Topic 4, Misc. Questions
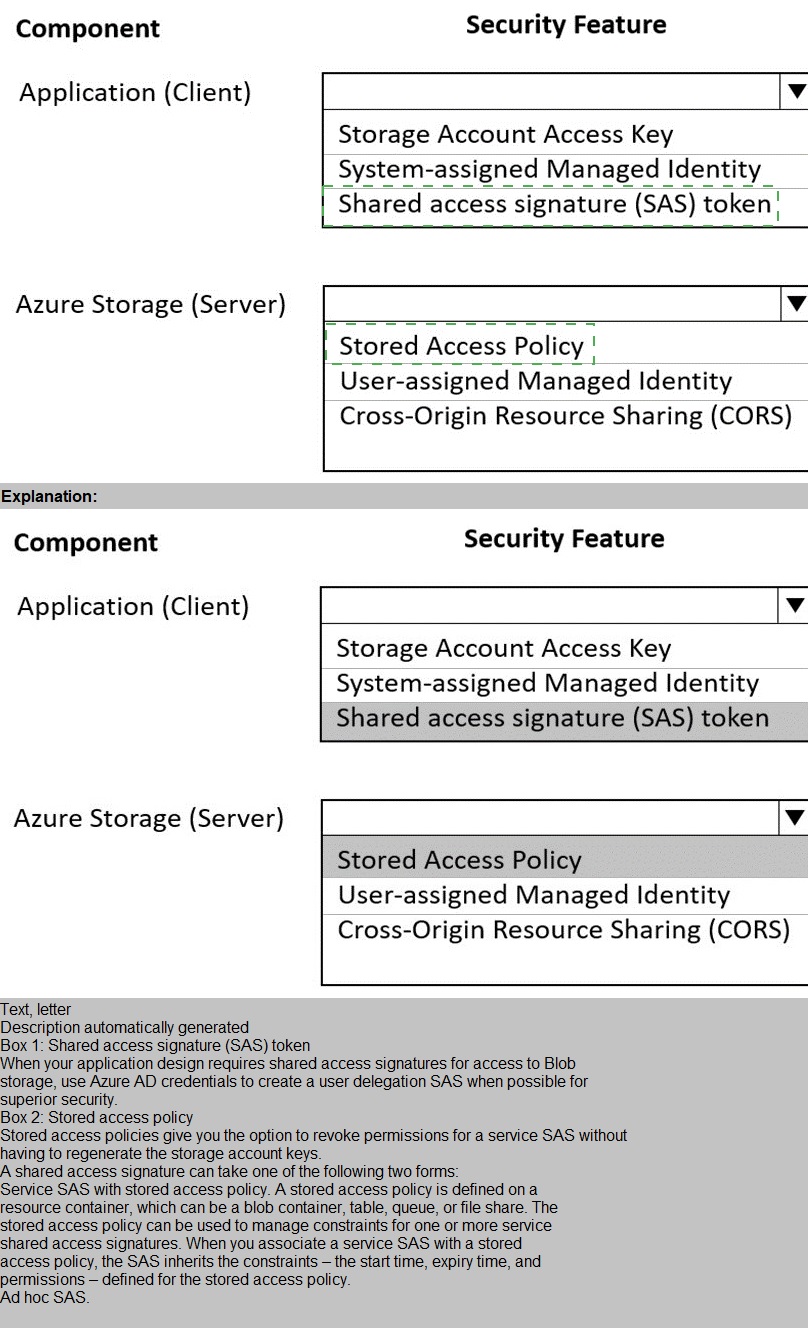
You are developing an application to store and retrieve data in Azure Blob storage. The
application will be hosted in an on-premises virtual machine (VM). The VM is connected to
Azure by using a Site-to-Site VPN gateway connection. The application is secured by using
Azure Active Directory (Azure AD) credentials.
The application must be granted access to the Azure Blob storage account with a start
time, expiry time, and read permissions. The Azure Blob storage account access must use
the Azure AD credentials of the application to secure data access. Data access must be
able to be revoked if the client application security is breached.
You need to secure the application access to Azure Blob storage.
Which security features should you use? To answer select the appropriate options in the
answer area.
NOTE: Each correct selection is worth one point.
You are configuring a new development environment for a Java application.
The environment requires a Virtual Machine Scale Set (VMSS), several storage accounts,
and networking components.
The VMSS must not be created until the storage accounts have been successfully created
and an associated load balancer and virtual network is configured.
How should you complete the Azure Resource Manager template? To answer, select the
appropriate options in the answer area.
NOTE: Each correct selection is worth one point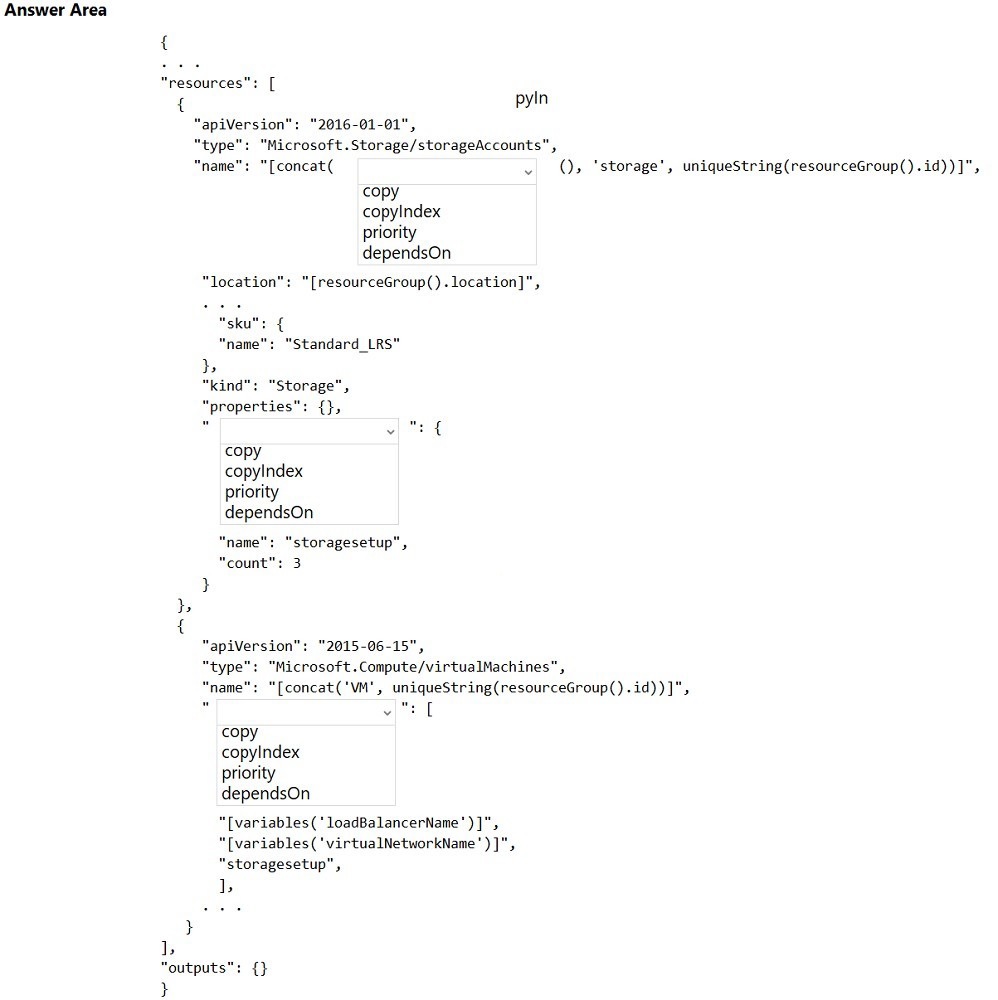
You have an existing Azure storage account that stores large volumes of data across
multiple containers.
You need to copy all data from the existing storage account to a new storage account. The
copy process must meet the following requirements:
Automate data movement.
Minimize user input required to perform the operation.
Ensure that the data movement process is recoverable.
What should you use?
A.
AzCopy
B.
Azure Storage Explorer
C.
Azure portal
D.
NET Storage Client Library
AzCopy
Explanation:
You can copy blobs, directories, and containers between storage accounts by using the
AzCopy v10 command-line utility.
The copy operation is synchronous so when the command returns, that indicates that all
files have been copied.
Reference:https://docs.microsoft.com/en-us/azure/storage/common/storage-use-azcopy-blobs-copy
You are developing a web application that uses Azure Cache for Redis. You anticipate that
the cache will frequently fill and that you will need to evict keys.
You must configure Azure Cache for Redis based on the following predicted usage pattern:
A small subset of elements will be accessed much more often than the rest.
You need to configure the Azure Cache for Redis to optimize performance for the predicted
usage pattern.
Which two eviction policies will achieve the goal?
NOTE: Each correct selection is worth one point.
A.
noeviction
B.
allkeys-lru
C.
volatile-lru
D.
allkeys-random
E.
volatile-ttl
F.
volatile-random
allkeys-lru
D.
allkeys-random
Explanation:
B: The allkeys-lru policy evict keys by trying to remove the less recently used (LRU) keys
first, in order to make space for the new data added. Use the allkeys-lru policy when you
expect a power-law distribution in the popularity of your requests, that is, you expect that a
subset of elements will be accessed far more often than the rest.
C: volatile-lru: evict keys by trying to remove the less recently used (LRU) keys first, but
only among keys that have an expire set, in order to make space for the new data added.
Note: The allkeys-lru policy is more memory efficient since there is no need to set an expire
for the key to be evicted under memory pressure.
Reference:
https://redis.io/topics/lru-cache
You are developing an Azure function that connects to an Azure SQL Database instance.
The function is triggered by an Azure Storage queue.
You receive reports of numerous System.InvalidOperationExceptions with the following
message: “Timeout expired. The timeout period elapsed prior to obtaining a connection
from the pool. This may have occurred because all pooled connections were in use and
max pool size was reached.”
You need to prevent the exception.
What should you do?
A.
In the host.json file, decrease the value of the batchSize option
B.
Convert the trigger to Azure Event Hub
C.
Convert the Azure Function to the Premium plan
D.
In the function.json file, change the value of the type option to queueScaling
In the host.json file, decrease the value of the batchSize option
Explanation:
With the Premium plan the max outbound connections per instance is unbounded
compared to the 600 active (1200 total) in a Consumption plan.
Note: The number of available connections is limited partly because a function app runs in
a sandbox environment. One of the restrictions that the sandbox imposes on your code is a
limit on the number of outbound connections, which is currently 600 active (1,200 total)
connections per instance. When you reach this limit, the functions runtime writes the
following message to the logs: Host thresholds exceeded: Connections.
Reference:
https://docs.microsoft.com/en-us/azure/azure-functions/manage-connections
https://docs.microsoft.com/en-us/azure/azure-functions/functions-scale#service-limits
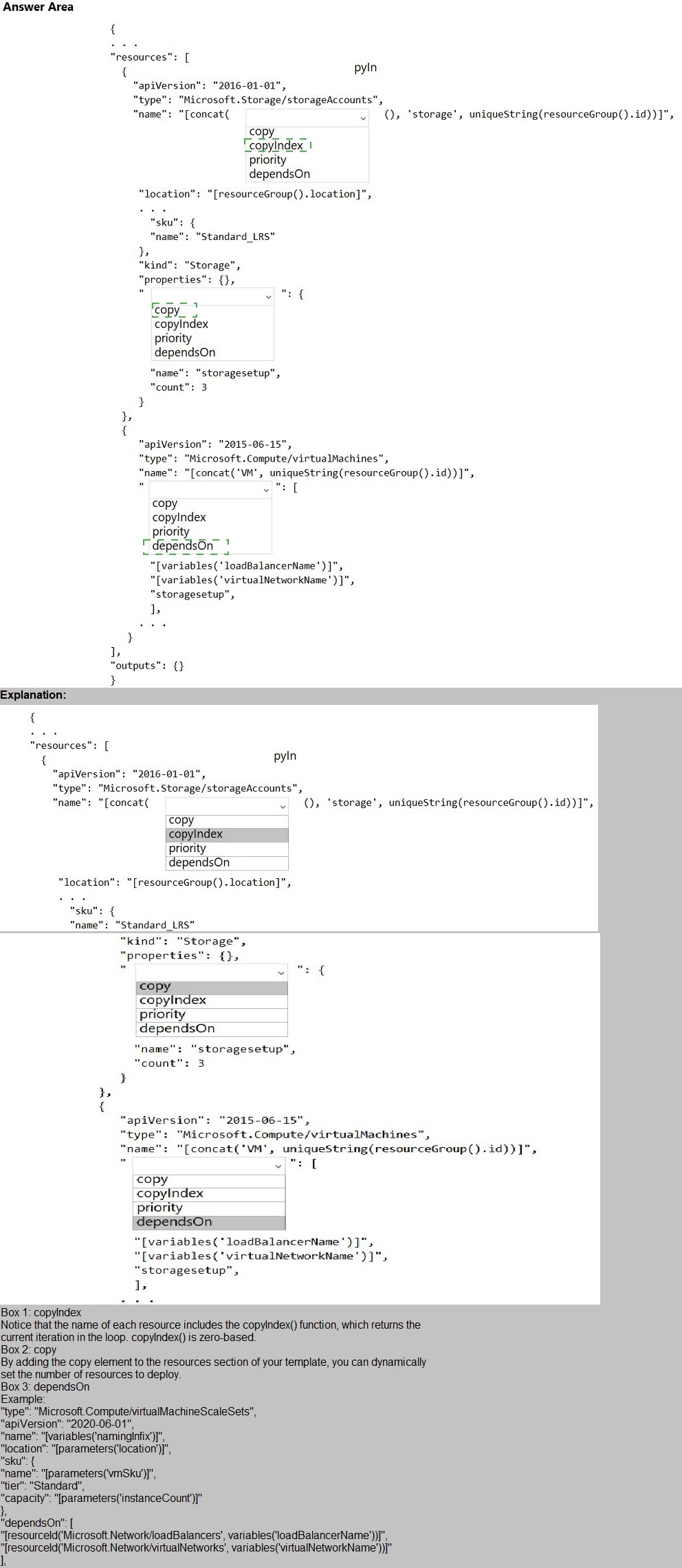
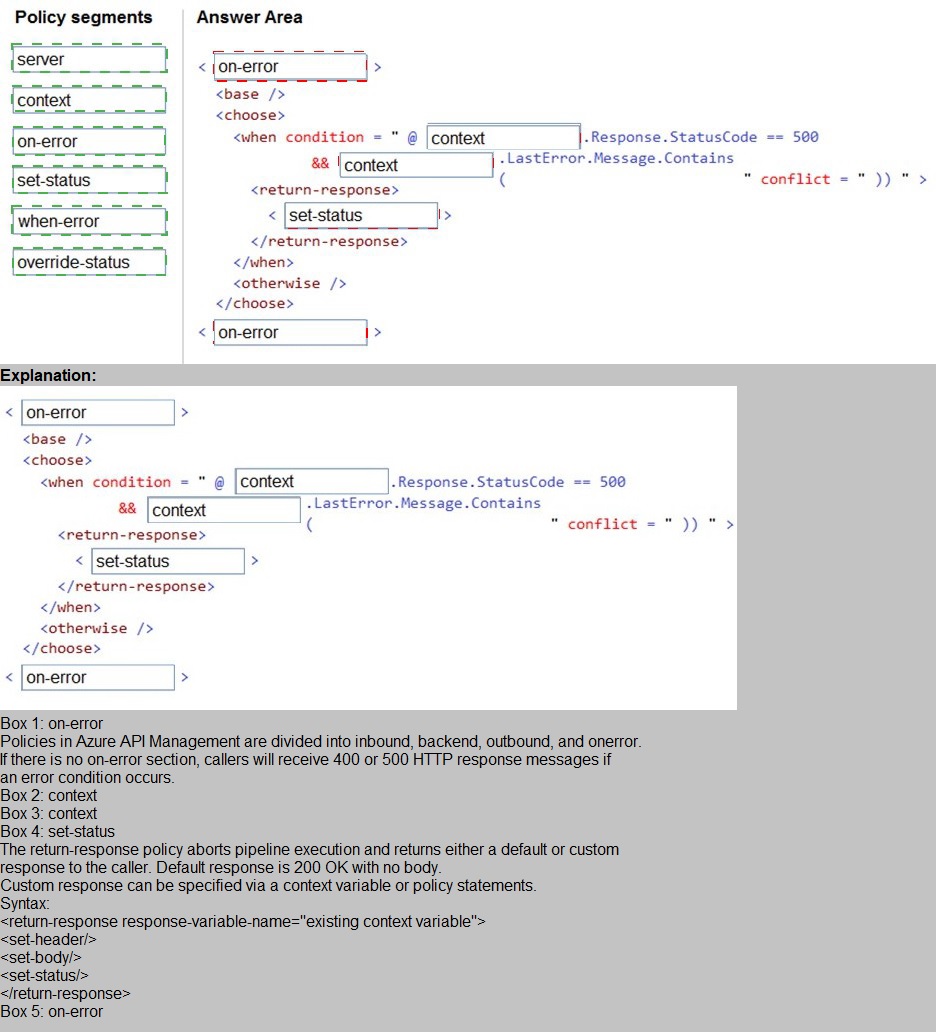
You are developing a REST web service. Customers will access the service by using an
Azure API Management instance.
The web service does not correctly handle conflicts. Instead of returning an HTTP status
code of 409, the service returns a status code of 500. The body of the status message
contains only the word conflict.
You need to ensure that conflicts produce the correct response.
How should you complete the policy? To answer, drag the appropriate code segments to
the correct locations. Each code segment may be used once, more than once, or not at all.
You may need to drag the split bar between panes or scroll to view content.
NOTE: Each correct selection is worth one point.
You are developing an ASP.NET Core time sheet application that runs as an Azure Web
App. Users of the application enter their time sheet information on the first day of every
month.
The application uses a third-party web service to validate data.
The application encounters periodic server errors due to errors that result from calling a
third-party web server. Each request to the third-party server has the same chance of
failure.
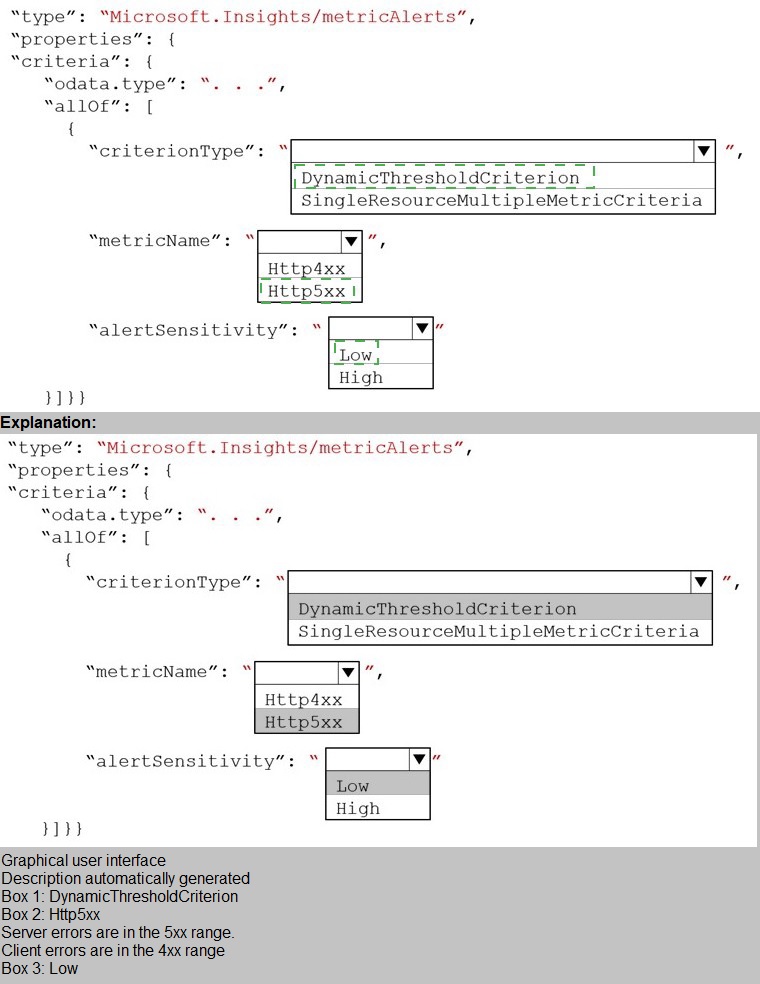
You need to configure an Azure Monitor alert to detect server errors unrelated to the thirdparty
service. You must minimize false-positive alerts.
How should you complete the Azure Resource Manager template? To answer, select the
appropriate options in the answer area.
NOTE: Each correct selection is worth one point.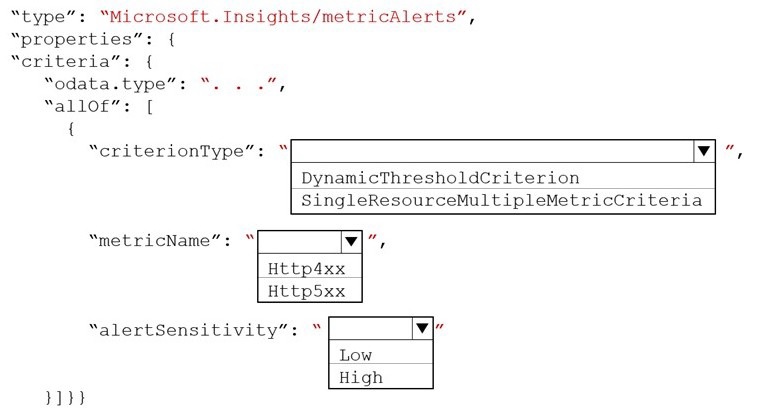
You develop and deploy an Azure App Service web app to a production environment. You
enable the Always On setting and the Application Insights site extensions. You deploy a
code update and receive multiple failed requests and exceptions in the web app. You need
to validate the performance and failure counts of the web app in near real time. Which
Application Insights tool should you use?
A.
Snapshot Debugger
B.
Profiler
C.
Smart Detection
D.
Live Metrics Stream
E.
Application Map
Smart Detection
You are developing an application to manage shipping information for cargo ships. The
application will use Azure Cosmos D8 for storage.
The application must run offline when ships are at sea The application must be connected
to Azure when ships are in port.
Which Azure Cosmos D8 API should you use for the application?
A.
Core
B.
MongoDe
C.
Cassandra
D.
Gremlin
Cassandra
Your company has several containers based on the following operating systems:
• Windows Server 2019 Nano Server
• Windows Server 2019 Server Core
• Windows Server 2022 Nano Server
• Windows Server 2022 Server Core
• Linux
You plan to migrate the containers to an Azure Kubernetes cluster. What is the minimum
number of node pools that the cluster must have?
A.
1
B.
2
C.
3
D.
6
3
| Page 4 out of 28 Pages |