microsoft.com/en-us/azure/azure-monitor/app/sampling
You need to ensure the security policies are met.
What code do you add at line CS07 of ConfigureSSE.ps1?
A.
–PermissionsToKeys create, encrypt, decrypt
B.
–PermissionsToCertificates create, encrypt, decrypt
C.
–PermissionsToCertificates wrapkey, unwrapkey, get
D.
–PermissionsToKeys wrapkey, unwrapkey, get
–PermissionsToCertificates create, encrypt, decrypt
Explanation:
Scenario: All certificates and secrets used to secure data must be stored in Azure Key
Vault.
You must adhere to the principle of least privilege and provide privileges which are
essential to perform the intended function.
The Set-AzureRmKeyValutAccessPolicy parameter -PermissionsToKeys specifies an array
of key operation permissions to grant to a user or service principal. The acceptable values
for this parameter: decrypt, encrypt, unwrapKey, wrapKey, verify, sign, get, list, update,
create, import, delete, backup, restore, recover, purge
Reference:
https://docs.microsoft.com/en-us/powershell/module/azurerm.keyvault/setazurermkeyvaultaccesspolicy
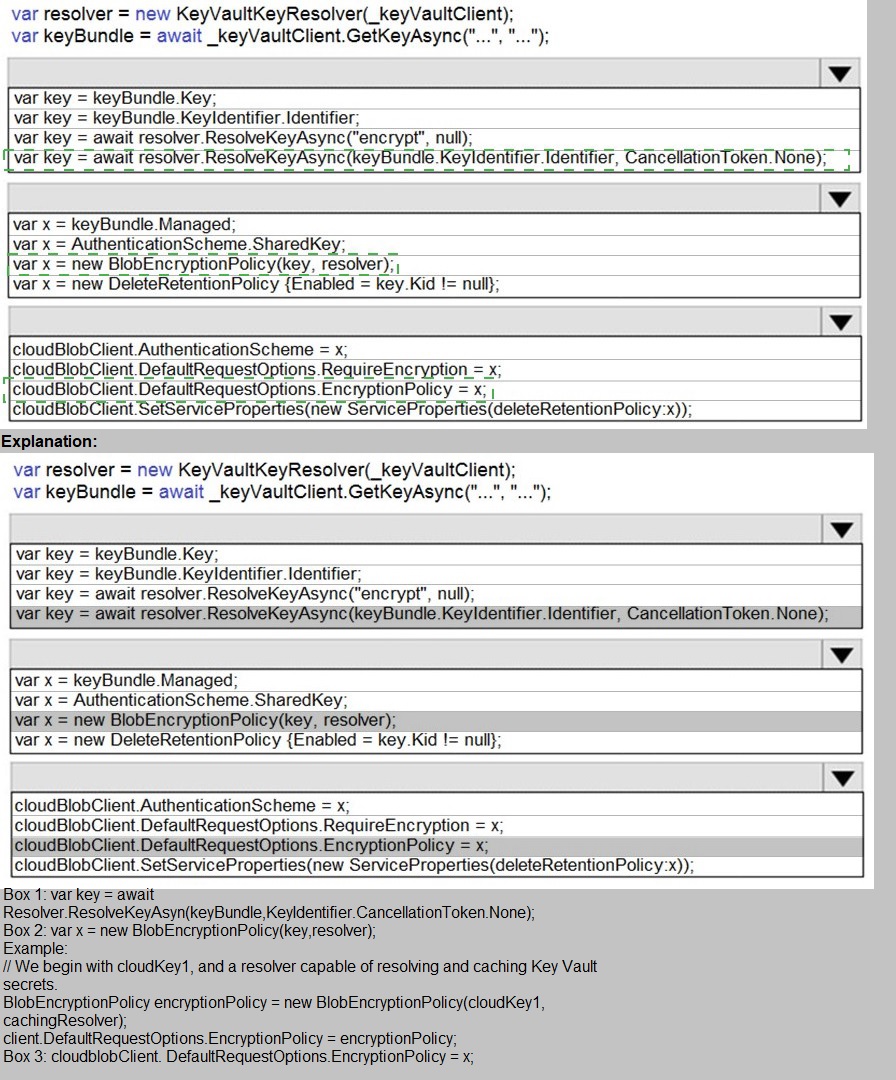
You need to add code at line PC26 of Processing.cs to ensure that security policies are
met.
How should you complete the code that you will add at line PC26? To answer, select the
appropriate options in the answer area.
NOTE: Each correct selection is worth one point.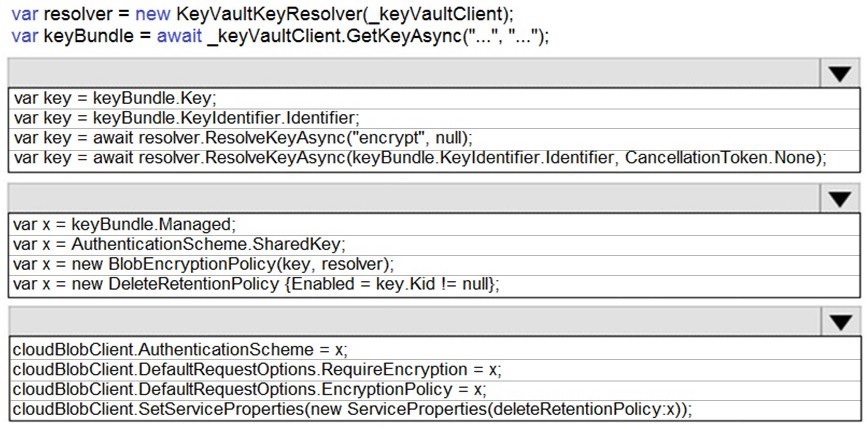
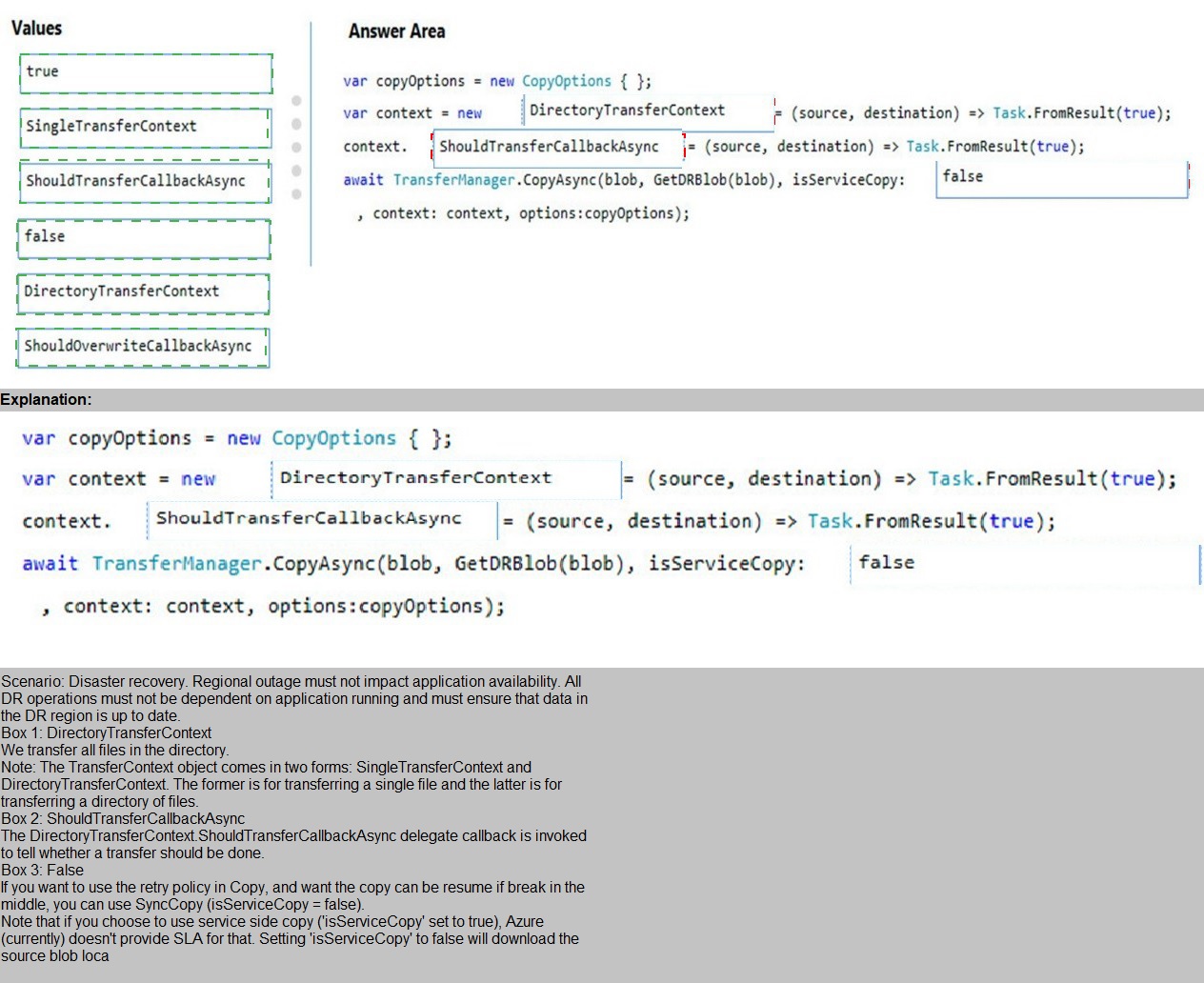
You need to ensure disaster recovery requirements are met.
What code should you add at line PC16? To answer, drag the appropriate code fragments to the correct locations. Each code
fragment may be used once, more than once, or not at all. You may need to drag the split bar between panes or scroll to view content.
NOTE: Each correct selection is worth one point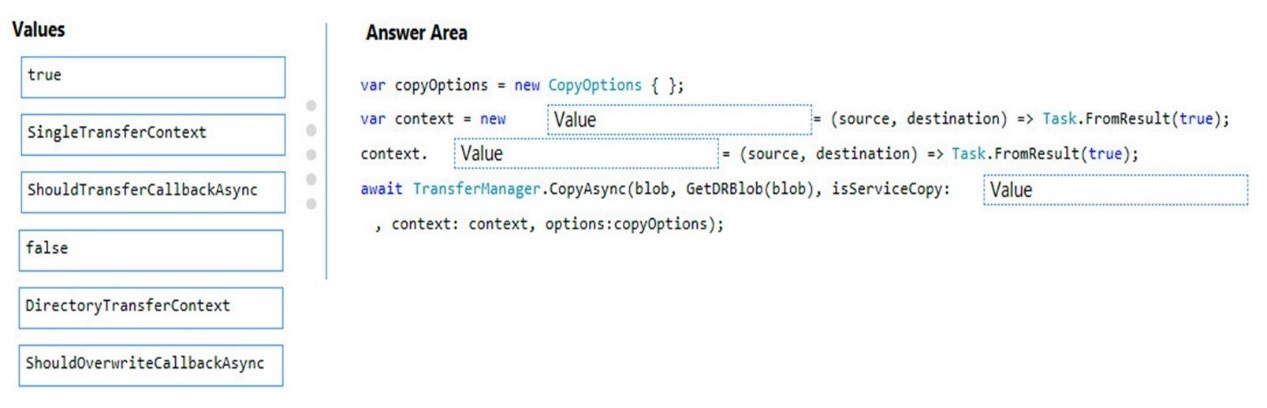
| Page 8 out of 28 Pages |